- Page 2 and 3: Contents Feature Guest editorial, A
- Page 4 and 5: 2 costs will be such that decisions
- Page 6 and 7: 4 N sources 1 The delay along the p
- Page 8 and 9: 6 Sunday Monday Tuesday Wednesday T
- Page 10 and 11: BPS 800.000 8 700.000 600.000 500.0
- Page 12 and 13: 10 where the contributions from dif
- Page 14 and 15: 12 1.75 1.50 1.25 1.00 0.75 0.50 0.
- Page 16 and 17: 14 Table 2 Survey of some distribut
- Page 18 and 19: 16 0 Local calls mean: 27 sec. Std.
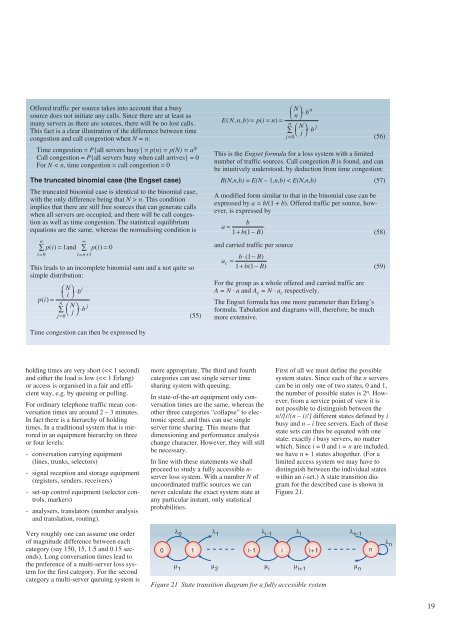
- Page 22 and 23: 20 j k λ ij µji λ ik µ ki λ ir
- Page 24 and 25: 22 14 Disturbed and shaped traffic
- Page 26 and 27: 24 200 184 150 100 50 0 25 26 27 28
- Page 28 and 29: 26 n * ooo---o A * M, V stream is n
- Page 30 and 31: 28 A-subscr. Network B-subscr. λ(
- Page 32 and 33: 30 Frame 6 Basic queuing model From
- Page 34 and 35: 32 Traffic sources (N) ⇒ III - -
- Page 36 and 37: 34 Since Gw (t) is the survivor fun
- Page 38 and 39: 36 - Mean response time depends onl
- Page 40 and 41: 38 Figure 38 Mixed international da
- Page 42 and 43: 40 3 Gaaren, S. LAN interconnection
- Page 44 and 45: 42 Solution of some problems in the
- Page 46 and 47: 44 Table 3 a. The “Loss” (in
- Page 48 and 49: 46 Table 6. (x = 3). a n 0.0 0.1 0.
- Page 50 and 51: 48 Telephone Systems” (published
- Page 52 and 53: 50 The life and work of Conny Palm
- Page 54 and 55: 52 mind that the seventies were bef
- Page 56 and 57: 54 of random traffic it is tacitly
- Page 58 and 59: 56 Architectures for the modelling
- Page 60 and 61: 58 QoS user Service catagories user
- Page 62 and 63: 60 (N)-service-user (N)-service-pro
- Page 64 and 65: 62 ACSE Presentation layer Session
- Page 66 and 67: 64 Traffic source 1 Traffic source
- Page 68 and 69: oth the traditional ack-based and t
- Page 70 and 71:
68 With this as a basis, some modif
- Page 72 and 73:
70 300 250 200 150 100 50 0 100 90
- Page 74 and 75:
72 Erl kErl 50 40 30 20 10 0 8 10 1
- Page 76 and 77:
74 Si: extreme high n s n s normal
- Page 78 and 79:
76 cost increase which must be cove
- Page 80 and 81:
78 with two to four hours read-out,
- Page 82 and 83:
80 Similarly as for Poisson-traffic
- Page 84 and 85:
82 throughput 1 Introduction Commun
- Page 86 and 87:
84 processor load Figure 4 its cust
- Page 88 and 89:
86 load control mechanisms. It is u
- Page 90 and 91:
88 ers to use the same facility at
- Page 92 and 93:
90 CE CE Figure 3 IRIM with cluster
- Page 94 and 95:
92 and one mini IRSU and one normal
- Page 96 and 97:
Table 4 Combined signalling and pac
- Page 98 and 99:
96 mission cost of large capacities
- Page 100 and 101:
40 30 20 10 98 TE-network TE-region
- Page 102 and 103:
100 change the routing for the next
- Page 104 and 105:
102 According to our plans reroutin
- Page 106 and 107:
104 Based on the experiences with t
- Page 108 and 109:
user access device 106 sound/speech
- Page 110 and 111:
108 overs for mobile stations that
- Page 112 and 113:
110 radio interface tion inside a b
- Page 114 and 115:
Figure 9 One way of defining space
- Page 116 and 117:
114 frequency code here. However, t
- Page 118 and 119:
116 class 1 class 2 class 3 [1,1,1]
- Page 120 and 121:
1.00E-00 1.00E-01 1.00E-02 case I c
- Page 122 and 123:
400 300 200 100 25 25 20 10 120 (a)
- Page 124 and 125:
Erlang Erlang Erlang 122 7 6 5 4 3
- Page 126 and 127:
124 Table 6 Call holding times (in
- Page 128 and 129:
Registered number of calls Register
- Page 130 and 131:
Table 9 Number of call attempts, su
- Page 132 and 133:
130 LAN Interconnection Traffic Mea
- Page 134 and 135:
132 gering table could be employed
- Page 136 and 137:
134 OSI name/layer 7) Application 6
- Page 138 and 139:
136 kbit/s 4000 3000 2000 1000 0 kb
- Page 140 and 141:
138 - The external LAN traffic is e
- Page 142 and 143:
Number of type 2 connections 140 Fe
- Page 144 and 145:
142 Number of type 2 connections No
- Page 146 and 147:
144 Number of type 2 connections Fi
- Page 148 and 149:
146 Preliminary studies indicate th
- Page 150 and 151:
148 Background Traffic Test Traffic
- Page 152 and 153:
150 ATM cell header 2.1.1 Measuring
- Page 154 and 155:
152 δ τ Figure 8 Deterministic in
- Page 156 and 157:
154 and CMR measurements was set to
- Page 158 and 159:
156 Sparc2 (SunOS 4.1.1) or Sparc10
- Page 160 and 161:
158 Segment size [byte] 8192 6144 4
- Page 162 and 163:
160 Throughput [Mbit/s] Throughput
- Page 164 and 165:
162 Segment size [byte] Unacknowled
- Page 166 and 167:
164 Throughput [Mbit/s] 30 20 4 kby
- Page 168 and 169:
166 Throughput [Mbit/s] Throughput
- Page 170 and 171:
168 TEL A TEL B Satellitedish Swiss
- Page 172 and 173:
170 Cell Discard Ratio Cell Discard
- Page 174 and 175:
172 Number of Type 2 Sources Number
- Page 176 and 177:
174 Synthetic load generation for A
- Page 178 and 179:
176 The type of the modulated proce
- Page 180 and 181:
178 Transp. Network LLC MAC PHY Tra
- Page 182 and 183:
180 0.005 0.004 0.003 0.002 0.001 0
- Page 184 and 185:
182 Number of active sources of the
- Page 186 and 187:
184 that these times are identicall
- Page 188 and 189:
186 Level duration The state sojour
- Page 190 and 191:
188 are summarised, before potentia
- Page 192 and 193:
190 Figure 4.4 Excerpt from the ATM
- Page 194 and 195:
192 4.2.6 Load extremes By specifyi
- Page 196 and 197:
194 14th international teletraffic
- Page 198 and 199:
196 how this change in “event rat
- Page 200 and 201:
advantage is that it is generally v
- Page 202 and 203:
200 ˜X = X + β(C − E(C)) (5.1)
- Page 204 and 205:
202 Table 3 Case 1: N = 4, λ/µ =
- Page 206 and 207:
204 A(t) 1 x - A on off Ti Pji Pij
- Page 208 and 209:
206 6.1.3 Control variables The num
- Page 210 and 211:
208 Some important queuing models f
- Page 212 and 213:
210 � � � A(ζ) � ζn �
- Page 214 and 215:
212 The main reason for giving (2.5
- Page 216 and 217:
214 M 0 0 1 For the sake of simplic
- Page 218 and 219:
216 cell-loss where I is the contou
- Page 220 and 221:
218 cell-loss 10 0 10 -1 10 -2 10 -
- Page 222 and 223:
220 Notes on a theorem of L. Takác
- Page 224 and 225:
222 and (25) (26) The parameters ck
- Page 226 and 227:
224
- Page 228 and 229:
226 Documents types that are prepar
- Page 230 and 231:
228 The rules for preparation and a
- Page 232 and 233:
230 Terminals/ Terminal Adapters
- Page 234 and 235:
232 plaintext Figure 1 The PNO Ciph