Contents Telektronikk - Telenor
Contents Telektronikk - Telenor
Contents Telektronikk - Telenor
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
26<br />
n *<br />
ooo---o<br />
A * M, V<br />
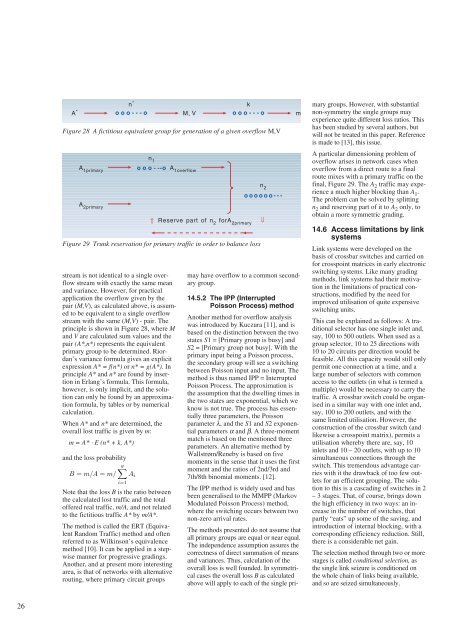
stream is not identical to a single overflow<br />
stream with exactly the same mean<br />
and variance. However, for practical<br />
application the overflow given by the<br />
pair (M,V), as calculated above, is assumed<br />
to be equivalent to a single overflow<br />
stream with the same (M,V) - pair. The<br />
principle is shown in Figure 28, where M<br />
and V are calculated sum values and the<br />
pair (A*,n*) represents the equivalent<br />
primary group to be determined. Riordan’s<br />
variance formula gives an explicit<br />
expression A* = f(n*) or n* = g(A*). In<br />
principle A* and n* are found by insertion<br />
in Erlang’s formula. This formula,<br />
however, is only implicit, and the solution<br />
can only be found by an approximation<br />
formula, by tables or by numerical<br />
calculation.<br />
When A* and n* are determined, the<br />
overall lost traffic is given by m:<br />
m = A* ⋅ E (n* + k, A*)<br />
and the loss probability<br />
g�<br />
B = m/A = m/<br />
Note that the loss B is the ratio between<br />
the calculated lost traffic and the total<br />
offered real traffic, m/A, and not related<br />
to the fictitious traffic A* by m/A*.<br />
The method is called the ERT (Equivalent<br />
Random Traffic) method and often<br />
referred to as Wilkinson’s equivalence<br />
method [10]. It can be applied in a stepwise<br />
manner for progressive gradings.<br />
Another, and at present more interesting<br />
area, is that of networks with alternative<br />
routing, where primary circuit groups<br />
k<br />
ooo---o m<br />
Figure 28 A fictitious equivalent group for generation of a given overflow M,V<br />
A 1primary<br />
A 2primary<br />
n 1<br />
ooo---o<br />
⇓<br />
A 1overflow<br />
Reserve part of n 2 forA 2primary<br />
Figure 29 Trunk reservation for primary traffic in order to balance loss<br />
i=1<br />
Ai<br />
n 2<br />
oooooo---<br />
may have overflow to a common secondary<br />
group.<br />
14.5.2 The IPP (Interrupted<br />
Poisson Process) method<br />
Another method for overflow analysis<br />
was introduced by Kuczura [11], and is<br />
based on the distinction between the two<br />
states S1 = [Primary group is busy] and<br />
S2 = [Primary group not busy]. With the<br />
primary input being a Poisson process,<br />
the secondary group will see a switching<br />
between Poisson input and no input. The<br />
method is thus named IPP = Interrupted<br />
Poisson Process. The approximation is<br />
the assumption that the dwelling times in<br />
the two states are exponential, which we<br />
know is not true. The process has essentially<br />
three parameters, the Poisson<br />
parameter λ, and the S1 and S2 exponential<br />
parameters α and β. A three-moment<br />
match is based on the mentioned three<br />
parameters. An alternative method by<br />
Wallstrøm/Reneby is based on five<br />
moments in the sense that it uses the first<br />
moment and the ratios of 2nd/3rd and<br />
7th/8th binomial moments. [12].<br />
The IPP method is widely used and has<br />
been generalised to the MMPP (Markov<br />
Modulated Poisson Process) method,<br />
where the switching occurs between two<br />
non-zero arrival rates.<br />
The methods presented do not assume that<br />
all primary groups are equal or near equal.<br />
The independence assumption assures the<br />
correctness of direct summation of means<br />
and variances. Thus, calculation of the<br />
overall loss is well founded. In symmetrical<br />
cases the overall loss B as calculated<br />
above will apply to each of the single pri-<br />
⇓<br />
mary groups. However, with substantial<br />
non-symmetry the single groups may<br />
experience quite different loss ratios. This<br />
has been studied by several authors, but<br />
will not be treated in this paper. Reference<br />
is made to [13], this issue.<br />
A particular dimensioning problem of<br />
overflow arises in network cases when<br />
overflow from a direct route to a final<br />
route mixes with a primary traffic on the<br />
final, Figure 29. The A2 traffic may experience<br />
a much higher blocking than A1 .<br />
The problem can be solved by splitting<br />
n2 and reserving part of it to A2 only, to<br />
obtain a more symmetric grading.<br />
14.6 Access limitations by link<br />
systems<br />
Link systems were developed on the<br />
basis of crossbar switches and carried on<br />
for crosspoint matrices in early electronic<br />
switching systems. Like many grading<br />
methods, link systems had their motivation<br />
in the limitations of practical constructions,<br />
modified by the need for<br />
improved utilisation of quite expensive<br />
switching units.<br />
This can be explained as follows: A traditional<br />
selector has one single inlet and,<br />
say, 100 to 500 outlets. When used as a<br />
group selector, 10 to 25 directions with<br />
10 to 20 circuits per direction would be<br />
feasible. All this capacity would still only<br />
permit one connection at a time, and a<br />
large number of selectors with common<br />
access to the outlets (in what is termed a<br />
multiple) would be necessary to carry the<br />
traffic. A crossbar switch could be organised<br />
in a similar way with one inlet and,<br />
say, 100 to 200 outlets, and with the<br />
same limited utilisation. However, the<br />
construction of the crossbar switch (and<br />
likewise a crosspoint matrix), permits a<br />
utilisation whereby there are, say, 10<br />
inlets and 10 – 20 outlets, with up to 10<br />
simultaneous connections through the<br />
switch. This tremendous advantage carries<br />
with it the drawback of too few outlets<br />
for an efficient grouping. The solution<br />
to this is a cascading of switches in 2<br />
– 3 stages. That, of course, brings down<br />
the high efficiency in two ways: an increase<br />
in the number of switches, that<br />
partly “eats” up some of the saving, and<br />
introduction of internal blocking, with a<br />
corresponding efficiency reduction. Still,<br />
there is a considerable net gain.<br />
The selection method through two or more<br />
stages is called conditional selection, as<br />
the single link seizure is conditioned on<br />
the whole chain of links being available,<br />
and so are seized simultaneously.