Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
News: Analysis<br />
For the past few years, Intel has moved<br />
away from the once-famous ‘tick-tock’<br />
scaling, where new processes were ‘ticks’<br />
and new architectures were ‘tocks’. It<br />
is switching to what the company calls<br />
‘hyperscaling’ advances, a new metaphor<br />
announced at the event to describe<br />
manufacturing advances. Intel will now<br />
use the ‘+’ and ‘++’ symbols to mark<br />
advances in the 14- and 10nm processes.<br />
Hyperscaling will help Intel cram new<br />
architectural and process innovations<br />
without hurrying a move to a new<br />
manufacturing process.<br />
New lithography techniques such<br />
as quad-patterning will help Intel take<br />
advantage of the economic benefits<br />
described by Moore’s Law, explained Kaizad<br />
Mistry, vice president and co-director of<br />
logic technology development at Intel. That<br />
will improve transistor density, which also<br />
brings performance and power-efficiency<br />
enhancements. Intel is projecting 15<br />
percent improvements in performance<br />
with each advance in the 10nm ‘+’ and ‘++’<br />
processes. Intel will also reduce the chip<br />
size to pack I/O, logic and SRAM blocks<br />
into a much smaller area.<br />
Intel is doing what the company calls<br />
“aggressive pitch scaling”, which involves<br />
packing wires, transistors and 3D fins closer<br />
together. On the 10nm process, that helps<br />
provide transistor density improvement that<br />
is 2.7 times better than the 14nm process.<br />
The chipmaker is also bringing the ability<br />
to mix and match different cores into an<br />
integrated system-on-chip. The cores could<br />
be made using different manufacturing<br />
processes. It’s also much how ARM chips are<br />
designed and made, a process that integrates<br />
CPUs, modems, graphics processors and<br />
other cores into a single chip. J<br />
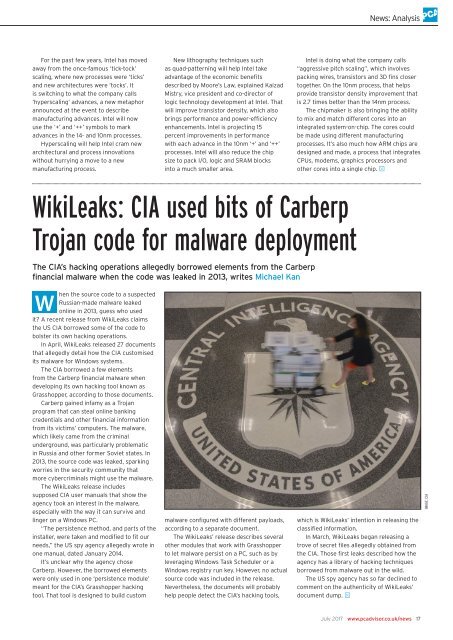
WikiLeaks: CIA used bits of Carberp<br />
Trojan code for malware deployment<br />
The CIA’s hacking operations allegedly borrowed elements from the Carberp<br />
financial malware when the code was leaked in 2013, writes Michael Kan<br />
W<br />
hen the source code to a suspected<br />
Russian-made malware leaked<br />
online in 2013, guess who used<br />
it? A recent release from WikiLeaks claims<br />
the US CIA borrowed some of the code to<br />
bolster its own hacking operations.<br />
In April, WikiLeaks released 27 documents<br />
that allegedly detail how the CIA customised<br />
its malware for Windows systems.<br />
The CIA borrowed a few elements<br />
from the Carberp financial malware when<br />
developing its own hacking tool known as<br />
Grasshopper, according to those documents.<br />
Carberp gained infamy as a Trojan<br />
program that can steal online banking<br />
credentials and other financial information<br />
from its victims’ computers. The malware,<br />
which likely came from the criminal<br />
underground, was particularly problematic<br />
in Russia and other former Soviet states. In<br />
2013, the source code was leaked, sparking<br />
worries in the security community that<br />
more cybercriminals might use the malware.<br />
The WikiLeaks release includes<br />
supposed CIA user manuals that show the<br />
agency took an interest in the malware,<br />
especially with the way it can survive and<br />
linger on a Windows <strong>PC</strong>.<br />
“The persistence method, and parts of the<br />
installer, were taken and modified to fit our<br />
needs,” the US spy agency allegedly wrote in<br />
one manual, dated January 2014.<br />
It’s unclear why the agency chose<br />
Carberp. However, the borrowed elements<br />
were only used in one ‘persistence module’<br />
meant for the CIA’s Grasshopper hacking<br />
tool. That tool is designed to build custom<br />
malware configured with different payloads,<br />
according to a separate document.<br />
The WikiLeaks’ release describes several<br />
other modules that work with Grasshopper<br />
to let malware persist on a <strong>PC</strong>, such as by<br />
leveraging Windows Task Scheduler or a<br />
Windows registry run key. However, no actual<br />
source code was included in the release.<br />
Nevertheless, the documents will probably<br />
help people detect the CIA’s hacking tools,<br />
which is WikiLeaks’ intention in releasing the<br />
classified information.<br />
In March, WikiLeaks began releasing a<br />
trove of secret files allegedly obtained from<br />
the CIA. Those first leaks described how the<br />
agency has a library of hacking techniques<br />
borrowed from malware out in the wild.<br />
The US spy agency has so far declined to<br />
comment on the authenticity of WikiLeaks’<br />
document dump. J<br />
IMAGE: CIA<br />
<strong>July</strong> <strong>2017</strong> www.pcadvisor.co.uk/news 17