You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
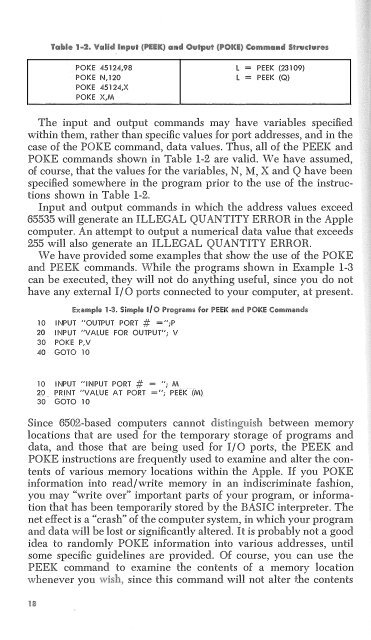
POKE 45124,98<br />
POKE N,120<br />
POKE 45124,X<br />
POKE X,M<br />
l = PEEK (23109)<br />
l = PEEK (Q)<br />
The input and output commands may have variables specified<br />
within them, rather than specific values for port addresses, and in the<br />
case of the POKE command, data values. Thus, all of the PEEK and<br />
POKE commands shown in Table 1-2 are valid. We have assumed,<br />
of course, that the values for the variables, N, M, X and Q have been<br />
specified somewhere in the program prior to the use of the instructions<br />
shown in Table 1-2.<br />
Input and output commands in which the address values exceed<br />
65535 will generate an ILLEGAL QUANTITY ERROR in the Apple<br />
computer. An attempt to output a numerical data value that exceeds<br />
255 will also generate an ILLEGAL QUANTITY ERROR.<br />
We have provided some examples that show the use of the POKE<br />
and PEEK commands. 'While the programs shown in Example 1-3<br />
can be executed, they will not do anything useful, since you do not<br />
have any external I/0 connected to your computer, at present.<br />
hample 1·3. 5imple D/O l'rnsrnm• for li'El"K mu! OK Commailcl•<br />
10 lf\IPUT "OUTPUT PORT # =";P<br />
20 lf\IPUT "VALUE FOR OUTPUT"; V<br />
30 POKE P,V<br />
40 GOTO 10<br />
10 lf\IPUT "INPUT PORT # = "; M<br />
20 _ PRl1'1T "VALUE AT PORT ="; PEEK-(M),<br />
30 GOTO 10<br />
Since 6502-based computers cannot<br />
between memory<br />
locations that are used for the temporary storage of programs and<br />
data, and those that are being used for I/ 0 ports, the PEEK and<br />
POKE instructions are frequently used to examine and alter the contents<br />
of various memory locations within the Apple. If you POKE<br />
information into read/write memory in an indiscriminate fashion,<br />
you may "write over" important parts of your program, or information<br />
that has been tempornrily stored by the BASIC interpreter. The<br />
net effect is a "crash" of the computer system, in which your program<br />
and data 'Nill be lost or significantly altered. It is probably not a good<br />
idea to randomly POKE information into various addresses, until<br />
some specific guidelines are provided. Of course, you can use the<br />
PEEK command to examine the contents of a memory location<br />
v1henever you since this command will not alter the contents