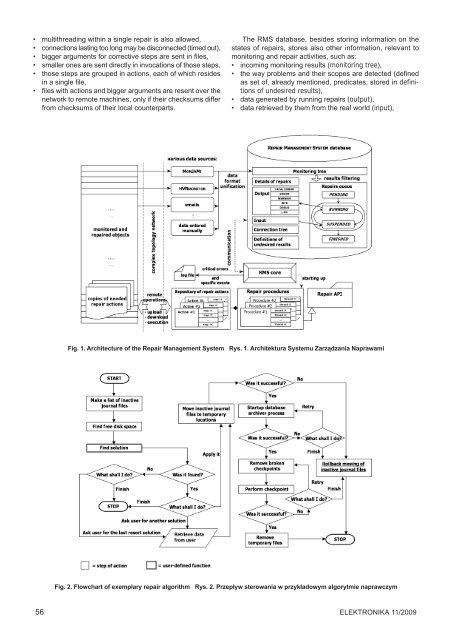
• multithreading within a single repair is also allowed, • connections lasting too long may be disconnected (timed out), • bigger arguments for corrective steps are sent in files, • smaller ones are sent directly in invocations of those steps, • those steps are grouped in actions, each of which resides in a single file, • files with actions and bigger arguments are resent over the network to remote machines, only if their checksums differ from checksums of their local counterparts. The RMS database, besides storing information on the states of repairs, stores also other information, relevant to monitoring and repair activities, such as: • incoming monitoring results (monitoring tree), • the way problems and their scopes are detected (defined as set of, already mentioned, predicates, stored in definitions of undesired results), • data generated by running repairs (output), • data retrieved by them from the real world (input), Fig. 1. Architecture of the Repair Management System Rys. 1. Architektura Systemu Zarządzania Naprawami Fig. 2. Flowchart of exemplary repair algorithm Rys. 2. Przepływ sterowania w przykładowym algorytmie naprawczym 56 ELEKTRONIKA 11/<strong>2009</strong>
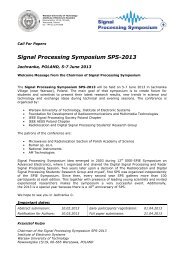
• data regarding their identity (details of repairs): their names, times their threads were started up and finished, PIDs (Process IDentifiers) of those threads, names of related scripts, with repair algorithms, binding repairs with scopes of problems triggering them, • information on making connections (with particular machines and as particular users) in the complex topology network, existing in the enterprise (connection tree). Case study of exemplary repair This subsection contains description and repair algorithm of exemplary problem. Brief description of the solved problem The examined problem is databases-related and may be characterized as follows: • each change in database is added to journal files (known also as redo log files), • once a day, after successful backup of the whole database (called here checkpoint) is made, journal files are deleted and their creation starts from scratch again, • creating and enlarging of the journal files is realized by a database archiver process, • lack of space in the filesystem, where those files exist, stops the database. Flowchart of the solution The way this problem is solved has been depicted in the Fig. 2. Conclusions The RMS and all other components of the RMF have been successfully implemented. Formal specifications of the RMM and the repair library formed the base for further development and left room for different implementations, sharing the same idea. The RMS with the prototype repair library (the repair API) are under tests in the Lufthansa Systems Poland Company. The API was implemented in the Perl programming language and the first experiments show that the system and its API meet the expectations of providing adequate support to the repair process. Experiments involved mentioned problem and its repair procedure which was easily implemented (using routines, derived from formal model), after representing it by a flowchart. Further experiments aiming at assessment of the effectiveness and efficiency of the RMS and benchmarking it with the traditional approaches are in the planning phase. Among expected benefits of the proposed approach are increase of reuse of repair procedures, better reliability of the repair process, significant increase of performance and better manageability due to improved documentation. The RMS incorporates existing monitoring systems and it is noticeable that repairs became faster, well-documented (so their results can be included in the internal reporting systems), and that administrators may focus on more complicated tasks. References [1] Škiljan, Z., Radič, B.: Monitoring systems: Concepts and tools. University Computing Centre, Croatia (2004). [2] Kamiński, M.: XML-based monitoring and its implementation in Perl. Proceedings of the 2nd National TPD Conference, Politechnika Poznańska Press, Poland (2007). [3] Kamiński, M.: HVRmonitor - data replication monitoring method. Proceedings of the 2nd AIS SIGSAND European Symposium on Systems Analysis and Design, University of Gdańsk Press, Poland (2007). [4] Barth, W.: Nagios. System and Network Monitoring. O’Reilly Press, USA (2006). [5] David, J.: Building a monitoring infrastructure with Nagios. Prentice-Hall, Great Britain (2007). [6] Turnbull, J.: Pro Nagios 2.0, Apress, USA (2006). [7] Zabbix reference manual: http://www.zabbix.com/documentation.php. [8] Zanikolas, S., Sakellariou, R.: A taxonomy of grid monitoring systems. School of Computer Science. The University of Manchester, Great Britain (2004). [9] Ceccanti, A., Panzieri, F.: Content-Based Monitoring in Grid Environments. Proceedings of the 13th IEEE International Workshops on Enabling Technologies. Department of Computer Science, University of Bologna, Italy (2004). [10] Jianwei, L., Hongbin, C., Pandeng, J., Meirong, C.: Design and Implementation of Grid Monitoring System Based on GMA. Proceedings of the 6th IEEE International Conference on Parallel and Distributed Computing. Applications and Technologies College of Computer Science, and University of Electronic Science and Technology. China (2006). [11] Cooke, A., Nutt, W., Magowan, J., Taylor, P., Leake, J., Byrom, R., Field, L., Hicks, S., Soni, M., Wilson, A., Cordenonsi, R., Cornwall, L., Djaoui, A., Fisher, S., Podhorszki, N., Coghlan, B., Kenny, S., O’Callaghan, D., Ryan, J.: Relational Grid Monitoring Architecture (R-GMA), Joint article published in GridPP. University of London, Great Britain (2003). [12] Campi, N., Bauer, K.: Automating Linux and Unix System Administration. Apress. USA (<strong>2009</strong>). [13] Strejcek, B.: Automate admin tasks with the powerful CFengine framework: http://www.linuxpromagazine.com/issues/<strong>2009</strong>/ 101/big_engine. [14] Gerlan, D., Schmerl, B.: Model-based Adaptation for Self-Healing Systems. School of Computer Science, Carnegie Mellon University, USA (2002). [15] Gerlan, D., Shang-Wen, C., Schmerl, B.: Increasing System Dependability through Architecture-based Self-repair, School of Computer Science, Carnegie Mellon University, USA (2003). [16] Gerlan, D., Shang-Wen, C., Schmerl, B., Sousa, J. P., Spitznagel, B., Steenkiste, P.: Using Architectural Style as a Basis for System Self-repair, School of Computer Science. Carnegie Mellon University, USA (2002). [17] Retkowski, G.: Building a Self-Healing Network: http://www.onlamp.com/pub/a/onlamp/2006/05/25/self-healing-networks.html. [18] Pervilä, M.: Using Nagios to monitor faults in a self-healing environment, Department of Computer Science, Helsinki University, Finland (2007). [19] Woodcock, J., Davies, J.: Using Z.: Specification, Refinement, and Proof, University of Oxford, Great Britain (1999). [20] Potter, B., Sinclair, J., Till, D.: An Introduction to Formal Specification and Z, International series in computer science, Prentice- Hall. Great Britain (1991). [21] Spivey, J.M.: The Z notation - A Reference Manual, Prentice- Hall. Great Britain (1992). [22] Kamiński, M.: Towards automating repairs of IT systems, article accepted (basing on its abstract) and submitted to the 30th International ISAT Conference (Information Systems., Architecture, and Technology). Poland (<strong>2009</strong>): http://www.isat.pwr.wroc.pl/. ELEKTRONIKA 11/<strong>2009</strong> 57
- Page 5 and 6:
konstrukcje technologie zastosowani
- Page 7 and 8:
Streszczenia artykułów • Summar
- Page 9 and 10: Streszczenia artykułów • Summar
- Page 11 and 12: Streszczenia artykułów • Summar
- Page 13 and 14: Medical pattern intelligent recogni
- Page 15 and 16: Fig. 2. Start graph Z and the set o
- Page 17 and 18: Both models are created of the basi
- Page 19 and 20: • in some cases in the methods of
- Page 21 and 22: 4. Random operators: three types of
- Page 23 and 24: useful. In work [1] is stressed, th
- Page 25 and 26: Tabl. 1. Fuzzy sets of the objects,
- Page 27 and 28: In addition, one has to remember th
- Page 29 and 30: The correction of digital images ob
- Page 31 and 32: Tabl. 4. MD error before and after
- Page 33 and 34: tionship then determines which indi
- Page 35 and 36: this goal. A user’s public key au
- Page 37 and 38: a) will be or could be broken, or b
- Page 39 and 40: Ontology-based approach to scada sy
- Page 41 and 42: erarchy of vulnerability classes wi
- Page 43 and 44: and the set of tasks is divided int
- Page 45 and 46: tasks: T 0 , T 4 , T 5 , T 6 and T
- Page 47 and 48: According to presented function CSF
- Page 49 and 50: The efficient data authentication i
- Page 51 and 52: Fig. 3. Example run of three rounds
- Page 53 and 54: Fig. 2. Possible scenarios of data
- Page 55 and 56: e necessary, in worst case - also s
- Page 57 and 58: dicates the number of tasks at the
- Page 59: • information on their state come
- Page 63 and 64: k = 1, 2, ..., m and m is the numbe
- Page 65 and 66: more powerful statistical (algorith
- Page 67 and 68: Signal to Noise Ratio (PSNR). We pr
- Page 69 and 70: [23] W3C - Web Services Glossary -
- Page 71 and 72: Associated with every N-point M-dim
- Page 73 and 74: The SMS-B system architecture (Sour
- Page 75 and 76: Technika próżni i technologie pr
- Page 77 and 78: wniosku i w konsekwencji za rok 200
- Page 79 and 80: Poniżej przedstawiono krótki kome
- Page 81 and 82: Wspomnienie Edward Leja (1937-2009)
- Page 83 and 84: Zastosowanie technik immunoenzymaty
- Page 85 and 86: z pasty węglowej, zaś odniesienia
- Page 87 and 88: [33] Biani A., Centi S. Tombrlli S.
- Page 89 and 90: Problemem bowiem w pracach instytut
- Page 91 and 92: 1985 - Zdzisław Dorywalski 1986 -
- Page 93 and 94: Rys. 4. Uroczyste wręczanie świad
- Page 95 and 96: Imię i Nazwisko Patenty Wzory uży
- Page 97 and 98: zadań określonych przez użytkown
- Page 99 and 100: Ocena sugerowanych w ankiecie metod
- Page 101: Zaprenumeruj wiedzę fachową 2010
- Page 104 and 105: Radary pasywne - nowa technika radi
- Page 106 and 107: c) stopniowo przesuwać jeden przeb
- Page 108 and 109: W przypadku wykorzystania nadajnika
- Page 110 and 111:
kreślić to, że owale Cassiniego
- Page 112 and 113:
Dla każdego kierunku odbieranej fa
- Page 114 and 115:
chomych, które w ogólnym przypadk
- Page 116 and 117:
Rys. 19. Fragment zobrazowania SS3
- Page 118 and 119:
Zbigniew Czekała jest projektantem
- Page 120 and 121:
• wytypowaniu statków zobowiąza
- Page 122 and 123:
• używanie właściwego osprzęt
- Page 124 and 125:
W jednomodowym szklanym włóknie t
- Page 126 and 127:
Światłowody scyntylacyjne W środ
- Page 128 and 129:
Parametry materiałowe szklanego w
- Page 130 and 131:
126 ELEKTRONIKA 11/2009
- Page 132 and 133:
Literatura [1] Yamane M., Asahara Y
- Page 134 and 135:
Rys.1. Przebiegi testowe na wyprowa
- Page 136 and 137:
nież pasmo emisji od około 500 MH