Download PDF - IBM Redbooks
Download PDF - IBM Redbooks
Download PDF - IBM Redbooks
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
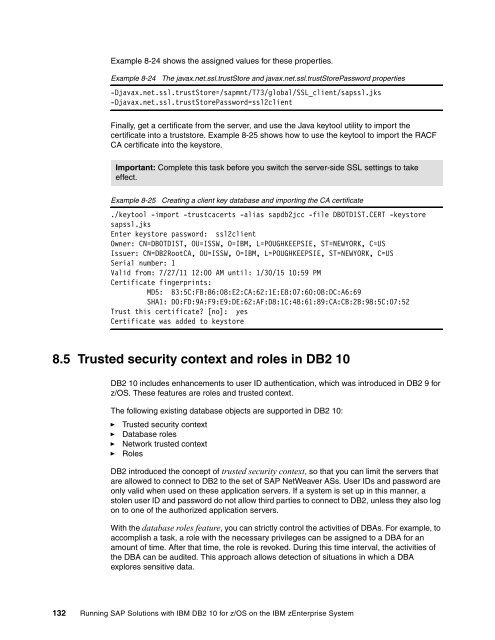
Example 8-24 shows the assigned values for these properties.<br />
Example 8-24 The javax.net.ssl.trustStore and javax.net.ssl.trustStorePassword properties<br />
-Djavax.net.ssl.trustStore=/sapmnt/T73/global/SSL_client/sapssl.jks<br />
-Djavax.net.ssl.trustStorePassword=ssl2client<br />
Finally, get a certificate from the server, and use the Java keytool utility to import the<br />
certificate into a truststore. Example 8-25 shows how to use the keytool to import the RACF<br />
CA certificate into the keystore.<br />
Important: Complete this task before you switch the server-side SSL settings to take<br />
effect.<br />
Example 8-25 Creating a client key database and importing the CA certificate<br />
./keytool -import -trustcacerts -alias sapdb2jcc -file DB0TDIST.CERT -keystore<br />
sapssl.jks<br />
Enter keystore password: ssl2client<br />
Owner: CN=DB0TDIST, OU=ISSW, O=<strong>IBM</strong>, L=POUGHKEEPSIE, ST=NEWYORK, C=US<br />
Issuer: CN=DB2RootCA, OU=ISSW, O=<strong>IBM</strong>, L=POUGHKEEPSIE, ST=NEWYORK, C=US<br />
Serial number: 1<br />
Valid from: 7/27/11 12:00 AM until: 1/30/15 10:59 PM<br />
Certificate fingerprints:<br />
MD5: B3:5C:FB:86:08:E2:CA:62:1E:E8:07:60:0B:DC:A6:69<br />
SHA1: D0:FD:9A:F9:E9:DE:62:AF:D8:1C:48:61:89:CA:CB:2B:98:5C:07:52<br />
Trust this certificate? [no]: yes<br />
Certificate was added to keystore<br />
8.5 Trusted security context and roles in DB2 10<br />
DB2 10 includes enhancements to user ID authentication, which was introduced in DB2 9 for<br />
z/OS. These features are roles and trusted context.<br />
The following existing database objects are supported in DB2 10:<br />
► Trusted security context<br />
► Database roles<br />
► Network trusted context<br />
► Roles<br />
DB2 introduced the concept of trusted security context, so that you can limit the servers that<br />
are allowed to connect to DB2 to the set of SAP NetWeaver ASs. User IDs and password are<br />
only valid when used on these application servers. If a system is set up in this manner, a<br />
stolen user ID and password do not allow third parties to connect to DB2, unless they also log<br />
on to one of the authorized application servers.<br />
With the database roles feature, you can strictly control the activities of DBAs. For example, to<br />
accomplish a task, a role with the necessary privileges can be assigned to a DBA for an<br />
amount of time. After that time, the role is revoked. During this time interval, the activities of<br />
the DBA can be audited. This approach allows detection of situations in which a DBA<br />
explores sensitive data.<br />
132 Running SAP Solutions with <strong>IBM</strong> DB2 10 for z/OS on the <strong>IBM</strong> zEnterprise System