fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Dynamic DNS configuration Configure the dynamically-addressed VPN peer<br />
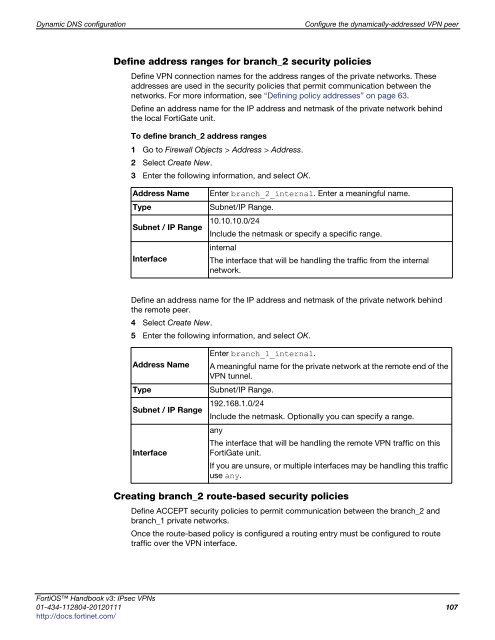
Define address ranges for branch_2 security policies<br />
Define VPN connection names for the address ranges of the private networks. These<br />
addresses are used in the security policies that permit communication between the<br />
networks. For more information, see “Defining policy addresses” on page 63.<br />
Define an address name for the IP address and netmask of the private network behind<br />
the local FortiGate unit.<br />
To define branch_2 address ranges<br />
1 Go to Firewall Objects > Address > Address.<br />
2 Select Create New.<br />
3 Enter the following information, and select OK.<br />
Address Name Enter branch_2_internal. Enter a meaningful name.<br />
Type Subnet/IP Range.<br />
Subnet / IP Range 10.10.10.0/24<br />
Include the netmask or specify a specific range.<br />
Interface<br />
internal<br />
The interface that will be handling the traffic from the internal<br />
network.<br />
Define an address name for the IP address and netmask of the private network behind<br />
the remote peer.<br />
4 Select Create New.<br />
5 Enter the following information, and select OK.<br />
Enter branch_1_internal.<br />
Address Name A meaningful name for the private network at the remote end of the<br />
VPN tunnel.<br />
Type Subnet/IP Range.<br />
Subnet / IP Range 192.168.1.0/24<br />
Include the netmask. Optionally you can specify a range.<br />
Interface<br />
any<br />
The interface that will be handling the remote VPN traffic on this<br />
FortiGate unit.<br />
If you are unsure, or multiple interfaces may be handling this traffic<br />
use any.<br />
Creating branch_2 route-based security policies<br />
Define ACCEPT security policies to permit communication between the branch_2 and<br />
branch_1 private networks.<br />
Once the route-based policy is configured a routing entry must be configured to route<br />
traffic over the VPN interface.<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 107<br />
http://docs.fortinet.com/