fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
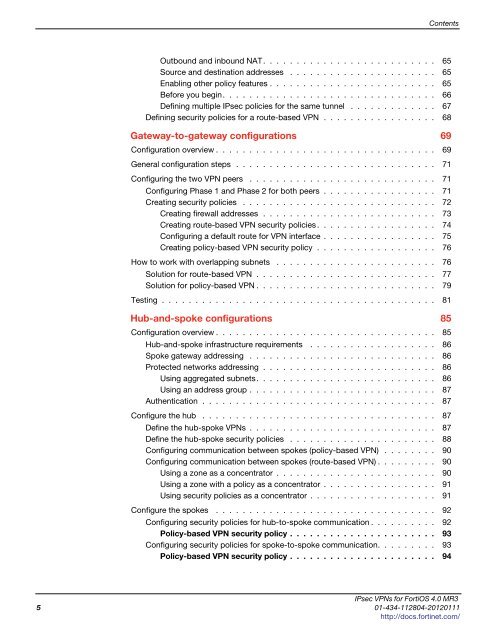
Contents<br />
Outbound and inbound NAT. . . . . . . . . . . . . . . . . . . . . . . . . . 65<br />
Source and destination addresses . . . . . . . . . . . . . . . . . . . . . . 65<br />
Enabling other policy features . . . . . . . . . . . . . . . . . . . . . . . . . 65<br />
Before you begin. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 66<br />
Defining multiple IPsec policies for the same tunnel . . . . . . . . . . . . . 67<br />
Defining security policies for a route-based VPN . . . . . . . . . . . . . . . . . 68<br />
Gateway-to-gateway configurations 69<br />
Configuration overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 69<br />
General configuration steps . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 71<br />
Configuring the two VPN peers . . . . . . . . . . . . . . . . . . . . . . . . . . . . 71<br />
Configuring Phase 1 and Phase 2 for both peers . . . . . . . . . . . . . . . . . 71<br />
Creating security policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72<br />
Creating firewall addresses . . . . . . . . . . . . . . . . . . . . . . . . . . 73<br />
Creating route-based VPN security policies . . . . . . . . . . . . . . . . . . 74<br />
Configuring a default route for VPN interface . . . . . . . . . . . . . . . . . 75<br />
Creating policy-based VPN security policy . . . . . . . . . . . . . . . . . . 76<br />
How to work with overlapping subnets . . . . . . . . . . . . . . . . . . . . . . . . 76<br />
Solution for route-based VPN . . . . . . . . . . . . . . . . . . . . . . . . . . . 77<br />
Solution for policy-based VPN . . . . . . . . . . . . . . . . . . . . . . . . . . . 79<br />
Testing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 81<br />
Hub-and-spoke configurations 85<br />
Configuration overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 85<br />
Hub-and-spoke infrastructure requirements . . . . . . . . . . . . . . . . . . . 86<br />
Spoke gateway addressing . . . . . . . . . . . . . . . . . . . . . . . . . . . . 86<br />
Protected networks addressing . . . . . . . . . . . . . . . . . . . . . . . . . . 86<br />
Using aggregated subnets. . . . . . . . . . . . . . . . . . . . . . . . . . . 86<br />
Using an address group . . . . . . . . . . . . . . . . . . . . . . . . . . . . 87<br />
Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 87<br />
Configure the hub . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 87<br />
Define the hub-spoke VPNs . . . . . . . . . . . . . . . . . . . . . . . . . . . . 87<br />
Define the hub-spoke security policies . . . . . . . . . . . . . . . . . . . . . . 88<br />
Configuring communication between spokes (policy-based VPN) . . . . . . . . 90<br />
Configuring communication between spokes (route-based VPN) . . . . . . . . . 90<br />
Using a zone as a concentrator . . . . . . . . . . . . . . . . . . . . . . . . 90<br />
Using a zone with a policy as a concentrator . . . . . . . . . . . . . . . . . 91<br />
Using security policies as a concentrator . . . . . . . . . . . . . . . . . . . 91<br />
Configure the spokes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 92<br />
Configuring security policies for hub-to-spoke communication . . . . . . . . . . 92<br />
Policy-based VPN security policy . . . . . . . . . . . . . . . . . . . . . . 93<br />
Configuring security policies for spoke-to-spoke communication. . . . . . . . . 93<br />
Policy-based VPN security policy . . . . . . . . . . . . . . . . . . . . . . 94<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
5 01-434-112804-20120111<br />
http://docs.fortinet.com/