fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Testing Dynamic DNS configuration<br />
Testing<br />
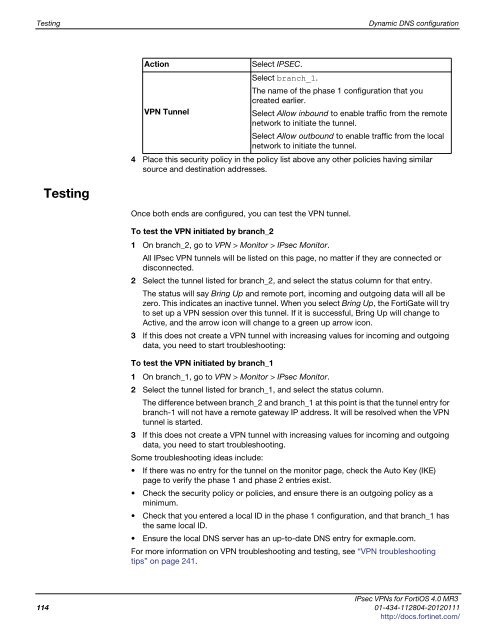
Action Select IPSEC.<br />
VPN Tunnel<br />
Select branch_1.<br />
The name of the phase 1 configuration that you<br />
created earlier.<br />
Select Allow inbound to enable traffic from the remote<br />
network to initiate the tunnel.<br />
Select Allow outbound to enable traffic from the local<br />
network to initiate the tunnel.<br />
4 Place this security policy in the policy list above any other policies having similar<br />
source and destination addresses.<br />
Once both ends are configured, you can test the VPN tunnel.<br />
To test the VPN initiated by branch_2<br />
1 On branch_2, go to VPN > Monitor > IPsec Monitor.<br />
All IPsec VPN tunnels will be listed on this page, no matter if they are connected or<br />
disconnected.<br />
2 Select the tunnel listed for branch_2, and select the status column for that entry.<br />
The status will say Bring Up and remote port, incoming and outgoing data will all be<br />
zero. This indicates an inactive tunnel. When you select Bring Up, the FortiGate will try<br />
to set up a VPN session over this tunnel. If it is successful, Bring Up will change to<br />
Active, and the arrow icon will change to a green up arrow icon.<br />
3 If this does not create a VPN tunnel with increasing values for incoming and outgoing<br />
data, you need to start troubleshooting:<br />
To test the VPN initiated by branch_1<br />
1 On branch_1, go to VPN > Monitor > IPsec Monitor.<br />
2 Select the tunnel listed for branch_1, and select the status column.<br />
The difference between branch_2 and branch_1 at this point is that the tunnel entry for<br />
branch-1 will not have a remote gateway IP address. It will be resolved when the VPN<br />
tunnel is started.<br />
3 If this does not create a VPN tunnel with increasing values for incoming and outgoing<br />
data, you need to start troubleshooting.<br />
Some troubleshooting ideas include:<br />
If there was no entry for the tunnel on the monitor page, check the Auto Key (IKE)<br />
page to verify the phase 1 and phase 2 entries exist.<br />
Check the security policy or policies, and ensure there is an outgoing policy as a<br />
minimum.<br />
Check that you entered a local ID in the phase 1 configuration, and that branch_1 has<br />
the same local ID.<br />
Ensure the local DNS server has an up-to-date DNS entry for exmaple.com.<br />
For more information on VPN troubleshooting and testing, see “VPN troubleshooting<br />
tips” on page 241.<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
114 01-434-112804-20120111<br />
http://docs.fortinet.com/