fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Hub-and-spoke configurations Dynamic spokes configuration example<br />
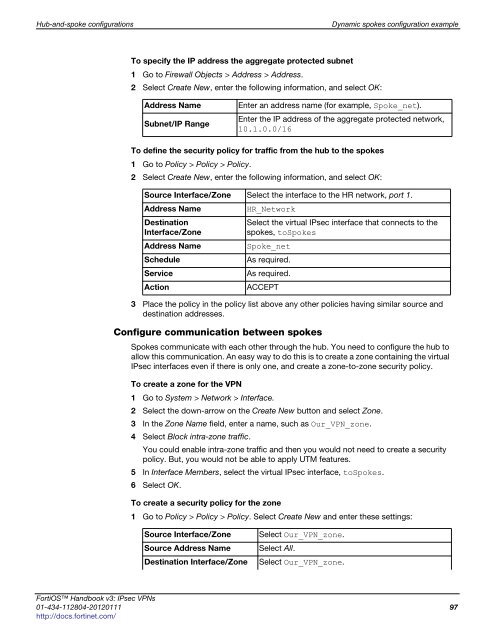
To specify the IP address the aggregate protected subnet<br />
1 Go to Firewall Objects > Address > Address.<br />
2 Select Create New, enter the following information, and select OK:<br />
Address Name Enter an address name (for example, Spoke_net).<br />
Subnet/IP Range<br />
To define the security policy for traffic from the hub to the spokes<br />
1 Go to Policy > Policy > Policy.<br />
2 Select Create New, enter the following information, and select OK:<br />
3 Place the policy in the policy list above any other policies having similar source and<br />
destination addresses.<br />
Configure communication between spokes<br />
Enter the IP address of the aggregate protected network,<br />
10.1.0.0/16<br />
Source Interface/Zone Select the interface to the HR network, port 1.<br />
Address Name HR_Network<br />
Destination<br />
Select the virtual IPsec interface that connects to the<br />
Interface/Zone<br />
spokes, toSpokes<br />
Address Name Spoke_net<br />
Schedule As required.<br />
Service As required.<br />
Action ACCEPT<br />
Spokes communicate with each other through the hub. You need to configure the hub to<br />
allow this communication. An easy way to do this is to create a zone containing the virtual<br />
IPsec interfaces even if there is only one, and create a zone-to-zone security policy.<br />
To create a zone for the VPN<br />
1 Go to System > Network > Interface.<br />
2 Select the down-arrow on the Create New button and select Zone.<br />
3 In the Zone Name field, enter a name, such as Our_VPN_zone.<br />
4 Select Block intra-zone traffic.<br />
You could enable intra-zone traffic and then you would not need to create a security<br />
policy. But, you would not be able to apply UTM features.<br />
5 In Interface Members, select the virtual IPsec interface, toSpokes.<br />
6 Select OK.<br />
To create a security policy for the zone<br />
1 Go to Policy > Policy > Policy. Select Create New and enter these settings:<br />
Source Interface/Zone Select Our_VPN_zone.<br />
Source Address Name Select All.<br />
Destination Interface/Zone Select Our_VPN_zone.<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 97<br />
http://docs.fortinet.com/