fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
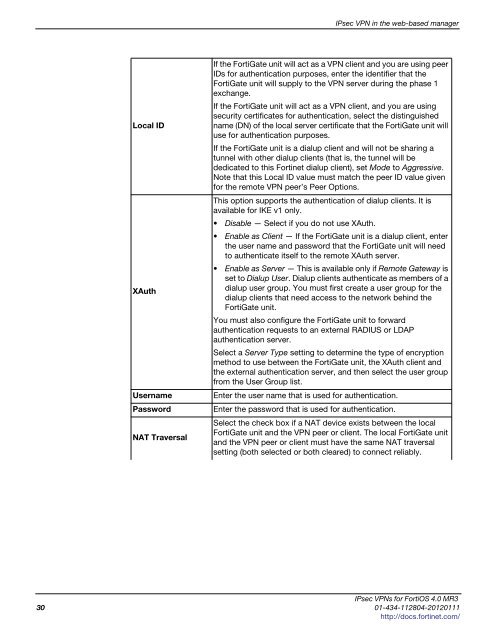
Local ID<br />
IPsec VPN in the web-based manager<br />
If the FortiGate unit will act as a VPN client and you are using peer<br />
IDs for authentication purposes, enter the identifier that the<br />
FortiGate unit will supply to the VPN server during the phase 1<br />
exchange.<br />
If the FortiGate unit will act as a VPN client, and you are using<br />
security certificates for authentication, select the distinguished<br />
name (DN) of the local server certificate that the FortiGate unit will<br />
use for authentication purposes.<br />
If the FortiGate unit is a dialup client and will not be sharing a<br />
tunnel with other dialup clients (that is, the tunnel will be<br />
dedicated to this Fortinet dialup client), set Mode to Aggressive.<br />
Note that this Local ID value must match the peer ID value given<br />
for the remote VPN peer’s Peer Options.<br />
This option supports the authentication of dialup clients. It is<br />
available for IKE v1 only.<br />
Disable — Select if you do not use XAuth.<br />
Enable as Client — If the FortiGate unit is a dialup client, enter<br />
the user name and password that the FortiGate unit will need<br />
to authenticate itself to the remote XAuth server.<br />
Enable as Server — This is available only if Remote Gateway is<br />
set to Dialup User. Dialup clients authenticate as members of a<br />
XAuth<br />
dialup user group. You must first create a user group for the<br />
dialup clients that need access to the network behind the<br />
FortiGate unit.<br />
You must also configure the FortiGate unit to forward<br />
authentication requests to an external RADIUS or LDAP<br />
authentication server.<br />
Select a Server Type setting to determine the type of encryption<br />
method to use between the FortiGate unit, the XAuth client and<br />
the external authentication server, and then select the user group<br />
from the User Group list.<br />
Username Enter the user name that is used for authentication.<br />
Password Enter the password that is used for authentication.<br />
NAT Traversal<br />
Select the check box if a NAT device exists between the local<br />
FortiGate unit and the VPN peer or client. The local FortiGate unit<br />
and the VPN peer or client must have the same NAT traversal<br />
setting (both selected or both cleared) to connect reliably.<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
30 01-434-112804-20120111<br />
http://docs.fortinet.com/