fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
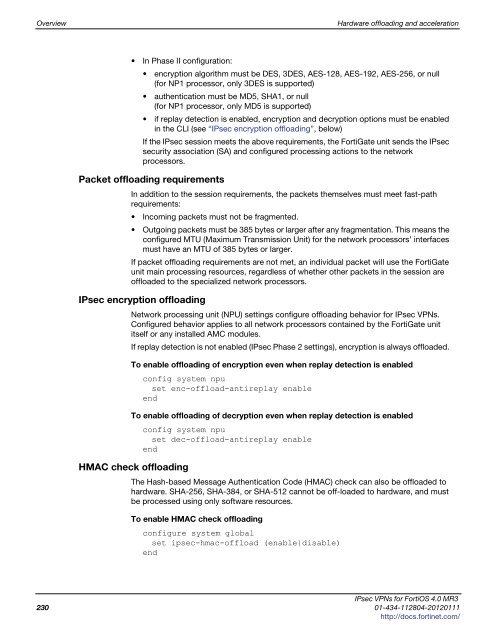
Overview Hardware offloading and acceleration<br />
In Phase II configuration:<br />
encryption algorithm must be DES, 3DES, AES-128, AES-192, AES-256, or null<br />
(for NP1 processor, only 3DES is supported)<br />
authentication must be MD5, SHA1, or null<br />
(for NP1 processor, only MD5 is supported)<br />
if replay detection is enabled, encryption and decryption options must be enabled<br />
in the CLI (see “IPsec encryption offloading”, below)<br />
If the IPsec session meets the above requirements, the FortiGate unit sends the IPsec<br />
security association (SA) and configured processing actions to the network<br />
processors.<br />
Packet offloading requirements<br />
In addition to the session requirements, the packets themselves must meet fast-path<br />
requirements:<br />
Incoming packets must not be fragmented.<br />
Outgoing packets must be 385 bytes or larger after any fragmentation. This means the<br />
configured MTU (Maximum Transmission Unit) for the network processors’ interfaces<br />
must have an MTU of 385 bytes or larger.<br />
If packet offloading requirements are not met, an individual packet will use the FortiGate<br />
unit main processing resources, regardless of whether other packets in the session are<br />
offloaded to the specialized network processors.<br />
IPsec encryption offloading<br />
Network processing unit (NPU) settings configure offloading behavior for IPsec VPNs.<br />
Configured behavior applies to all network processors contained by the FortiGate unit<br />
itself or any installed AMC modules.<br />
If replay detection is not enabled (IPsec Phase 2 settings), encryption is always offloaded.<br />
To enable offloading of encryption even when replay detection is enabled<br />
config system npu<br />
set enc-offload-antireplay enable<br />
end<br />
To enable offloading of decryption even when replay detection is enabled<br />
config system npu<br />
set dec-offload-antireplay enable<br />
end<br />
HMAC check offloading<br />
The Hash-based Message Authentication Code (HMAC) check can also be offloaded to<br />
hardware. SHA-256, SHA-384, or SHA-512 cannot be off-loaded to hardware, and must<br />
be processed using only software resources.<br />
To enable HMAC check offloading<br />
configure system global<br />
set <strong>ipsec</strong>-hmac-offload (enable|disable)<br />
end<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
230 01-434-112804-20120111<br />
http://docs.fortinet.com/