fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
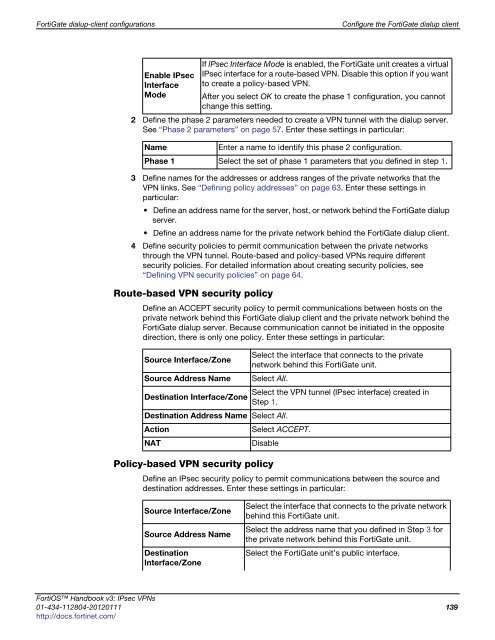
FortiGate dialup-client configurations Configure the FortiGate dialup client<br />
Enable IPsec<br />
Interface<br />
Mode<br />
2 Define the phase 2 parameters needed to create a VPN tunnel with the dialup server.<br />
See “Phase 2 parameters” on page 57. Enter these settings in particular:<br />
3 Define names for the addresses or address ranges of the private networks that the<br />
VPN links. See “Defining policy addresses” on page 63. Enter these settings in<br />
particular:<br />
Define an address name for the server, host, or network behind the FortiGate dialup<br />
server.<br />
Define an address name for the private network behind the FortiGate dialup client.<br />
4 Define security policies to permit communication between the private networks<br />
through the VPN tunnel. Route-based and policy-based VPNs require different<br />
security policies. For detailed information about creating security policies, see<br />
“Defining VPN security policies” on page 64.<br />
Route-based VPN security policy<br />
Define an ACCEPT security policy to permit communications between hosts on the<br />
private network behind this FortiGate dialup client and the private network behind the<br />
FortiGate dialup server. Because communication cannot be initiated in the opposite<br />
direction, there is only one policy. Enter these settings in particular:<br />
Policy-based VPN security policy<br />
If IPsec Interface Mode is enabled, the FortiGate unit creates a virtual<br />
IPsec interface for a route-based VPN. Disable this option if you want<br />
to create a policy-based VPN.<br />
After you select OK to create the phase 1 configuration, you cannot<br />
change this setting.<br />
Name Enter a name to identify this phase 2 configuration.<br />
Phase 1 Select the set of phase 1 parameters that you defined in step 1.<br />
Source Interface/Zone<br />
Select the interface that connects to the private<br />
network behind this FortiGate unit.<br />
Source Address Name Select All.<br />
Select the VPN tunnel (IPsec interface) created in<br />
Destination Interface/Zone<br />
Step 1.<br />
Destination Address Name Select All.<br />
Action Select ACCEPT.<br />
NAT Disable<br />
Define an IPsec security policy to permit communications between the source and<br />
destination addresses. Enter these settings in particular:<br />
Source Interface/Zone<br />
Source Address Name<br />
Destination<br />
Interface/Zone<br />
Select the interface that connects to the private network<br />
behind this FortiGate unit.<br />
Select the address name that you defined in Step 3 for<br />
the private network behind this FortiGate unit.<br />
Select the FortiGate unit’s public interface.<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 139<br />
http://docs.fortinet.com/