fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
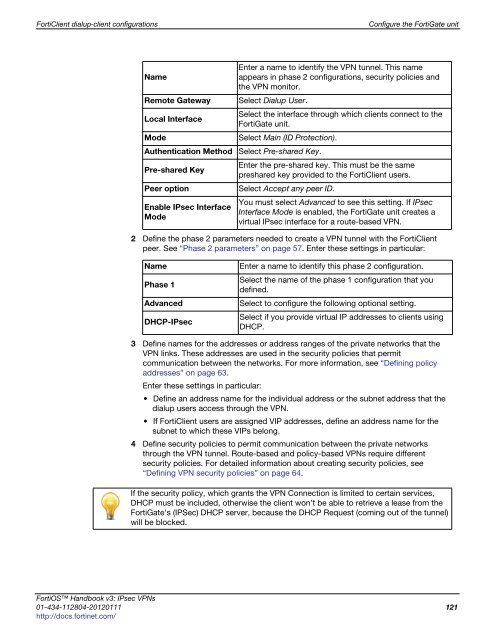
FortiClient dialup-client configurations Configure the FortiGate unit<br />
Enter a name to identify the VPN tunnel. This name<br />
Name<br />
appears in phase 2 configurations, security policies and<br />
the VPN monitor.<br />
Remote Gateway Select Dialup User.<br />
Local Interface<br />
Select the interface through which clients connect to the<br />
FortiGate unit.<br />
Mode Select Main (ID Protection).<br />
Authentication Method Select Pre-shared Key.<br />
Pre-shared Key<br />
Enter the pre-shared key. This must be the same<br />
preshared key provided to the FortiClient users.<br />
Peer option Select Accept any peer ID.<br />
Enable IPsec Interface<br />
Mode<br />
You must select Advanced to see this setting. If IPsec<br />
Interface Mode is enabled, the FortiGate unit creates a<br />
virtual IPsec interface for a route-based VPN.<br />
2 Define the phase 2 parameters needed to create a VPN tunnel with the FortiClient<br />
peer. See “Phase 2 parameters” on page 57. Enter these settings in particular:<br />
Name Enter a name to identify this phase 2 configuration.<br />
Phase 1<br />
Select the name of the phase 1 configuration that you<br />
defined.<br />
Advanced Select to configure the following optional setting.<br />
DHCP-IPsec<br />
Select if you provide virtual IP addresses to clients using<br />
DHCP.<br />
3 Define names for the addresses or address ranges of the private networks that the<br />
VPN links. These addresses are used in the security policies that permit<br />
communication between the networks. For more information, see “Defining policy<br />
addresses” on page 63.<br />
Enter these settings in particular:<br />
Define an address name for the individual address or the subnet address that the<br />
dialup users access through the VPN.<br />
If FortiClient users are assigned VIP addresses, define an address name for the<br />
subnet to which these VIPs belong.<br />
4 Define security policies to permit communication between the private networks<br />
through the VPN tunnel. Route-based and policy-based VPNs require different<br />
security policies. For detailed information about creating security policies, see<br />
“Defining VPN security policies” on page 64.<br />
If the security policy, which grants the VPN Connection is limited to certain services,<br />
DHCP must be included, otherwise the client won’t be able to retrieve a lease from the<br />
FortiGate’s (IPSec) DHCP server, because the DHCP Request (coming out of the tunnel)<br />
will be blocked.<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 121<br />
http://docs.fortinet.com/