fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
FortiClient dialup-client configuration example FortiClient dialup-client configurations<br />
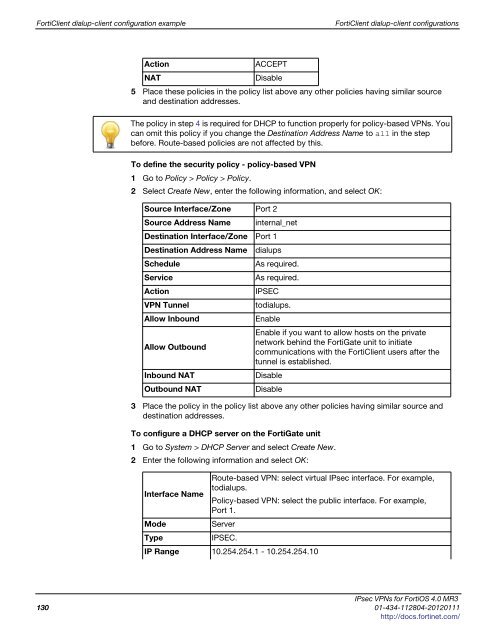
Action ACCEPT<br />
NAT Disable<br />
5 Place these policies in the policy list above any other policies having similar source<br />
and destination addresses.<br />
The policy in step 4 is required for DHCP to function properly for policy-based VPNs. You<br />
can omit this policy if you change the Destination Address Name to all in the step<br />
before. Route-based policies are not affected by this.<br />
To define the security policy - policy-based VPN<br />
1 Go to Policy > Policy > Policy.<br />
2 Select Create New, enter the following information, and select OK:<br />
Source Interface/Zone Port 2<br />
Source Address Name internal_net<br />
Destination Interface/Zone Port 1<br />
Destination Address Name dialups<br />
Schedule As required.<br />
Service As required.<br />
Action IPSEC<br />
VPN Tunnel todialups.<br />
Allow Inbound Enable<br />
Enable if you want to allow hosts on the private<br />
network behind the FortiGate unit to initiate<br />
Allow Outbound<br />
communications with the FortiClient users after the<br />
tunnel is established.<br />
Inbound NAT Disable<br />
Outbound NAT Disable<br />
3 Place the policy in the policy list above any other policies having similar source and<br />
destination addresses.<br />
To configure a DHCP server on the FortiGate unit<br />
1 Go to System > DHCP Server and select Create New.<br />
2 Enter the following information and select OK:<br />
Interface Name<br />
Route-based VPN: select virtual IPsec interface. For example,<br />
todialups.<br />
Policy-based VPN: select the public interface. For example,<br />
Port 1.<br />
Mode Server<br />
Type IPSEC.<br />
IP Range 10.254.254.1 - 10.254.254.10<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
130 01-434-112804-20120111<br />
http://docs.fortinet.com/