fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
L2TP and IPsec (Microsoft VPN) Troubleshooting<br />
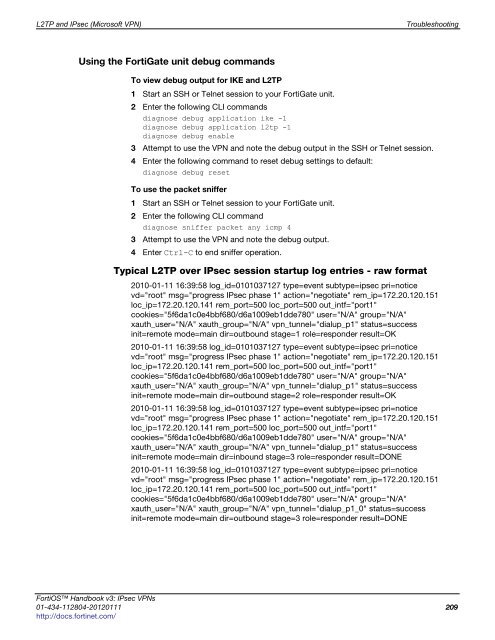
Using the FortiGate unit debug commands<br />
To view debug output for IKE and L2TP<br />
1 Start an SSH or Telnet session to your FortiGate unit.<br />
2 Enter the following CLI commands<br />
diagnose debug application ike -1<br />
diagnose debug application l2tp -1<br />
diagnose debug enable<br />
3 Attempt to use the VPN and note the debug output in the SSH or Telnet session.<br />
4 Enter the following command to reset debug settings to default:<br />
diagnose debug reset<br />
To use the packet sniffer<br />
1 Start an SSH or Telnet session to your FortiGate unit.<br />
2 Enter the following CLI command<br />
diagnose sniffer packet any icmp 4<br />
3 Attempt to use the VPN and note the debug output.<br />
4 Enter Ctrl-C to end sniffer operation.<br />
Typical L2TP over IPsec session startup log entries - raw format<br />
2010-01-11 16:39:58 log_id=0101037127 type=event subtype=<strong>ipsec</strong> pri=notice<br />
vd="root" msg="progress IPsec phase 1" action="negotiate" rem_ip=172.20.120.151<br />
loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_intf="port1"<br />
cookies="5f6da1c0e4bbf680/d6a1009eb1dde780" user="N/A" group="N/A"<br />
xauth_user="N/A" xauth_group="N/A" vpn_tunnel="dialup_p1" status=success<br />
init=remote mode=main dir=outbound stage=1 role=responder result=OK<br />
2010-01-11 16:39:58 log_id=0101037127 type=event subtype=<strong>ipsec</strong> pri=notice<br />
vd="root" msg="progress IPsec phase 1" action="negotiate" rem_ip=172.20.120.151<br />
loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_intf="port1"<br />
cookies="5f6da1c0e4bbf680/d6a1009eb1dde780" user="N/A" group="N/A"<br />
xauth_user="N/A" xauth_group="N/A" vpn_tunnel="dialup_p1" status=success<br />
init=remote mode=main dir=outbound stage=2 role=responder result=OK<br />
2010-01-11 16:39:58 log_id=0101037127 type=event subtype=<strong>ipsec</strong> pri=notice<br />
vd="root" msg="progress IPsec phase 1" action="negotiate" rem_ip=172.20.120.151<br />
loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_intf="port1"<br />
cookies="5f6da1c0e4bbf680/d6a1009eb1dde780" user="N/A" group="N/A"<br />
xauth_user="N/A" xauth_group="N/A" vpn_tunnel="dialup_p1" status=success<br />
init=remote mode=main dir=inbound stage=3 role=responder result=DONE<br />
2010-01-11 16:39:58 log_id=0101037127 type=event subtype=<strong>ipsec</strong> pri=notice<br />
vd="root" msg="progress IPsec phase 1" action="negotiate" rem_ip=172.20.120.151<br />
loc_ip=172.20.120.141 rem_port=500 loc_port=500 out_intf="port1"<br />
cookies="5f6da1c0e4bbf680/d6a1009eb1dde780" user="N/A" group="N/A"<br />
xauth_user="N/A" xauth_group="N/A" vpn_tunnel="dialup_p1_0" status=success<br />
init=remote mode=main dir=outbound stage=3 role=responder result=DONE<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 209<br />
http://docs.fortinet.com/