fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
IPsec VPN Overview Planning your VPN<br />
Network topologies<br />
which VPN devices to include in the configuration<br />
through which interfaces the VPN devices communicate<br />
through which interfaces do private networks access the VPN gateways<br />
Once you have this information, you can select a VPN topology that meets the<br />
requirements of your situation.<br />
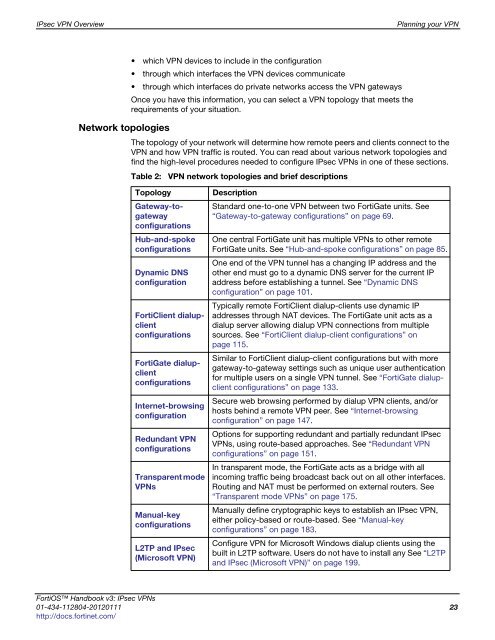
The topology of your network will determine how remote peers and clients connect to the<br />
VPN and how VPN traffic is routed. You can read about various network topologies and<br />
find the high-level procedures needed to configure IPsec VPNs in one of these sections.<br />
Table 2: VPN network topologies and brief descriptions<br />
Topology Description<br />
Gateway-togateway<br />
configurations<br />
Hub-and-spoke<br />
configurations<br />
Dynamic DNS<br />
configuration<br />
FortiClient dialupclient<br />
configurations<br />
FortiGate dialupclient<br />
configurations<br />
Internet-browsing<br />
configuration<br />
Redundant VPN<br />
configurations<br />
Transparent mode<br />
VPNs<br />
Manual-key<br />
configurations<br />
L2TP and IPsec<br />
(Microsoft VPN)<br />
Standard one-to-one VPN between two FortiGate units. See<br />
“Gateway-to-gateway configurations” on page 69.<br />
One central FortiGate unit has multiple VPNs to other remote<br />
FortiGate units. See “Hub-and-spoke configurations” on page 85.<br />
One end of the VPN tunnel has a changing IP address and the<br />
other end must go to a dynamic DNS server for the current IP<br />
address before establishing a tunnel. See “Dynamic DNS<br />
configuration” on page 101.<br />
Typically remote FortiClient dialup-clients use dynamic IP<br />
addresses through NAT devices. The FortiGate unit acts as a<br />
dialup server allowing dialup VPN connections from multiple<br />
sources. See “FortiClient dialup-client configurations” on<br />
page 115.<br />
Similar to FortiClient dialup-client configurations but with more<br />
gateway-to-gateway settings such as unique user authentication<br />
for multiple users on a single VPN tunnel. See “FortiGate dialupclient<br />
configurations” on page 133.<br />
Secure web browsing performed by dialup VPN clients, and/or<br />
hosts behind a remote VPN peer. See “Internet-browsing<br />
configuration” on page 147.<br />
Options for supporting redundant and partially redundant IPsec<br />
VPNs, using route-based approaches. See “Redundant VPN<br />
configurations” on page 151.<br />
In transparent mode, the FortiGate acts as a bridge with all<br />
incoming traffic being broadcast back out on all other interfaces.<br />
Routing and NAT must be performed on external routers. See<br />
“Transparent mode VPNs” on page 175.<br />
Manually define cryptographic keys to establish an IPsec VPN,<br />
either policy-based or route-based. See “Manual-key<br />
configurations” on page 183.<br />
Configure VPN for Microsoft Windows dialup clients using the<br />
built in L2TP software. Users do not have to install any See “L2TP<br />
and IPsec (Microsoft VPN)” on page 199.<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 23<br />
http://docs.fortinet.com/