fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Configuring the FortiGate unit GRE over IPsec (Cisco VPN) configurations<br />
Configuring the FortiGate unit<br />
There are several steps to the GRE-over-IPsec configuration:<br />
Enable overlapping subnets. This is needed because the IPsec and GRE tunnels will<br />
use the same addresses.<br />
Configure a route-based IPsec VPN on the external interface.<br />
Configure a GRE tunnel on the virtual IPsec interface. Set its local gateway and<br />
remote gateway addresses to match the local and remote gateways of the IPsec<br />
tunnel.<br />
Configure security policies to allow traffic to pass in both directions between the GRE<br />
virtual interface and the IPsec virtual interface.<br />
Configure security policies to allow traffic to pass in both directions between the<br />
protected network interface and the GRE virtual interface.<br />
Configure a static route to direct traffic destined for the network behind the Cisco<br />
router into the GRE-over-IPsec tunnel.<br />
Enabling overlapping subnets<br />
By default, each FortiGate unit network interface must be on a separate network. The<br />
configuration described in this chapter assigns an IPsec tunnel end point and the<br />
external interface to the same network. Enable subnet overlap as follows:<br />
config system settings<br />
set allow-subnet-overlap enable<br />
end<br />
Configuring the IPsec VPN<br />
A route-based VPN is required. It must use encryption and authentication algorithms<br />
compatible with the Cisco equipment to which it connects. In this chapter, preshared key<br />
authentication is shown.<br />
To configure the IPsec VPN - web-based manager<br />
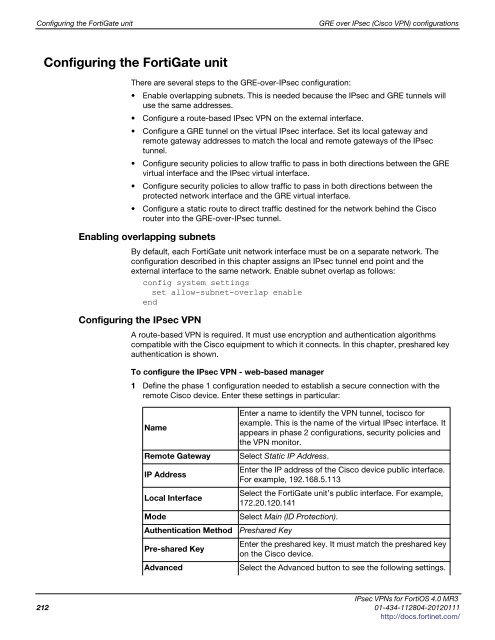
1 Define the phase 1 configuration needed to establish a secure connection with the<br />
remote Cisco device. Enter these settings in particular:<br />
Enter a name to identify the VPN tunnel, tocisco for<br />
example. This is the name of the virtual IPsec interface. It<br />
Name<br />
appears in phase 2 configurations, security policies and<br />
the VPN monitor.<br />
Remote Gateway Select Static IP Address.<br />
IP Address<br />
Enter the IP address of the Cisco device public interface.<br />
For example, 192.168.5.113<br />
Local Interface<br />
Select the FortiGate unit’s public interface. For example,<br />
172.20.120.141<br />
Mode Select Main (ID Protection).<br />
Authentication Method Preshared Key<br />
Pre-shared Key<br />
Enter the preshared key. It must match the preshared key<br />
on the Cisco device.<br />
Advanced Select the Advanced button to see the following settings.<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
212 01-434-112804-20120111<br />
http://docs.fortinet.com/