fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Dynamic DNS configuration Configure the dynamically-addressed VPN peer<br />
6 Optionally configure any other security policy settings you require such as UTM or<br />
traffic shaping for this policy.<br />
7 Place these policies in the policy list above any other policies having similar source<br />
and destination addresses. This will ensure VPN traffic is matched against the VPN<br />
policies before any other policies.<br />
To create routing entry for VPN interface - CLI<br />
config router static<br />
edit 5<br />
set dst 0.0.0.0 0.0.0.0<br />
set dynamic-dateway enable<br />
set device wan1<br />
next<br />
end<br />
This routing entry must be added in the CLI because the dynamic-gateway option is not<br />
available in the web-based manager.<br />
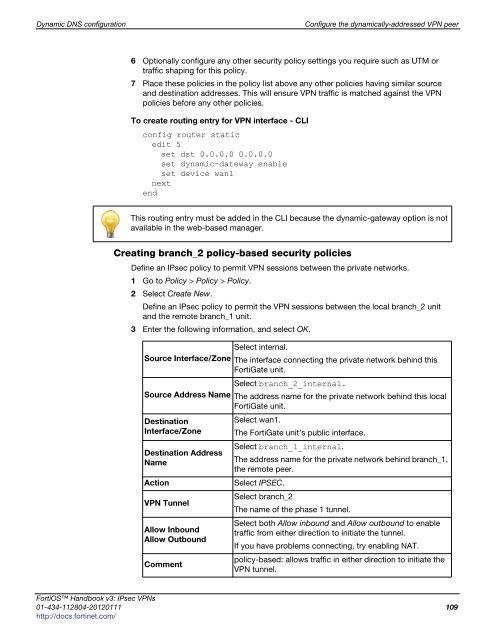
Creating branch_2 policy-based security policies<br />
Define an IPsec policy to permit VPN sessions between the private networks.<br />
1 Go to Policy > Policy > Policy.<br />
2 Select Create New.<br />
Define an IPsec policy to permit the VPN sessions between the local branch_2 unit<br />
and the remote branch_1 unit.<br />
3 Enter the following information, and select OK.<br />
Select internal.<br />
Source Interface/Zone The interface connecting the private network behind this<br />
FortiGate unit.<br />
Select branch_2_internal.<br />
Source Address Name The address name for the private network behind this local<br />
FortiGate unit.<br />
Destination<br />
Interface/Zone<br />
Select wan1.<br />
The FortiGate unit’s public interface.<br />
Destination Address<br />
Name<br />
Select branch_1_internal.<br />
The address name for the private network behind branch_1,<br />
the remote peer.<br />
Action Select IPSEC.<br />
VPN Tunnel<br />
Allow Inbound<br />
Allow Outbound<br />
Comment<br />
Select branch_2<br />
The name of the phase 1 tunnel.<br />
Select both Allow inbound and Allow outbound to enable<br />
traffic from either direction to initiate the tunnel.<br />
If you have problems connecting, try enabling NAT.<br />
policy-based: allows traffic in either direction to initiate the<br />
VPN tunnel.<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 109<br />
http://docs.fortinet.com/