fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
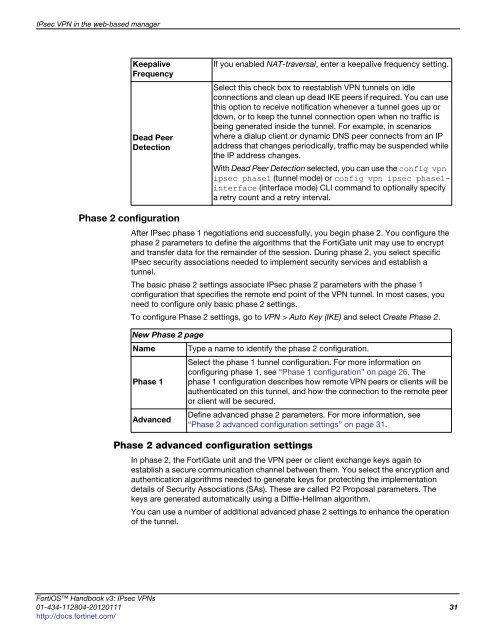
IPsec VPN in the web-based manager<br />
Keepalive<br />
Frequency<br />
Dead Peer<br />
Detection<br />
Phase 2 configuration<br />
After IPsec phase 1 negotiations end successfully, you begin phase 2. You configure the<br />
phase 2 parameters to define the algorithms that the FortiGate unit may use to encrypt<br />
and transfer data for the remainder of the session. During phase 2, you select specific<br />
IPsec security associations needed to implement security services and establish a<br />
tunnel.<br />
The basic phase 2 settings associate IPsec phase 2 parameters with the phase 1<br />
configuration that specifies the remote end point of the VPN tunnel. In most cases, you<br />
need to configure only basic phase 2 settings.<br />
To configure Phase 2 settings, go to VPN > Auto Key (IKE) and select Create Phase 2.<br />
Phase 2 advanced configuration settings<br />
If you enabled NAT-traversal, enter a keepalive frequency setting.<br />
Select this check box to reestablish VPN tunnels on idle<br />
connections and clean up dead IKE peers if required. You can use<br />
this option to receive notification whenever a tunnel goes up or<br />
down, or to keep the tunnel connection open when no traffic is<br />
being generated inside the tunnel. For example, in scenarios<br />
where a dialup client or dynamic DNS peer connects from an IP<br />
address that changes periodically, traffic may be suspended while<br />
the IP address changes.<br />
With Dead Peer Detection selected, you can use the config vpn<br />
<strong>ipsec</strong> phase1 (tunnel mode) or config vpn <strong>ipsec</strong> phase1interface<br />
(interface mode) CLI command to optionally specify<br />
a retry count and a retry interval.<br />
New Phase 2 page<br />
Name Type a name to identify the phase 2 configuration.<br />
Phase 1<br />
Advanced<br />
Select the phase 1 tunnel configuration. For more information on<br />
configuring phase 1, see “Phase 1 configuration” on page 26. The<br />
phase 1 configuration describes how remote VPN peers or clients will be<br />
authenticated on this tunnel, and how the connection to the remote peer<br />
or client will be secured.<br />
Define advanced phase 2 parameters. For more information, see<br />
“Phase 2 advanced configuration settings” on page 31.<br />
In phase 2, the FortiGate unit and the VPN peer or client exchange keys again to<br />
establish a secure communication channel between them. You select the encryption and<br />
authentication algorithms needed to generate keys for protecting the implementation<br />
details of Security Associations (SAs). These are called P2 Proposal parameters. The<br />
keys are generated automatically using a Diffie-Hellman algorithm.<br />
You can use a number of additional advanced phase 2 settings to enhance the operation<br />
of the tunnel.<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 31<br />
http://docs.fortinet.com/