fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
IPsec VPN concepts Encryption<br />
Encryption<br />
Authentication<br />
Encryption mathematically transforms data to appear as meaningless random numbers.<br />
The original data is called plaintext and the encrypted data is called ciphertext. The<br />
opposite process, called decryption, performs the inverse operation to recover the<br />
original plaintext from the ciphertext.<br />
The process by which the plaintext is transformed to ciphertext and back again is called<br />
an algorithm. All algorithms use a small piece of information, a key, in the arithmetic<br />
process of converted plaintext to ciphertext, or vice-versa. IPsec uses symmetrical<br />
algorithms, in which the same key is used to both encrypt and decrypt the data.<br />
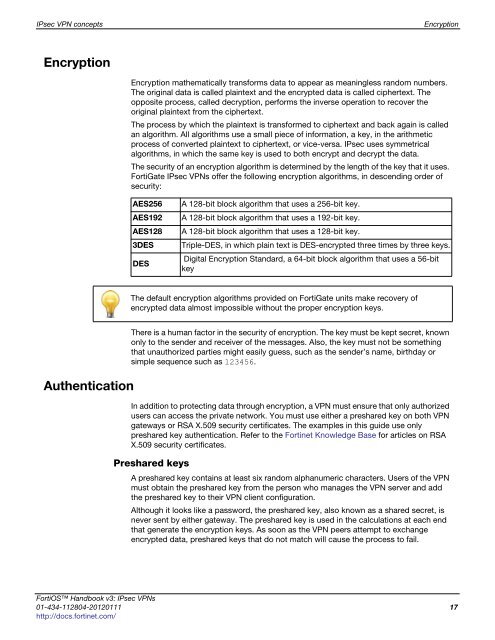
The security of an encryption algorithm is determined by the length of the key that it uses.<br />
FortiGate IPsec VPNs offer the following encryption algorithms, in descending order of<br />
security:<br />
AES256 A 128-bit block algorithm that uses a 256-bit key.<br />
AES192 A 128-bit block algorithm that uses a 192-bit key.<br />
AES128 A 128-bit block algorithm that uses a 128-bit key.<br />
3DES Triple-DES, in which plain text is DES-encrypted three times by three keys.<br />
DES<br />
There is a human factor in the security of encryption. The key must be kept secret, known<br />
only to the sender and receiver of the messages. Also, the key must not be something<br />
that unauthorized parties might easily guess, such as the sender’s name, birthday or<br />
simple sequence such as 123456.<br />
In addition to protecting data through encryption, a VPN must ensure that only authorized<br />
users can access the private network. You must use either a preshared key on both VPN<br />
gateways or RSA X.509 security certificates. The examples in this guide use only<br />
preshared key authentication. Refer to the Fortinet Knowledge Base for articles on RSA<br />
X.509 security certificates.<br />
Preshared keys<br />
Digital Encryption Standard, a 64-bit block algorithm that uses a 56-bit<br />
key<br />
The default encryption algorithms provided on FortiGate units make recovery of<br />
encrypted data almost impossible without the proper encryption keys.<br />
A preshared key contains at least six random alphanumeric characters. Users of the VPN<br />
must obtain the preshared key from the person who manages the VPN server and add<br />
the preshared key to their VPN client configuration.<br />
Although it looks like a password, the preshared key, also known as a shared secret, is<br />
never sent by either gateway. The preshared key is used in the calculations at each end<br />
that generate the encryption keys. As soon as the VPN peers attempt to exchange<br />
encrypted data, preshared keys that do not match will cause the process to fail.<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 17<br />
http://docs.fortinet.com/