fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Configuration overview Hub-and-spoke configurations<br />
This guide discusses the issues involved in configuring a hub-and-spoke VPN and<br />
provides some basic configuration examples.<br />
Hub-and-spoke infrastructure requirements<br />
The FortiGate hub must be operating in NAT mode and have a static public IP<br />
address.<br />
Spokes may have static IP addresses, dynamic IP addresses (see “FortiGate dialupclient<br />
configurations” on page 133), or static domain names and dynamic IP<br />
addresses (see “Dynamic DNS configuration” on page 101).<br />
Spoke gateway addressing<br />
The public IP address of the spoke is the VPN remote gateway as seen from the hub.<br />
Statically addressed spokes each require a separate VPN phase 1 configuration on the<br />
hub. When there are many spokes, this becomes rather cumbersome.<br />
Using dynamic addressing for spokes simplifies the VPN configuration because then the<br />
hub requires only a single phase 1 configuration with “dialup user” as the remote<br />
gateway. You can use this configuration even if the remote peers have static IP<br />
addresses. A remote peer can establish a VPN connection regardless of its IP address if<br />
its traffic selectors match and it can authenticate to the hub. See “Dynamic spokes<br />
configuration example” on page 95 for an example of this configuration.<br />
Protected networks addressing<br />
The addresses of the protected networks are needed to configure destination selectors<br />
and sometimes for security policies and static routes. The larger the number of spokes,<br />
the more addresses there are to manage. You can<br />
assign spoke subnets as part of a larger subnet, usually on a new network<br />
or<br />
create address groups that contain all of the needed addresses<br />
Using aggregated subnets<br />
If you are creating a new network, where subnet IP addresses are not already assigned,<br />
you can simplify the VPN configuration by assigning spoke subnets that are part of a<br />
large subnet.<br />
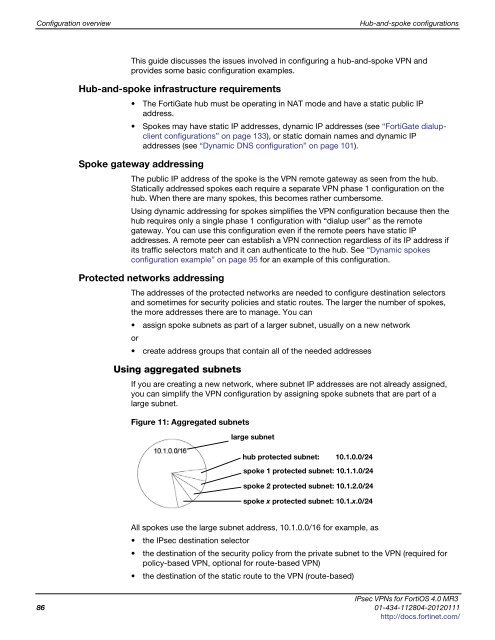
Figure 11: Aggregated subnets<br />
large subnet<br />
hub protected subnet: 10.1.0.0/24<br />
spoke 1 protected subnet: 10.1.1.0/24<br />
spoke 2 protected subnet: 10.1.2.0/24<br />
spoke x protected subnet: 10.1.x.0/24<br />
All spokes use the large subnet address, 10.1.0.0/16 for example, as<br />
the IPsec destination selector<br />
the destination of the security policy from the private subnet to the VPN (required for<br />
policy-based VPN, optional for route-based VPN)<br />
the destination of the static route to the VPN (route-based)<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
86 01-434-112804-20120111<br />
http://docs.fortinet.com/