fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Configure the phase 2 parameters Phase 2 parameters<br />
There are some configurations that require specific selectors:<br />
the VPN peer is a third-party device that uses specific phase2 selectors<br />
the FortiGate unit connects as a dialup client to another FortiGate unit, in which case<br />
you must specify a source IP address, IP address range or subnet<br />
With FortiOS VPNs, your network has multiple layers of security, with quick mode<br />
selectors being an important line of defence.<br />
Routes guide traffic from one IP address to another.<br />
Phase 1 and phase 2 connection settings ensure there is a valid remote end point for<br />
the VPN tunnel that agrees on the encryption and parameters.<br />
Quick mode selectors allow IKE negotiations only for allowed peers.<br />
Security policies control which IP addresses can connect to the VPN.<br />
Security policies also control what protocols are allowed over the VPN along with any<br />
bandwidth limiting.<br />
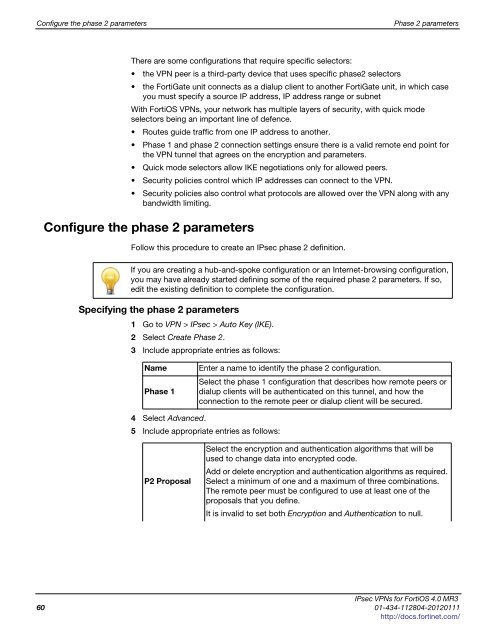
Configure the phase 2 parameters<br />
Follow this procedure to create an IPsec phase 2 definition.<br />
If you are creating a hub-and-spoke configuration or an Internet-browsing configuration,<br />
you may have already started defining some of the required phase 2 parameters. If so,<br />
edit the existing definition to complete the configuration.<br />
Specifying the phase 2 parameters<br />
1 Go to VPN > IPsec > Auto Key (IKE).<br />
2 Select Create Phase 2.<br />
3 Include appropriate entries as follows:<br />
Name Enter a name to identify the phase 2 configuration.<br />
Phase 1<br />
Select the phase 1 configuration that describes how remote peers or<br />
dialup clients will be authenticated on this tunnel, and how the<br />
connection to the remote peer or dialup client will be secured.<br />
4 Select Advanced.<br />
5 Include appropriate entries as follows:<br />
P2 Proposal<br />
Select the encryption and authentication algorithms that will be<br />
used to change data into encrypted code.<br />
Add or delete encryption and authentication algorithms as required.<br />
Select a minimum of one and a maximum of three combinations.<br />
The remote peer must be configured to use at least one of the<br />
proposals that you define.<br />
It is invalid to set both Encryption and Authentication to null.<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
60 01-434-112804-20120111<br />
http://docs.fortinet.com/