fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Configure the dynamically-addressed VPN peer Dynamic DNS configuration<br />
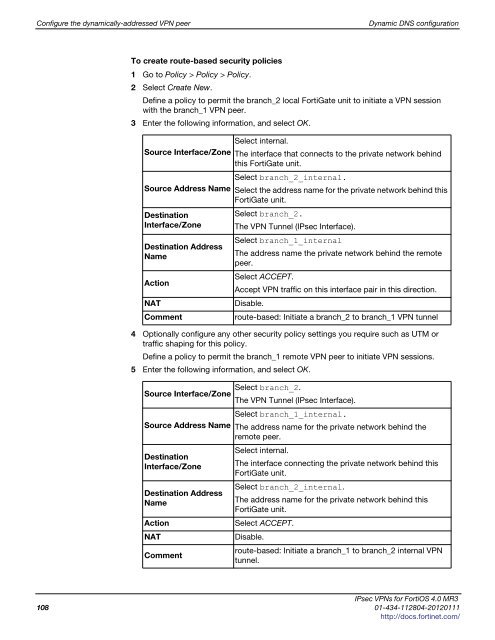
To create route-based security policies<br />
1 Go to Policy > Policy > Policy.<br />
2 Select Create New.<br />
Define a policy to permit the branch_2 local FortiGate unit to initiate a VPN session<br />
with the branch_1 VPN peer.<br />
3 Enter the following information, and select OK.<br />
Select internal.<br />
Source Interface/Zone The interface that connects to the private network behind<br />
this FortiGate unit.<br />
Select branch_2_internal.<br />
Source Address Name Select the address name for the private network behind this<br />
FortiGate unit.<br />
Destination<br />
Interface/Zone<br />
Destination Address<br />
Name<br />
Select branch_2.<br />
The VPN Tunnel (IPsec Interface).<br />
Select branch_1_internal<br />
The address name the private network behind the remote<br />
peer.<br />
Action<br />
Select ACCEPT.<br />
Accept VPN traffic on this interface pair in this direction.<br />
NAT Disable.<br />
Comment route-based: Initiate a branch_2 to branch_1 VPN tunnel<br />
4 Optionally configure any other security policy settings you require such as UTM or<br />
traffic shaping for this policy.<br />
Define a policy to permit the branch_1 remote VPN peer to initiate VPN sessions.<br />
5 Enter the following information, and select OK.<br />
Source Interface/Zone<br />
Select branch_2.<br />
The VPN Tunnel (IPsec Interface).<br />
Select branch_1_internal.<br />
Source Address Name The address name for the private network behind the<br />
remote peer.<br />
Destination<br />
Interface/Zone<br />
Select internal.<br />
The interface connecting the private network behind this<br />
FortiGate unit.<br />
Destination Address<br />
Name<br />
Select branch_2_internal.<br />
The address name for the private network behind this<br />
FortiGate unit.<br />
Action Select ACCEPT.<br />
NAT Disable.<br />
Comment<br />
route-based: Initiate a branch_1 to branch_2 internal VPN<br />
tunnel.<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
108 01-434-112804-20120111<br />
http://docs.fortinet.com/