fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Gateway-to-gateway configurations Testing<br />
Testing<br />
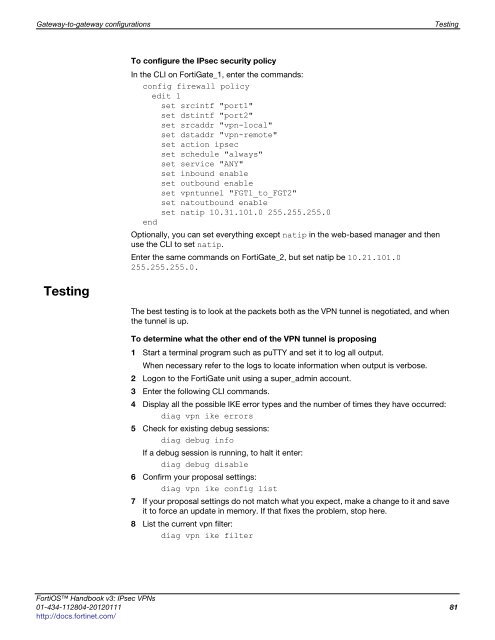
To configure the IPsec security policy<br />
In the CLI on FortiGate_1, enter the commands:<br />
config firewall policy<br />
edit 1<br />
set srcintf "port1"<br />
set dstintf "port2"<br />
set srcaddr "vpn-local"<br />
set dstaddr "vpn-remote"<br />
set action <strong>ipsec</strong><br />
set schedule "always"<br />
set service "ANY"<br />
set inbound enable<br />
set outbound enable<br />
set vpntunnel "FGT1_to_FGT2"<br />
set natoutbound enable<br />
set natip 10.31.101.0 255.255.255.0<br />
end<br />
Optionally, you can set everything except natip in the web-based manager and then<br />
use the CLI to set natip.<br />
Enter the same commands on FortiGate_2, but set natip be 10.21.101.0<br />
255.255.255.0.<br />
The best testing is to look at the packets both as the VPN tunnel is negotiated, and when<br />
the tunnel is up.<br />
To determine what the other end of the VPN tunnel is proposing<br />
1 Start a terminal program such as puTTY and set it to log all output.<br />
When necessary refer to the logs to locate information when output is verbose.<br />
2 Logon to the FortiGate unit using a super_admin account.<br />
3 Enter the following CLI commands.<br />
4 Display all the possible IKE error types and the number of times they have occurred:<br />
diag vpn ike errors<br />
5 Check for existing debug sessions:<br />
diag debug info<br />
If a debug session is running, to halt it enter:<br />
diag debug disable<br />
6 Confirm your proposal settings:<br />
diag vpn ike config list<br />
7 If your proposal settings do not match what you expect, make a change to it and save<br />
it to force an update in memory. If that fixes the problem, stop here.<br />
8 List the current vpn filter:<br />
diag vpn ike filter<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 81<br />
http://docs.fortinet.com/