fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
IPsec VPN in the web-based manager<br />
Manual Key<br />
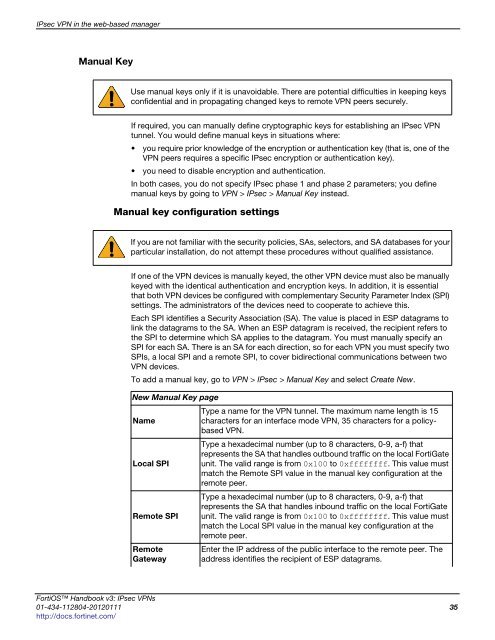
Use manual keys only if it is unavoidable. There are potential difficulties in keeping keys<br />
confidential and in propagating changed keys to remote VPN peers securely.<br />
If required, you can manually define cryptographic keys for establishing an IPsec VPN<br />
tunnel. You would define manual keys in situations where:<br />
you require prior knowledge of the encryption or authentication key (that is, one of the<br />
VPN peers requires a specific IPsec encryption or authentication key).<br />
you need to disable encryption and authentication.<br />
In both cases, you do not specify IPsec phase 1 and phase 2 parameters; you define<br />
manual keys by going to VPN > IPsec > Manual Key instead.<br />
Manual key configuration settings<br />
If you are not familiar with the security policies, SAs, selectors, and SA databases for your<br />
particular installation, do not attempt these procedures without qualified assistance.<br />
If one of the VPN devices is manually keyed, the other VPN device must also be manually<br />
keyed with the identical authentication and encryption keys. In addition, it is essential<br />
that both VPN devices be configured with complementary Security Parameter Index (SPI)<br />
settings. The administrators of the devices need to cooperate to achieve this.<br />
Each SPI identifies a Security Association (SA). The value is placed in ESP datagrams to<br />
link the datagrams to the SA. When an ESP datagram is received, the recipient refers to<br />
the SPI to determine which SA applies to the datagram. You must manually specify an<br />
SPI for each SA. There is an SA for each direction, so for each VPN you must specify two<br />
SPIs, a local SPI and a remote SPI, to cover bidirectional communications between two<br />
VPN devices.<br />
To add a manual key, go to VPN > IPsec > Manual Key and select Create New.<br />
New Manual Key page<br />
Name<br />
Local SPI<br />
Remote SPI<br />
Remote<br />
Gateway<br />
Type a name for the VPN tunnel. The maximum name length is 15<br />
characters for an interface mode VPN, 35 characters for a policybased<br />
VPN.<br />
Type a hexadecimal number (up to 8 characters, 0-9, a-f) that<br />
represents the SA that handles outbound traffic on the local FortiGate<br />
unit. The valid range is from 0x100 to 0xffffffff. This value must<br />
match the Remote SPI value in the manual key configuration at the<br />
remote peer.<br />
Type a hexadecimal number (up to 8 characters, 0-9, a-f) that<br />
represents the SA that handles inbound traffic on the local FortiGate<br />
unit. The valid range is from 0x100 to 0xffffffff. This value must<br />
match the Local SPI value in the manual key configuration at the<br />
remote peer.<br />
Enter the IP address of the public interface to the remote peer. The<br />
address identifies the recipient of ESP datagrams.<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 35<br />
http://docs.fortinet.com/