fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Advanced phase 2 settings Phase 2 parameters<br />
P2 Proposals<br />
Replay detection<br />
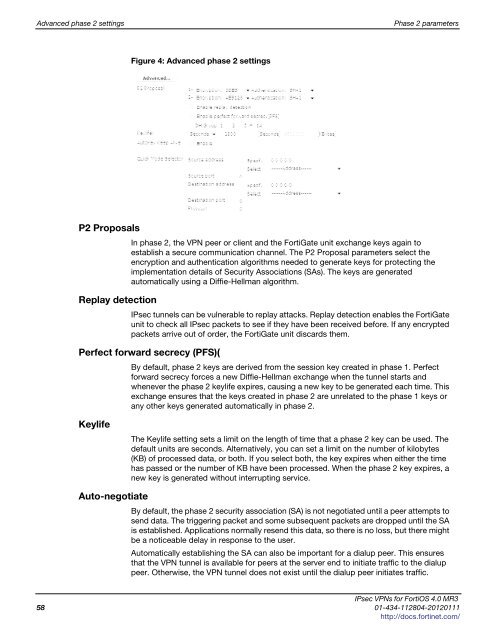
Figure 4: Advanced phase 2 settings<br />
In phase 2, the VPN peer or client and the FortiGate unit exchange keys again to<br />
establish a secure communication channel. The P2 Proposal parameters select the<br />
encryption and authentication algorithms needed to generate keys for protecting the<br />
implementation details of Security Associations (SAs). The keys are generated<br />
automatically using a Diffie-Hellman algorithm.<br />
IPsec tunnels can be vulnerable to replay attacks. Replay detection enables the FortiGate<br />
unit to check all IPsec packets to see if they have been received before. If any encrypted<br />
packets arrive out of order, the FortiGate unit discards them.<br />
Perfect forward secrecy (PFS)(<br />
Keylife<br />
Auto-negotiate<br />
By default, phase 2 keys are derived from the session key created in phase 1. Perfect<br />
forward secrecy forces a new Diffie-Hellman exchange when the tunnel starts and<br />
whenever the phase 2 keylife expires, causing a new key to be generated each time. This<br />
exchange ensures that the keys created in phase 2 are unrelated to the phase 1 keys or<br />
any other keys generated automatically in phase 2.<br />
The Keylife setting sets a limit on the length of time that a phase 2 key can be used. The<br />
default units are seconds. Alternatively, you can set a limit on the number of kilobytes<br />
(KB) of processed data, or both. If you select both, the key expires when either the time<br />
has passed or the number of KB have been processed. When the phase 2 key expires, a<br />
new key is generated without interrupting service.<br />
By default, the phase 2 security association (SA) is not negotiated until a peer attempts to<br />
send data. The triggering packet and some subsequent packets are dropped until the SA<br />
is established. Applications normally resend this data, so there is no loss, but there might<br />
be a noticeable delay in response to the user.<br />
Automatically establishing the SA can also be important for a dialup peer. This ensures<br />
that the VPN tunnel is available for peers at the server end to initiate traffic to the dialup<br />
peer. Otherwise, the VPN tunnel does not exist until the dialup peer initiates traffic.<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
58 01-434-112804-20120111<br />
http://docs.fortinet.com/