fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Routing all remote traffic through the VPN tunnel Internet-browsing configuration<br />
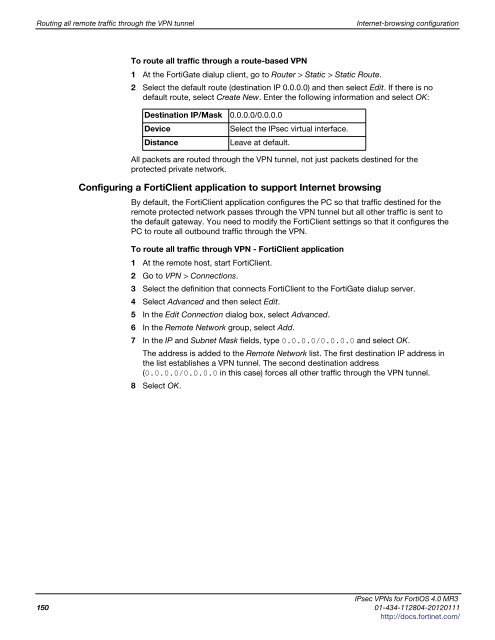
To route all traffic through a route-based VPN<br />
1 At the FortiGate dialup client, go to Router > Static > Static Route.<br />
2 Select the default route (destination IP 0.0.0.0) and then select Edit. If there is no<br />
default route, select Create New. Enter the following information and select OK:<br />
Destination IP/Mask 0.0.0.0/0.0.0.0<br />
Device Select the IPsec virtual interface.<br />
Distance Leave at default.<br />
All packets are routed through the VPN tunnel, not just packets destined for the<br />
protected private network.<br />
Configuring a FortiClient application to support Internet browsing<br />
By default, the FortiClient application configures the PC so that traffic destined for the<br />
remote protected network passes through the VPN tunnel but all other traffic is sent to<br />
the default gateway. You need to modify the FortiClient settings so that it configures the<br />
PC to route all outbound traffic through the VPN.<br />
To route all traffic through VPN - FortiClient application<br />
1 At the remote host, start FortiClient.<br />
2 Go to VPN > Connections.<br />
3 Select the definition that connects FortiClient to the FortiGate dialup server.<br />
4 Select Advanced and then select Edit.<br />
5 In the Edit Connection dialog box, select Advanced.<br />
6 In the Remote Network group, select Add.<br />
7 In the IP and Subnet Mask fields, type 0.0.0.0/0.0.0.0 and select OK.<br />
The address is added to the Remote Network list. The first destination IP address in<br />
the list establishes a VPN tunnel. The second destination address<br />
(0.0.0.0/0.0.0.0 in this case) forces all other traffic through the VPN tunnel.<br />
8 Select OK.<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
150 01-434-112804-20120111<br />
http://docs.fortinet.com/