fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
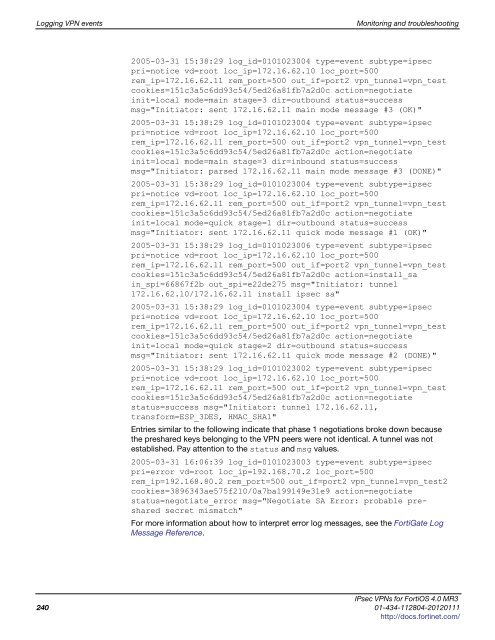
Logging VPN events Monitoring and troubleshooting<br />
2005-03-31 15:38:29 log_id=0101023004 type=event subtype=<strong>ipsec</strong><br />
pri=notice vd=root loc_ip=172.16.62.10 loc_port=500<br />
rem_ip=172.16.62.11 rem_port=500 out_if=port2 vpn_tunnel=vpn_test<br />
cookies=151c3a5c6dd93c54/5ed26a81fb7a2d0c action=negotiate<br />
init=local mode=main stage=3 dir=outbound status=success<br />
msg="Initiator: sent 172.16.62.11 main mode message #3 (OK)"<br />
2005-03-31 15:38:29 log_id=0101023004 type=event subtype=<strong>ipsec</strong><br />
pri=notice vd=root loc_ip=172.16.62.10 loc_port=500<br />
rem_ip=172.16.62.11 rem_port=500 out_if=port2 vpn_tunnel=vpn_test<br />
cookies=151c3a5c6dd93c54/5ed26a81fb7a2d0c action=negotiate<br />
init=local mode=main stage=3 dir=inbound status=success<br />
msg="Initiator: parsed 172.16.62.11 main mode message #3 (DONE)"<br />
2005-03-31 15:38:29 log_id=0101023004 type=event subtype=<strong>ipsec</strong><br />
pri=notice vd=root loc_ip=172.16.62.10 loc_port=500<br />
rem_ip=172.16.62.11 rem_port=500 out_if=port2 vpn_tunnel=vpn_test<br />
cookies=151c3a5c6dd93c54/5ed26a81fb7a2d0c action=negotiate<br />
init=local mode=quick stage=1 dir=outbound status=success<br />
msg="Initiator: sent 172.16.62.11 quick mode message #1 (OK)"<br />
2005-03-31 15:38:29 log_id=0101023006 type=event subtype=<strong>ipsec</strong><br />
pri=notice vd=root loc_ip=172.16.62.10 loc_port=500<br />
rem_ip=172.16.62.11 rem_port=500 out_if=port2 vpn_tunnel=vpn_test<br />
cookies=151c3a5c6dd93c54/5ed26a81fb7a2d0c action=install_sa<br />
in_spi=66867f2b out_spi=e22de275 msg="Initiator: tunnel<br />
172.16.62.10/172.16.62.11 install <strong>ipsec</strong> sa"<br />
2005-03-31 15:38:29 log_id=0101023004 type=event subtype=<strong>ipsec</strong><br />
pri=notice vd=root loc_ip=172.16.62.10 loc_port=500<br />
rem_ip=172.16.62.11 rem_port=500 out_if=port2 vpn_tunnel=vpn_test<br />
cookies=151c3a5c6dd93c54/5ed26a81fb7a2d0c action=negotiate<br />
init=local mode=quick stage=2 dir=outbound status=success<br />
msg="Initiator: sent 172.16.62.11 quick mode message #2 (DONE)"<br />
2005-03-31 15:38:29 log_id=0101023002 type=event subtype=<strong>ipsec</strong><br />
pri=notice vd=root loc_ip=172.16.62.10 loc_port=500<br />
rem_ip=172.16.62.11 rem_port=500 out_if=port2 vpn_tunnel=vpn_test<br />
cookies=151c3a5c6dd93c54/5ed26a81fb7a2d0c action=negotiate<br />
status=success msg="Initiator: tunnel 172.16.62.11,<br />
transform=ESP_3DES, HMAC_SHA1"<br />
Entries similar to the following indicate that phase 1 negotiations broke down because<br />
the preshared keys belonging to the VPN peers were not identical. A tunnel was not<br />
established. Pay attention to the status and msg values.<br />
2005-03-31 16:06:39 log_id=0101023003 type=event subtype=<strong>ipsec</strong><br />
pri=error vd=root loc_ip=192.168.70.2 loc_port=500<br />
rem_ip=192.168.80.2 rem_port=500 out_if=port2 vpn_tunnel=vpn_test2<br />
cookies=3896343ae575f210/0a7ba199149e31e9 action=negotiate<br />
status=negotiate_error msg="Negotiate SA Error: probable preshared<br />
secret mismatch"<br />
For more information about how to interpret error log messages, see the FortiGate Log<br />
Message Reference.<br />
IPsec VPNs for FortiOS 4.0 MR3<br />
2<strong>40</strong> 01-434-112804-20120111<br />
http://docs.fortinet.com/