fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
fortigate-ipsec-40-mr3
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
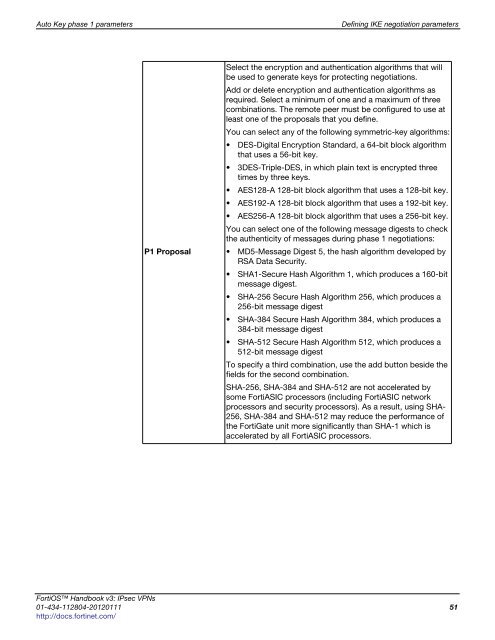
Auto Key phase 1 parameters Defining IKE negotiation parameters<br />
P1 Proposal<br />
Select the encryption and authentication algorithms that will<br />
be used to generate keys for protecting negotiations.<br />
Add or delete encryption and authentication algorithms as<br />
required. Select a minimum of one and a maximum of three<br />
combinations. The remote peer must be configured to use at<br />
least one of the proposals that you define.<br />
You can select any of the following symmetric-key algorithms:<br />
DES-Digital Encryption Standard, a 64-bit block algorithm<br />
that uses a 56-bit key.<br />
3DES-Triple-DES, in which plain text is encrypted three<br />
times by three keys.<br />
AES128-A 128-bit block algorithm that uses a 128-bit key.<br />
AES192-A 128-bit block algorithm that uses a 192-bit key.<br />
AES256-A 128-bit block algorithm that uses a 256-bit key.<br />
You can select one of the following message digests to check<br />
the authenticity of messages during phase 1 negotiations:<br />
MD5-Message Digest 5, the hash algorithm developed by<br />
RSA Data Security.<br />
SHA1-Secure Hash Algorithm 1, which produces a 160-bit<br />
message digest.<br />
SHA-256 Secure Hash Algorithm 256, which produces a<br />
256-bit message digest<br />
SHA-384 Secure Hash Algorithm 384, which produces a<br />
384-bit message digest<br />
SHA-512 Secure Hash Algorithm 512, which produces a<br />
512-bit message digest<br />
To specify a third combination, use the add button beside the<br />
fields for the second combination.<br />
SHA-256, SHA-384 and SHA-512 are not accelerated by<br />
some FortiASIC processors (including FortiASIC network<br />
processors and security processors). As a result, using SHA-<br />
256, SHA-384 and SHA-512 may reduce the performance of<br />
the FortiGate unit more significantly than SHA-1 which is<br />
accelerated by all FortiASIC processors.<br />
FortiOS Handbook v3: IPsec VPNs<br />
01-434-112804-20120111 51<br />
http://docs.fortinet.com/