Local Area Networks (LANs) in Aircraft - FTP Directory Listing - FAA
Local Area Networks (LANs) in Aircraft - FTP Directory Listing - FAA
Local Area Networks (LANs) in Aircraft - FTP Directory Listing - FAA
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
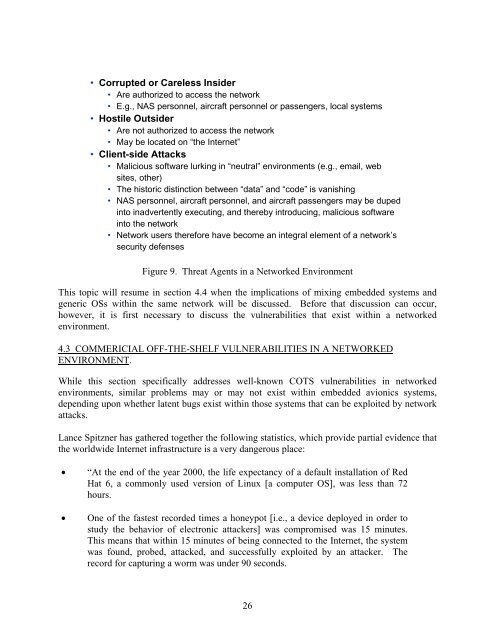
• Corrupted or Careless Insider<br />
• Are authorized to access the network<br />
• E.g., NAS personnel, aircraft personnel or passengers, local systems<br />
• Hostile Outsider<br />
• Are not authorized to access the network<br />
• May be located on “the Internet”<br />
• Client-side Attacks<br />
• Malicious software lurk<strong>in</strong>g <strong>in</strong> “neutral” environments (e.g., email, web<br />
sites, other)<br />
• The historic dist<strong>in</strong>ction between “data” and “code” is vanish<strong>in</strong>g<br />
• NAS personnel, aircraft personnel, and aircraft passengers may be duped<br />
<strong>in</strong>to <strong>in</strong>advertently execut<strong>in</strong>g, and thereby <strong>in</strong>troduc<strong>in</strong>g, malicious software<br />
<strong>in</strong>to the network<br />
• Network users therefore have become an <strong>in</strong>tegral element of a network’s<br />
security defenses<br />
Figure 9. Threat Agents <strong>in</strong> a Networked Environment<br />
This topic will resume <strong>in</strong> section 4.4 when the implications of mix<strong>in</strong>g embedded systems and<br />
generic OSs with<strong>in</strong> the same network will be discussed. Before that discussion can occur,<br />
however, it is first necessary to discuss the vulnerabilities that exist with<strong>in</strong> a networked<br />
environment.<br />
4.3 COMMERICIAL OFF-THE-SHELF VULNERABILITIES IN A NETWORKED<br />
ENVIRONMENT.<br />
While this section specifically addresses well-known COTS vulnerabilities <strong>in</strong> networked<br />
environments, similar problems may or may not exist with<strong>in</strong> embedded avionics systems,<br />
depend<strong>in</strong>g upon whether latent bugs exist with<strong>in</strong> those systems that can be exploited by network<br />
attacks.<br />
Lance Spitzner has gathered together the follow<strong>in</strong>g statistics, which provide partial evidence that<br />
the worldwide Internet <strong>in</strong>frastructure is a very dangerous place:<br />
• “At the end of the year 2000, the life expectancy of a default <strong>in</strong>stallation of Red<br />
Hat 6, a commonly used version of L<strong>in</strong>ux [a computer OS], was less than 72<br />
hours.<br />
• One of the fastest recorded times a honeypot [i.e., a device deployed <strong>in</strong> order to<br />
study the behavior of electronic attackers] was compromised was 15 m<strong>in</strong>utes.<br />
This means that with<strong>in</strong> 15 m<strong>in</strong>utes of be<strong>in</strong>g connected to the Internet, the system<br />
was found, probed, attacked, and successfully exploited by an attacker. The<br />
record for captur<strong>in</strong>g a worm was under 90 seconds.<br />
26