RingMaster Management Guide - Juniper Networks
RingMaster Management Guide - Juniper Networks
RingMaster Management Guide - Juniper Networks
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
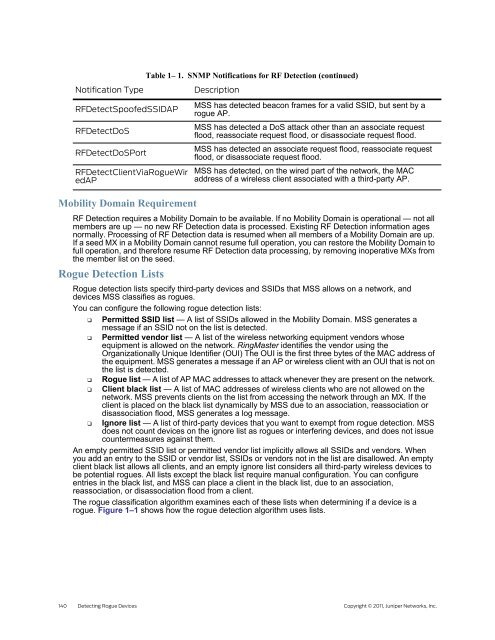
Table 1– 1. SNMP Notifications for RF Detection (continued)<br />
Notification Type Description<br />
RFDetectSpoofedSSIDAP<br />
RFDetectDoS<br />
RFDetectDoSPort<br />
RFDetectClientViaRogueWir<br />
edAP<br />
Mobility Domain Requirement<br />
RF Detection requires a Mobility Domain to be available. If no Mobility Domain is operational — not all<br />
members are up — no new RF Detection data is processed. Existing RF Detection information ages<br />
normally. Processing of RF Detection data is resumed when all members of a Mobility Domain are up.<br />
If a seed MX in a Mobility Domain cannot resume full operation, you can restore the Mobility Domain to<br />
full operation, and therefore resume RF Detection data processing, by removing inoperative MXs from<br />
the member list on the seed.<br />
Rogue Detection Lists<br />
MSS has detected beacon frames for a valid SSID, but sent by a<br />
rogue AP.<br />
MSS has detected a DoS attack other than an associate request<br />
flood, reassociate request flood, or disassociate request flood.<br />
MSS has detected an associate request flood, reassociate request<br />
flood, or disassociate request flood.<br />
MSS has detected, on the wired part of the network, the MAC<br />
address of a wireless client associated with a third-party AP.<br />
Rogue detection lists specify third-party devices and SSIDs that MSS allows on a network, and<br />
devices MSS classifies as rogues.<br />
You can configure the following rogue detection lists:<br />
❑ Permitted SSID list — A list of SSIDs allowed in the Mobility Domain. MSS generates a<br />
message if an SSID not on the list is detected.<br />
❑ Permitted vendor list — A list of the wireless networking equipment vendors whose<br />
equipment is allowed on the network. <strong>RingMaster</strong> identifies the vendor using the<br />
Organizationally Unique Identifier (OUI) The OUI is the first three bytes of the MAC address of<br />
the equipment. MSS generates a message if an AP or wireless client with an OUI that is not on<br />
the list is detected.<br />
❑ Rogue list — A list of AP MAC addresses to attack whenever they are present on the network.<br />
❑ Client black list — A list of MAC addresses of wireless clients who are not allowed on the<br />
network. MSS prevents clients on the list from accessing the network through an MX. If the<br />
client is placed on the black list dynamically by MSS due to an association, reassociation or<br />
disassociation flood, MSS generates a log message.<br />
❑ Ignore list — A list of third-party devices that you want to exempt from rogue detection. MSS<br />
does not count devices on the ignore list as rogues or interfering devices, and does not issue<br />
countermeasures against them.<br />
An empty permitted SSID list or permitted vendor list implicitly allows all SSIDs and vendors. When<br />
you add an entry to the SSID or vendor list, SSIDs or vendors not in the list are disallowed. An empty<br />
client black list allows all clients, and an empty ignore list considers all third-party wireless devices to<br />
be potential rogues. All lists except the black list require manual configuration. You can configure<br />
entries in the black list, and MSS can place a client in the black list, due to an association,<br />
reassociation, or disassociation flood from a client.<br />
The rogue classification algorithm examines each of these lists when determining if a device is a<br />
rogue. Figure 1–1 shows how the rogue detection algorithm uses lists.<br />
140 Detecting Rogue Devices Copyright © 2011, <strong>Juniper</strong> <strong>Networks</strong>, Inc.