RingMaster Management Guide - Juniper Networks
RingMaster Management Guide - Juniper Networks
RingMaster Management Guide - Juniper Networks
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
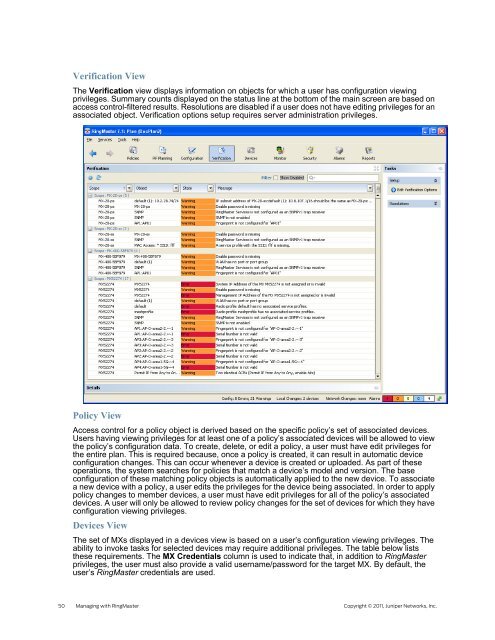
Verification View<br />
The Verification view displays information on objects for which a user has configuration viewing<br />
privileges. Summary counts displayed on the status line at the bottom of the main screen are based on<br />
access control-filtered results. Resolutions are disabled if a user does not have editing privileges for an<br />
associated object. Verification options setup requires server administration privileges.<br />
Policy View<br />
Access control for a policy object is derived based on the specific policy’s set of associated devices.<br />
Users having viewing privileges for at least one of a policy’s associated devices will be allowed to view<br />
the policy’s configuration data. To create, delete, or edit a policy, a user must have edit privileges for<br />
the entire plan. This is required because, once a policy is created, it can result in automatic device<br />
configuration changes. This can occur whenever a device is created or uploaded. As part of these<br />
operations, the system searches for policies that match a device’s model and version. The base<br />
configuration of these matching policy objects is automatically applied to the new device. To associate<br />
a new device with a policy, a user edits the privileges for the device being associated. In order to apply<br />
policy changes to member devices, a user must have edit privileges for all of the policy’s associated<br />
devices. A user will only be allowed to review policy changes for the set of devices for which they have<br />
configuration viewing privileges.<br />
Devices View<br />
The set of MXs displayed in a devices view is based on a user’s configuration viewing privileges. The<br />
ability to invoke tasks for selected devices may require additional privileges. The table below lists<br />
these requirements. The MX Credentials column is used to indicate that, in addition to <strong>RingMaster</strong><br />
privileges, the user must also provide a valid username/password for the target MX. By default, the<br />
user’s <strong>RingMaster</strong> credentials are used.<br />
50 Managing with <strong>RingMaster</strong> Copyright © 2011, <strong>Juniper</strong> <strong>Networks</strong>, Inc.