6th European Conference - Academic Conferences
6th European Conference - Academic Conferences
6th European Conference - Academic Conferences
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
David Merritt and Barry Mullins<br />
to the probability of cyber espionage, it is possible to use this score to measure the probability of the<br />
entire event as being cyber espionage.<br />
It is important to note that an individual event detected by itself may not express outright if a<br />
circumstance is cyber espionage-related or not. A targeted, socially-engineered intrusion might be a<br />
sophisticated spam or phishing attempt. New and undetected information-stealing malware could be a<br />
new variant of benign adware. A consistent transfer of significant amounts of encrypted data could<br />
end up being an authorized VPN (virtual private network) connection. The subtlety of a covert channel<br />
may be difficult to detect or declare with certainty its intentions, but it does serve as an impetus to<br />
investigate further to determine the context of the channel.<br />
The advantage behind this synthesis approach is that intrusion, malware, or exfiltration detection can<br />
be viewed within the context of the whole event. Not doing so could lead to incorrect conclusions<br />
being drawn from insufficient context. But each step of a cyber spy's attack methodology is not of<br />
equal value to the investigator. For instance, it is a challenge to judge the intent of malware simply by<br />
looking at its detectability and functionality. Many malicious programs have the same functionality but<br />
are used for different purposes. In fact, many legitimate programs are frequently used maliciously<br />
(e.g., Remote Administration Tools). On the contrary, a targeted intrusion that is industry-relevant<br />
hints at the intentions of the adversary—to quietly get to specific targets. Thus, the intrusion factor<br />
should be weighted more than the malware “factor”. Similarly, with data exfiltration detection,<br />
covertness of the channel and sensitivity of the data are significant factors affecting the<br />
characterization of espionage. These factors' weights should have more weight than the malware<br />
installation factor.<br />
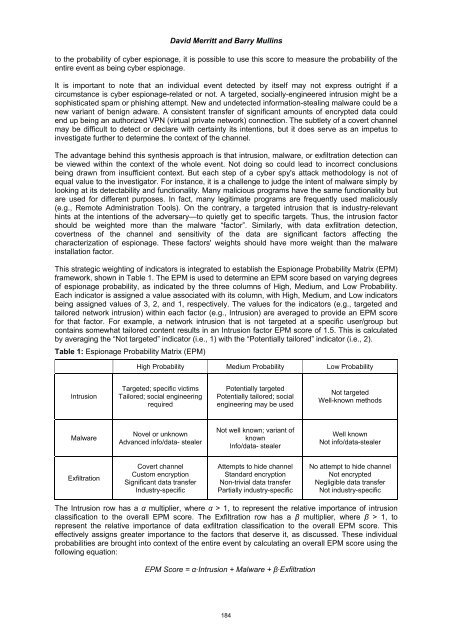
This strategic weighting of indicators is integrated to establish the Espionage Probability Matrix (EPM)<br />
framework, shown in Table 1. The EPM is used to determine an EPM score based on varying degrees<br />
of espionage probability, as indicated by the three columns of High, Medium, and Low Probability.<br />
Each indicator is assigned a value associated with its column, with High, Medium, and Low indicators<br />
being assigned values of 3, 2, and 1, respectively. The values for the indicators (e.g., targeted and<br />
tailored network intrusion) within each factor (e.g., Intrusion) are averaged to provide an EPM score<br />
for that factor. For example, a network intrusion that is not targeted at a specific user/group but<br />
contains somewhat tailored content results in an Intrusion factor EPM score of 1.5. This is calculated<br />
by averaging the “Not targeted” indicator (i.e., 1) with the “Potentially tailored” indicator (i.e., 2).<br />
Table 1: Espionage Probability Matrix (EPM)<br />
Intrusion<br />
Malware<br />
Exfiltration<br />
High Probability Medium Probability Low Probability<br />
Targeted; specific victims<br />
Tailored; social engineering<br />
required<br />
Novel or unknown<br />
Advanced info/data- stealer<br />
Covert channel<br />
Custom encryption<br />
Significant data transfer<br />
Industry-specific<br />
Potentially targeted<br />
Potentially tailored; social<br />
engineering may be used<br />
Not well known; variant of<br />
known<br />
Info/data- stealer<br />
Attempts to hide channel<br />
Standard encryption<br />
Non-trivial data transfer<br />
Partially industry-specific<br />
Not targeted<br />
Well-known methods<br />
Well known<br />
Not info/data-stealer<br />
No attempt to hide channel<br />
Not encrypted<br />
Negligible data transfer<br />
Not industry-specific<br />
The Intrusion row has a α multiplier, where α > 1, to represent the relative importance of intrusion<br />
classification to the overall EPM score. The Exfiltration row has a β multiplier, where β > 1, to<br />
represent the relative importance of data exfiltration classification to the overall EPM score. This<br />
effectively assigns greater importance to the factors that deserve it, as discussed. These individual<br />
probabilities are brought into context of the entire event by calculating an overall EPM score using the<br />
following equation:<br />
EPM Score = α·Intrusion + Malware + β·Exfiltration<br />
184