6th European Conference - Academic Conferences
6th European Conference - Academic Conferences
6th European Conference - Academic Conferences
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Muhammad Naveed<br />
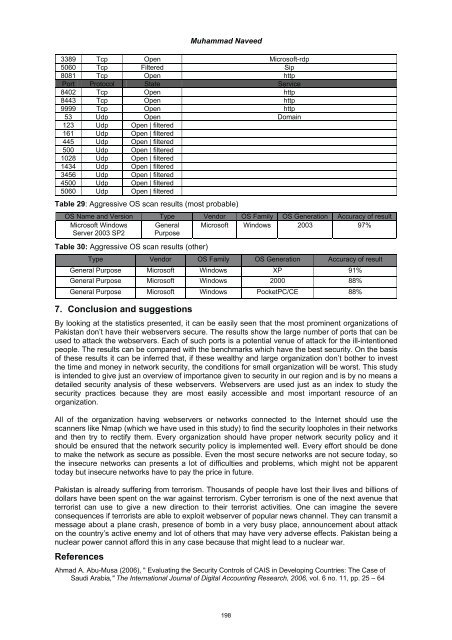
3389 Tcp Open Microsoft-rdp<br />
5060 Tcp Filtered Sip<br />
8081 Tcp Open http<br />
Port Protocol State Service<br />
8402 Tcp Open http<br />
8443 Tcp Open http<br />
9999 Tcp Open http<br />
53 Udp Open Domain<br />
123 Udp Open | filtered<br />
161 Udp Open | filtered<br />
445 Udp Open | filtered<br />
500 Udp Open | filtered<br />
1028 Udp Open | filtered<br />
1434 Udp Open | filtered<br />
3456 Udp Open | filtered<br />
4500 Udp Open | filtered<br />
5060 Udp Open | filtered<br />
Table 29: Aggressive OS scan results (most probable)<br />
OS Name and Version Type Vendor OS Family OS Generation Accuracy of result<br />
Microsoft Windows General Microsoft Windows 2003 97%<br />
Server 2003 SP2 Purpose<br />
Table 30: Aggressive OS scan results (other)<br />
Type Vendor OS Family OS Generation Accuracy of result<br />
General Purpose Microsoft Windows XP 91%<br />
General Purpose Microsoft Windows 2000 88%<br />
General Purpose Microsoft Windows PocketPC/CE 88%<br />
7. Conclusion and suggestions<br />
By looking at the statistics presented, it can be easily seen that the most prominent organizations of<br />
Pakistan don’t have their webservers secure. The results show the large number of ports that can be<br />
used to attack the webservers. Each of such ports is a potential venue of attack for the ill-intentioned<br />
people. The results can be compared with the benchmarks which have the best security. On the basis<br />
of these results it can be inferred that, if these wealthy and large organization don’t bother to invest<br />
the time and money in network security, the conditions for small organization will be worst. This study<br />
is intended to give just an overview of importance given to security in our region and is by no means a<br />
detailed security analysis of these webservers. Webservers are used just as an index to study the<br />
security practices because they are most easily accessible and most important resource of an<br />
organization.<br />
All of the organization having webservers or networks connected to the Internet should use the<br />
scanners like Nmap (which we have used in this study) to find the security loopholes in their networks<br />
and then try to rectify them. Every organization should have proper network security policy and it<br />
should be ensured that the network security policy is implemented well. Every effort should be done<br />
to make the network as secure as possible. Even the most secure networks are not secure today, so<br />
the insecure networks can presents a lot of difficulties and problems, which might not be apparent<br />
today but insecure networks have to pay the price in future.<br />
Pakistan is already suffering from terrorism. Thousands of people have lost their lives and billions of<br />
dollars have been spent on the war against terrorism. Cyber terrorism is one of the next avenue that<br />
terrorist can use to give a new direction to their terrorist activities. One can imagine the severe<br />
consequences if terrorists are able to exploit webserver of popular news channel. They can transmit a<br />
message about a plane crash, presence of bomb in a very busy place, announcement about attack<br />
on the country’s active enemy and lot of others that may have very adverse effects. Pakistan being a<br />
nuclear power cannot afford this in any case because that might lead to a nuclear war.<br />
References<br />
Ahmad A. Abu-Musa (2006), " Evaluating the Security Controls of CAIS in Developing Countries: The Case of<br />
Saudi Arabia," The International Journal of Digital Accounting Research, 2006, vol. 6 no. 11, pp. 25 – 64<br />
198