6th European Conference - Academic Conferences
6th European Conference - Academic Conferences
6th European Conference - Academic Conferences
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Vincent Garramone and Daniel Likarish<br />
forensics course was used to evaluate whether the literature based taxonomy approach would<br />
produce an acceptable description of the material. The result of the evaluation confirmed that a<br />
literature based seeded taxonomy was a good starting point, but that refinement is necessary. The<br />
digital forensics topic was chosen as our initial case because Regis University wanted to make lab<br />
materials from its computer forensics course available on the PRISM site and felt these materials<br />
would be representative of content for a graduate forensics class. The weekly lab materials were<br />
qualitatively evaluated using the list of forensics terms derived from current forensics literature. These<br />
results were then compared to actual terms in the lab topic descriptions given in the course syllabus.<br />
4.1 Granularizing PRISM taxonomies<br />
One of the major goals of PRISM is to make searching for content intuitive and efficient. To achieve<br />
this, content must be tagged in a way that allows keyword and guided searches to return accurate<br />
results. Since IA terminology varies widely among researchers and practitioners, we have tried to<br />
accommodate the broadest possible group of users by developing several taxonomies to tag content.<br />
After a resource has been associated with a particular taxonomy term, it can automatically be<br />
included in guided searches and is reachable with the advanced search function of PRISM. At the<br />
conclusion of the first major development phase, PRISM was equipped with both the International<br />
Information Systems Security Certification Consortium (Theoharidou and Gritzalis 2007) and U.S.<br />
Department of Homeland Security CBK vocabularies (Shoemaker, Drommi, Ingalsbe and Mead<br />
2007). However, in simple use cases existing vocabularies did not offer a sufficient level of specificity.<br />
Rather than create arbitrary lists of terms a researcher might personally want to search for, it was<br />
decided to review the literature and attempt to distill vocabularies that would reflect common usage<br />
among curriculum developers.<br />
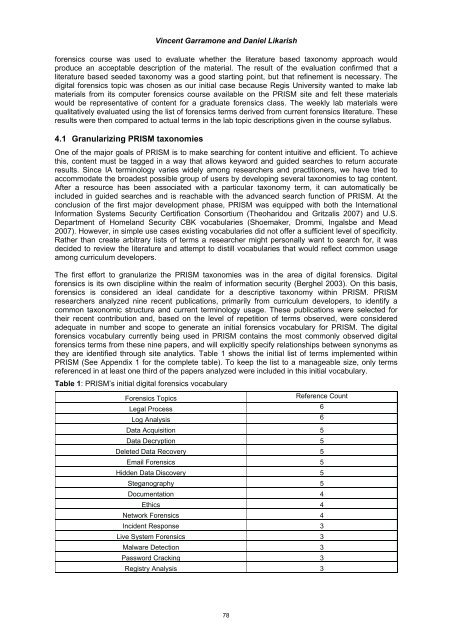
The first effort to granularize the PRISM taxonomies was in the area of digital forensics. Digital<br />
forensics is its own discipline within the realm of information security (Berghel 2003). On this basis,<br />
forensics is considered an ideal candidate for a descriptive taxonomy within PRISM. PRISM<br />
researchers analyzed nine recent publications, primarily from curriculum developers, to identify a<br />
common taxonomic structure and current terminology usage. These publications were selected for<br />
their recent contribution and, based on the level of repetition of terms observed, were considered<br />
adequate in number and scope to generate an initial forensics vocabulary for PRISM. The digital<br />
forensics vocabulary currently being used in PRISM contains the most commonly observed digital<br />
forensics terms from these nine papers, and will explicitly specify relationships between synonyms as<br />
they are identified through site analytics. Table 1 shows the initial list of terms implemented within<br />
PRISM (See Appendix 1 for the complete table). To keep the list to a manageable size, only terms<br />
referenced in at least one third of the papers analyzed were included in this initial vocabulary.<br />
Table 1: PRISM’s initial digital forensics vocabulary<br />
Forensics Topics<br />
Reference Count<br />
Legal Process<br />
6<br />
Log Analysis<br />
6<br />
Data Acquisition 5<br />
Data Decryption 5<br />
Deleted Data Recovery 5<br />
Email Forensics 5<br />
Hidden Data Discovery 5<br />
Steganography 5<br />
Documentation 4<br />
Ethics 4<br />
Network Forensics 4<br />
Incident Response 3<br />
Live System Forensics 3<br />
Malware Detection 3<br />
Password Cracking 3<br />
Registry Analysis 3<br />
78