6th European Conference - Academic Conferences
6th European Conference - Academic Conferences
6th European Conference - Academic Conferences
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Vincent Garramone and Daniel Likarish<br />
To avoid creating too much predefined structure and possibly over-restricting the way users interact<br />
with the site, a single, flat vocabulary of forensics-related terms was defined, as opposed to a<br />
hierarchical one. This allows accommodation of user variance between how they define and use<br />
terms. Furthermore, terms that refer to conceptual subsets of other terms are included in the<br />
vocabulary because they are apparently often used independently of their parent terms in the<br />
literature. For example, “Steganography” could be conceptually categorized as “hidden data<br />
discovery”, but more than half of the papers examined explicitly mentioned the former term. This is an<br />
example of a deterministic approach: allowing actual usage or terms to dictate taxonomy<br />
development.<br />
4.2 Dealing with added complexity<br />
As the taxonomy structure becomes more complex, a tradeoff between the ease of content searching<br />
and the difficulty of content submission is made. To offset the effects of PRISM’s more complex<br />
taxonomy system, PRISM moderators will categorize content for developers. By offering this service,<br />
content submission difficulty will be reduced, requiring only the submission of a link or the upload of<br />
an archive to be posted.<br />
4.3 A trial of the system<br />
We used Regis University’s Computer Forensics course to evaluate the list of terms derived from the<br />
literature (Table 1) and their ability to describe the computer forensics materials. The premise of the<br />
course is to introduce the student to a wide variety of methods for investigating computer security<br />
incidents. Each student takes on the role of a forensic analyst and each week the student is asked to<br />
apply their skills to the analysis of many different types of data with different scenarios and tools. The<br />
students have to create log entries detailing their findings as they work through the process of<br />
analyzing the data for each scenario. First, we chose terms from the vocabulary that we felt<br />
represented the lab content and learning intent. These lists, given in Table 2, column 2, represent the<br />
values a content creator would assign to their own materials upon upload to the PRISM site. Next<br />
those terms were compared with actual language used to describe the lab content in the course<br />
syllabus, and a rating was given to the level of similarity between the available vocabulary terms and<br />
those explicitly listed in the lab topic descriptions. A “Yes” value suggests that the terminology was<br />
sufficiently similar to allow someone not familiar with the content of the lab to effectively classify data<br />
using only a brief description. A “Partial” value means that one or more, but not all of the vocabulary<br />
terms are reflected in the lab topic description. In this case, a material might not be classified under all<br />
relevant terms, making it difficult to locate on the site. As an example, the lab described in the first row<br />
of Table 2 might only be classified as an “Email Forensics” material since “Documentation” and “Legal<br />
Process” are not explicitly mentioned in the description. Finally, a “No” designation is given if none of<br />
the relevant vocabulary terms are present in the lab topic description.<br />
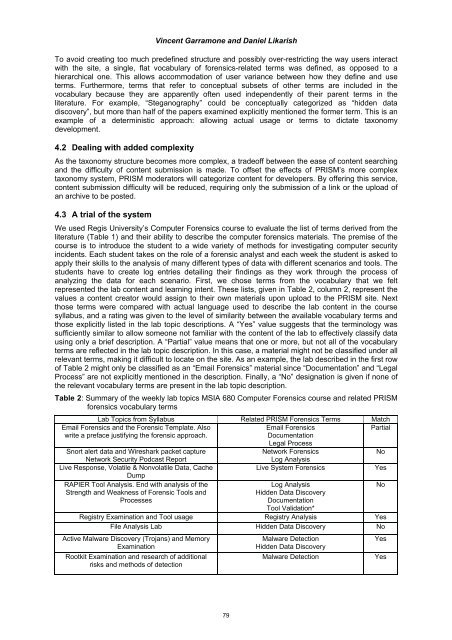
Table 2: Summary of the weekly lab topics MSIA 680 Computer Forensics course and related PRISM<br />
forensics vocabulary terms<br />
Lab Topics from Syllabus Related PRISM Forensics Terms Match<br />
Email Forensics and the Forensic Template. Also<br />
Email Forensics<br />
Partial<br />
write a preface justifying the forensic approach.<br />
Documentation<br />
Legal Process<br />
Snort alert data and Wireshark packet capture<br />
Network Forensics<br />
No<br />
Network Security Podcast Report<br />
Log Analysis<br />
Live Response, Volatile & Nonvolatile Data, Cache<br />
Dump<br />
Live System Forensics Yes<br />
RAPIER Tool Analysis. End with analysis of the<br />
Log Analysis<br />
No<br />
Strength and Weakness of Forensic Tools and<br />
Hidden Data Discovery<br />
Processes<br />
Documentation<br />
Tool Validation*<br />
Registry Examination and Tool usage Registry Analysis Yes<br />
File Analysis Lab Hidden Data Discovery No<br />
Active Malware Discovery (Trojans) and Memory<br />
Examination<br />
Rootkit Examination and research of additional<br />
risks and methods of detection<br />
79<br />
Malware Detection<br />
Hidden Data Discovery<br />
Malware Detection<br />
Yes<br />
Yes