6th European Conference - Academic Conferences
6th European Conference - Academic Conferences
6th European Conference - Academic Conferences
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Manoj Cherukuri and Srinivas Mukkamala<br />
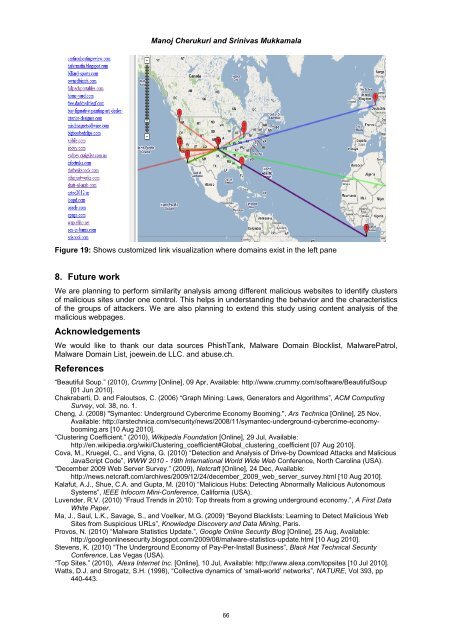
Figure 19: Shows customized link visualization where domains exist in the left pane<br />
8. Future work<br />
We are planning to perform similarity analysis among different malicious websites to identify clusters<br />
of malicious sites under one control. This helps in understanding the behavior and the characteristics<br />
of the groups of attackers. We are also planning to extend this study using content analysis of the<br />
malicious webpages.<br />
Acknowledgements<br />
We would like to thank our data sources PhishTank, Malware Domain Blocklist, MalwarePatrol,<br />
Malware Domain List, joewein.de LLC. and abuse.ch.<br />
References<br />
“Beautiful Soup.” (2010), Crummy [Online], 09 Apr, Available: http://www.crummy.com/software/BeautifulSoup<br />
[01 Jun 2010].<br />
Chakrabarti, D. and Faloutsos, C. (2006) “Graph Mining: Laws, Generators and Algorithms”, ACM Computing<br />
Survey, vol. 38, no. 1.<br />
Cheng, J. (2008) "Symantec: Underground Cybercrime Economy Booming.", Ars Technica [Online], 25 Nov,<br />
Available: http://arstechnica.com/security/news/2008/11/symantec-underground-cybercrime-economybooming.ars<br />
[10 Aug 2010].<br />
“Clustering Coefficient.” (2010), Wikipedia Foundation [Online], 29 Jul, Available:<br />
http://en.wikipedia.org/wiki/Clustering_coefficient#Global_clustering_coefficient [07 Aug 2010].<br />
Cova, M., Kruegel, C., and Vigna, G. (2010) “Detection and Analysis of Drive-by Download Attacks and Malicious<br />
JavaScript Code”, WWW 2010 - 19th International World Wide Web <strong>Conference</strong>, North Carolina (USA).<br />
“December 2009 Web Server Survey.” (2009), Netcraft [Online], 24 Dec, Available:<br />
http://news.netcraft.com/archives/2009/12/24/december_2009_web_server_survey.html [10 Aug 2010].<br />
Kalafut, A.J., Shue, C.A. and Gupta, M. (2010) “Malicious Hubs: Detecting Abnormally Malicious Autonomous<br />
Systems”, IEEE Infocom Mini-<strong>Conference</strong>, California (USA).<br />
Luvender, R.V. (2010) “Fraud Trends in 2010: Top threats from a growing underground economy.”, A First Data<br />
White Paper.<br />
Ma, J., Saul, L.K., Savage, S., and Voelker, M.G. (2009) “Beyond Blacklists: Learning to Detect Malicious Web<br />
Sites from Suspicious URLs”, Knowledge Discovery and Data Mining, Paris.<br />
Provos, N. (2010) “Malware Statistics Update.”, Google Online Security Blog [Online], 25 Aug, Available:<br />
http://googleonlinesecurity.blogspot.com/2009/08/malware-statistics-update.html [10 Aug 2010].<br />
Stevens, K. (2010) “The Underground Economy of Pay-Per-Install Business”, Black Hat Technical Security<br />
<strong>Conference</strong>, Las Vegas (USA).<br />
“Top Sites.” (2010), Alexa Internet Inc. [Online], 10 Jul, Available: http://www.alexa.com/topsites [10 Jul 2010].<br />
Watts, D.J. and Strogatz, S.H. (1998), “Collective dynamics of ‘small-world’ networks”, NATURE, Vol 393, pp<br />
440-443.<br />
66