Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
134 CHAPTER 8 Security Standards and Services<br />
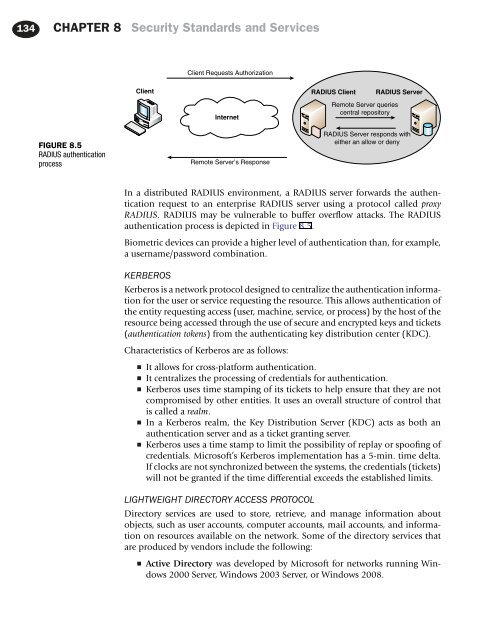
Client Requests Authorization<br />
Client<br />
Internet<br />
RADIUS Client<br />
Remote Server queries<br />
central repository<br />
RADIUS Server<br />
FIGURE 8.5<br />
RADIUS authentication<br />
process<br />
Remote Server’s Response<br />
RADIUS Server responds with<br />
either an allow or deny<br />
In a distributed RADIUS environment, a RADIUS server forwards the authentication<br />
request to an enterprise RADIUS server using a protocol called proxy<br />
RADIUS. RADIUS may be vulnerable to buffer overflow attacks. The RADIUS<br />
authentication process is depicted in Figure 8.5.<br />
Biometric devices can provide a higher level of authentication than, for example,<br />
a username/password combination.<br />
KERBEROS<br />
Kerberos is a network protocol designed to centralize the authentication information<br />
for the user or service requesting the resource. This allows authentication of<br />
the entity requesting access (user, machine, service, or process) by the host of the<br />
resource being accessed through the use of secure and encrypted keys and tickets<br />
(authentication tokens) from the authenticating key distribution center (KDC).<br />
Characteristics of Kerberos are as follows:<br />
■ It allows for cross-platform authentication.<br />
■ It centralizes the processing of credentials for authentication.<br />
■ Kerberos uses time stamping of its tickets to help ensure that they are not<br />
compromised by other entities. It uses an overall structure of control that<br />
is called a realm.<br />
■ In a Kerberos realm, the Key Distribution Server (KDC) acts as both an<br />
authentication server and as a ticket granting server.<br />
■ Kerberos uses a time stamp to limit the possibility of replay or spoofing of<br />
credentials. Microsoft’s Kerberos implementation has a 5-min. time delta.<br />
If clocks are not synchronized between the systems, the credentials (tickets)<br />
will not be granted if the time differential exceeds the established limits.<br />
LIGHTWEIGHT DIRECTORY ACCESS PROTOCOL<br />
Directory services are used to store, retrieve, and manage information about<br />
objects, such as user accounts, computer accounts, mail accounts, and information<br />
on resources available on the network. Some of the directory services that<br />
are produced by vendors include the following:<br />
■<br />
Active Directory was developed by Microsoft for networks running Windows<br />
2000 Server, Windows 2003 Server, or Windows 2008.