Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Network Access Security 137<br />
TACACS+ was the first revision to offer secure communications between<br />
the TACACS+ client and the TACACS+ server. Vulnerabilities and attacks<br />
common with TACACS+ are as follows:<br />
■ The encryption used in TACACS+ is based on a shared secret that is rarely<br />
changed, so a compromise at any point would ultimately expose future<br />
compromises.<br />
■ Birthday attacks The pool of TACACS+ session IDs is not very large;<br />
therefore, it is reasonable that two users could have the same session ID.<br />
■ Buffer overflow Like RADIUS, TACACS+ can fall victim to bufferoverflow<br />
attacks.<br />
■ Packet sniffing The length of passwords can be easily determined by<br />
“sniffing” a network.<br />
■ Lack of integrity checking An attacker can alter accounting records during<br />
transmission because the accounting data is not encrypted during<br />
transport.<br />
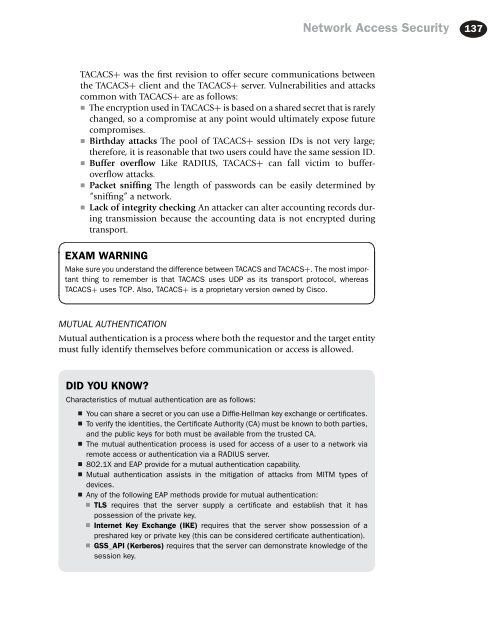
EXAM WARNING<br />
Make sure you understand the difference between TACACS and TACACS+. The most important<br />
thing to remember is that TACACS uses UDP as its transport protocol, whereas<br />
TACACS+ uses TCP. Also, TACACS+ is a proprietary version owned by Cisco.<br />
MUTUAL AUTHENTICATION<br />
Mutual authentication is a process where both the requestor and the target entity<br />
must fully identify themselves before communication or access is allowed.<br />
DID YOU KNOW<br />
Characteristics of mutual authentication are as follows:<br />
■ You can share a secret or you can use a Diffie-Hellman key exchange or certificates.<br />
■ To verify the identities, the Certificate Authority (CA) must be known to both parties,<br />
and the public keys for both must be available from the trusted CA.<br />
■ The mutual authentication process is used for access of a user to a network via<br />
remote access or authentication via a RADIUS server.<br />
■ 802.1X and EAP provide for a mutual authentication capability.<br />
■ Mutual authentication assists in the mitigation of attacks from MITM types of<br />
devices.<br />
■ Any of the following EAP methods provide for mutual authentication:<br />
■ TLS requires that the server supply a certificate and establish that it has<br />
possession of the private key.<br />
■ Internet Key Exchange (IKE) requires that the server show possession of a<br />
preshared key or private key (this can be considered certificate authentication).<br />
■ GSS_API (Kerberos) requires that the server can demonstrate knowledge of the<br />
session key.