Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
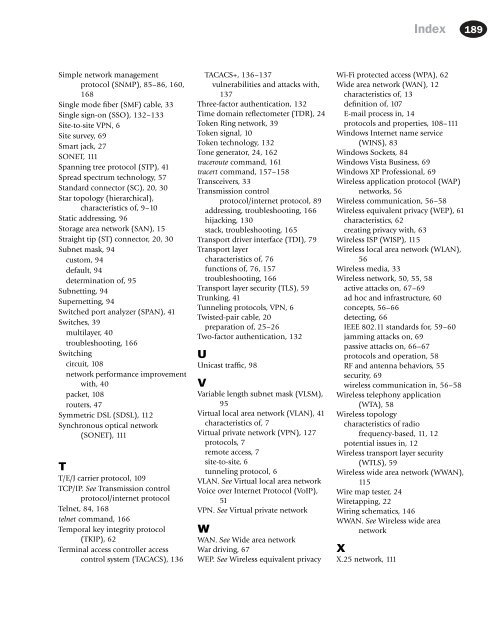
Index 189<br />
Simple network management<br />
protocol (SNMP), 85–86, 160,<br />
168<br />
Single mode fiber (SMF) cable, 33<br />
Single sign-on (SSO), 132–133<br />
Site-to-site VPN, 6<br />
Site survey, 69<br />
Smart jack, 27<br />
SONET, <strong>11</strong>1<br />
Spanning tree protocol (STP), 41<br />
Spread spectrum technology, 57<br />
Standard connector (SC), 20, 30<br />
Star topology (hierarchical),<br />
characteristics of, 9–10<br />
Static addressing, 96<br />
Storage area network (SAN), 15<br />
Straight tip (ST) connector, 20, 30<br />
Subnet mask, 94<br />
custom, 94<br />
default, 94<br />
determination of, 95<br />
Subnetting, 94<br />
Supernetting, 94<br />
Switched port analyzer (SPAN), 41<br />
Switches, 39<br />
multilayer, 40<br />
troubleshooting, 166<br />
Switching<br />
circuit, 108<br />
network performance improvement<br />
with, 40<br />
packet, 108<br />
routers, 47<br />
Symmetric DSL (SDSL), <strong>11</strong>2<br />
Synchronous optical network<br />
(SONET), <strong>11</strong>1<br />
T<br />
T/E/J carrier protocol, 109<br />
TCP/IP. See Transmission control<br />
protocol/internet protocol<br />
Telnet, 84, 168<br />
telnet command, 166<br />
Temporal key integrity protocol<br />
(TKIP), 62<br />
Terminal access controller access<br />
control system (TACACS), 136<br />
TACACS+, 136–137<br />
vulnerabilities and attacks with,<br />
137<br />
Three-factor authentication, 132<br />
Time domain reflectometer (TDR), 24<br />
Token Ring network, 39<br />
Token signal, 10<br />
Token technology, 132<br />
Tone generator, 24, 162<br />
traceroute command, 161<br />
tracert command, 157–158<br />
Transceivers, 33<br />
Transmission control<br />
protocol/internet protocol, 89<br />
addressing, troubleshooting, 166<br />
hijacking, 130<br />
stack, troubleshooting, 165<br />
Transport driver interface (TDI), 79<br />
Transport layer<br />
characteristics of, 76<br />
functions of, 76, 157<br />
troubleshooting, 166<br />
Transport layer security (TLS), 59<br />
Trunking, 41<br />
Tunneling protocols, VPN, 6<br />
Twisted-pair cable, 20<br />
preparation of, 25–26<br />
Two-factor authentication, 132<br />
U<br />
Unicast traffic, 98<br />
V<br />
Variable length subnet mask (VLSM),<br />
95<br />
Virtual local area network (VLAN), 41<br />
characteristics of, 7<br />
Virtual private network (VPN), 127<br />
protocols, 7<br />
remote access, 7<br />
site-to-site, 6<br />
tunneling protocol, 6<br />
VLAN. See Virtual local area network<br />
Voice over Internet Protocol (VoIP),<br />
51<br />
VPN. See Virtual private network<br />
W<br />
WAN. See Wide area network<br />
War driving, 67<br />
WEP. See Wireless equivalent privacy<br />
Wi-Fi protected access (WPA), 62<br />
Wide area network (WAN), 12<br />
characteristics of, 13<br />
definition of, 107<br />
E-mail process in, 14<br />
protocols and properties, 108–<strong>11</strong>1<br />
Windows Internet name service<br />
(WINS), 83<br />
Windows Sockets, 84<br />
Windows Vista Business, 69<br />
Windows XP Professional, 69<br />
Wireless application protocol (WAP)<br />
networks, 56<br />
Wireless communication, 56–58<br />
Wireless equivalent privacy (WEP), 61<br />
characteristics, 62<br />
creating privacy with, 63<br />
Wireless ISP (WISP), <strong>11</strong>5<br />
Wireless local area network (WLAN),<br />
56<br />
Wireless media, 33<br />
Wireless network, 50, 55, 58<br />
active attacks on, 67–69<br />
ad hoc and infrastructure, 60<br />
concepts, 56–66<br />
detecting, 66<br />
IEEE 802.<strong>11</strong> standards for, 59–60<br />
jamming attacks on, 69<br />
passive attacks on, 66–67<br />
protocols and operation, 58<br />
RF and antenna behaviors, 55<br />
security, 69<br />
wireless communication in, 56–58<br />
Wireless telephony application<br />
(WTA), 58<br />
Wireless topology<br />
characteristics of radio<br />
frequency-based, <strong>11</strong>, 12<br />
potential issues in, 12<br />
Wireless transport layer security<br />
(WTLS), 59<br />
Wireless wide area network (WWAN),<br />
<strong>11</strong>5<br />
Wire map tester, 24<br />
Wiretapping, 22<br />
Wiring schematics, 146<br />
WWAN. See Wireless wide area<br />
network<br />
X<br />
X.25 network, <strong>11</strong>1