Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
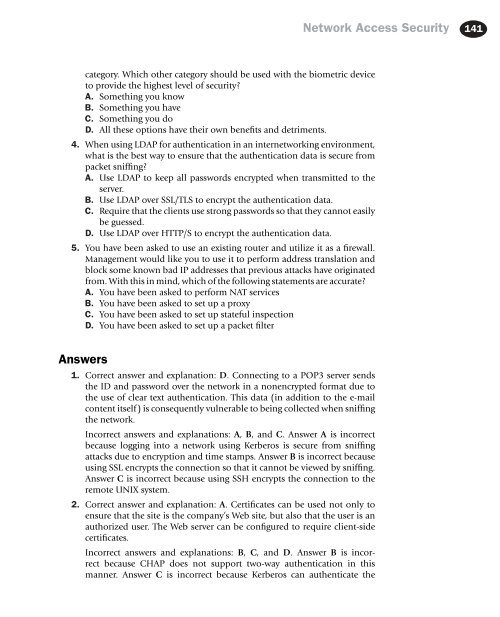
Network Access Security 141<br />
category. Which other category should be used with the biometric device<br />
to provide the highest level of security<br />
A. Something you know<br />
B. Something you have<br />
C. Something you do<br />
D. All these options have their own benefits and detriments.<br />
4. When using LDAP for authentication in an internetworking environment,<br />
what is the best way to ensure that the authentication data is secure from<br />
packet sniffing<br />
A. Use LDAP to keep all passwords encrypted when transmitted to the<br />
server.<br />
B. Use LDAP over SSL/TLS to encrypt the authentication data.<br />
C. Require that the clients use strong passwords so that they cannot easily<br />
be guessed.<br />
D. Use LDAP over HTTP/S to encrypt the authentication data.<br />
5. You have been asked to use an existing router and utilize it as a firewall.<br />
Management would like you to use it to perform address translation and<br />
block some known bad IP addresses that previous attacks have originated<br />
from. With this in mind, which of the following statements are accurate<br />
A. You have been asked to perform NAT services<br />
B. You have been asked to set up a proxy<br />
C. You have been asked to set up stateful inspection<br />
D. You have been asked to set up a packet filter<br />
Answers<br />
1. Correct answer and explanation: D. Connecting to a POP3 server sends<br />
the ID and password over the network in a nonencrypted format due to<br />
the use of clear text authentication. This data (in addition to the e-mail<br />
content itself) is consequently vulnerable to being collected when sniffing<br />
the network.<br />
Incorrect answers and explanations: A, B, and C. Answer A is incorrect<br />
because logging into a network using Kerberos is secure from sniffing<br />
attacks due to encryption and time stamps. Answer B is incorrect because<br />
using SSL encrypts the connection so that it cannot be viewed by sniffing.<br />
Answer C is incorrect because using SSH encrypts the connection to the<br />
remote UNIX system.<br />
2. Correct answer and explanation: A. Certificates can be used not only to<br />
ensure that the site is the company’s Web site, but also that the user is an<br />
authorized user. The Web server can be configured to require client-side<br />
certificates.<br />
Incorrect answers and explanations: B, C, and D. Answer B is incorrect<br />
because CHAP does not support two-way authentication in this<br />
manner. Answer C is incorrect because Kerberos can authenticate the