Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Syngress - Eleventh Hour Network+ Exam N10-004 Study Guide (11 ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
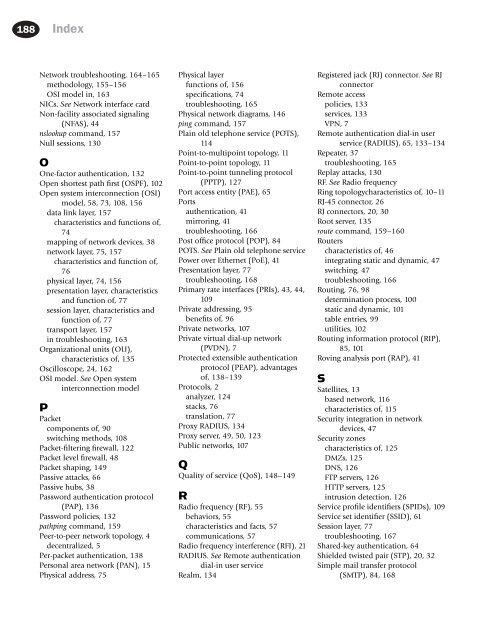
188 Index<br />
Network troubleshooting, 164–165<br />
methodology, 155–156<br />
OSI model in, 163<br />
NICs. See Network interface card<br />
Non-facility associated signaling<br />
(NFAS), 44<br />
nslookup command, 157<br />
Null sessions, 130<br />
O<br />
One-factor authentication, 132<br />
Open shortest path first (OSPF), 102<br />
Open system interconnection (OSI)<br />
model, 58, 73, 108, 156<br />
data link layer, 157<br />
characteristics and functions of,<br />
74<br />
mapping of network devices, 38<br />
network layer, 75, 157<br />
characteristics and function of,<br />
76<br />
physical layer, 74, 156<br />
presentation layer, characteristics<br />
and function of, 77<br />
session layer, characteristics and<br />
function of, 77<br />
transport layer, 157<br />
in troubleshooting, 163<br />
Organizational units (OU),<br />
characteristics of, 135<br />
Oscilloscope, 24, 162<br />
OSI model. See Open system<br />
interconnection model<br />
P<br />
Packet<br />
components of, 90<br />
switching methods, 108<br />
Packet-filtering firewall, 122<br />
Packet level firewall, 48<br />
Packet shaping, 149<br />
Passive attacks, 66<br />
Passive hubs, 38<br />
Password authentication protocol<br />
(PAP), 136<br />
Password policies, 132<br />
pathping command, 159<br />
Peer-to-peer network topology, 4<br />
decentralized, 5<br />
Per-packet authentication, 138<br />
Personal area network (PAN), 15<br />
Physical address, 75<br />
Physical layer<br />
functions of, 156<br />
specifications, 74<br />
troubleshooting, 165<br />
Physical network diagrams, 146<br />
ping command, 157<br />
Plain old telephone service (POTS),<br />
<strong>11</strong>4<br />
Point-to-multipoint topology, <strong>11</strong><br />
Point-to-point topology, <strong>11</strong><br />
Point-to-point tunneling protocol<br />
(PPTP), 127<br />
Port access entity (PAE), 65<br />
Ports<br />
authentication, 41<br />
mirroring, 41<br />
troubleshooting, 166<br />
Post office protocol (POP), 84<br />
POTS. See Plain old telephone service<br />
Power over Ethernet (PoE), 41<br />
Presentation layer, 77<br />
troubleshooting, 168<br />
Primary rate interfaces (PRIs), 43, 44,<br />
109<br />
Private addressing, 95<br />
benefits of, 96<br />
Private networks, 107<br />
Private virtual dial-up network<br />
(PVDN), 7<br />
Protected extensible authentication<br />
protocol (PEAP), advantages<br />
of, 138–139<br />
Protocols, 2<br />
analyzer, 124<br />
stacks, 76<br />
translation, 77<br />
Proxy RADIUS, 134<br />
Proxy server, 49, 50, 123<br />
Public networks, 107<br />
Q<br />
Quality of service (QoS), 148–149<br />
R<br />
Radio frequency (RF), 55<br />
behaviors, 55<br />
characteristics and facts, 57<br />
communications, 57<br />
Radio frequency interference (RFI), 21<br />
RADIUS. See Remote authentication<br />
dial-in user service<br />
Realm, 134<br />
Registered jack (RJ) connector. See RJ<br />
connector<br />
Remote access<br />
policies, 133<br />
services, 133<br />
VPN, 7<br />
Remote authentication dial-in user<br />
service (RADIUS), 65, 133–134<br />
Repeater, 37<br />
troubleshooting, 165<br />
Replay attacks, 130<br />
RF. See Radio frequency<br />
Ring topologycharacteristics of, 10–<strong>11</strong><br />
RJ-45 connector, 26<br />
RJ connectors, 20, 30<br />
Root server, 135<br />
route command, 159–160<br />
Routers<br />
characteristics of, 46<br />
integrating static and dynamic, 47<br />
switching, 47<br />
troubleshooting, 166<br />
Routing, 76, 98<br />
determination process, 100<br />
static and dynamic, 101<br />
table entries, 99<br />
utilities, 102<br />
Routing information protocol (RIP),<br />
85, 101<br />
Roving analysis port (RAP), 41<br />
S<br />
Satellites, 13<br />
based network, <strong>11</strong>6<br />
characteristics of, <strong>11</strong>5<br />
Security integration in network<br />
devices, 47<br />
Security zones<br />
characteristics of, 125<br />
DMZs, 125<br />
DNS, 126<br />
FTP servers, 126<br />
HTTP servers, 125<br />
intrusion detection, 126<br />
Service profile identifiers (SPIDs), 109<br />
Service set identifier (SSID), 61<br />
Session layer, 77<br />
troubleshooting, 167<br />
Shared-key authentication, 64<br />
Shielded twisted pair (STP), 20, 32<br />
Simple mail transfer protocol<br />
(SMTP), 84, 168