Intrusion Defense Firewall 1.2 User's Guide - Trend Micro? Online ...
Intrusion Defense Firewall 1.2 User's Guide - Trend Micro? Online ...
Intrusion Defense Firewall 1.2 User's Guide - Trend Micro? Online ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
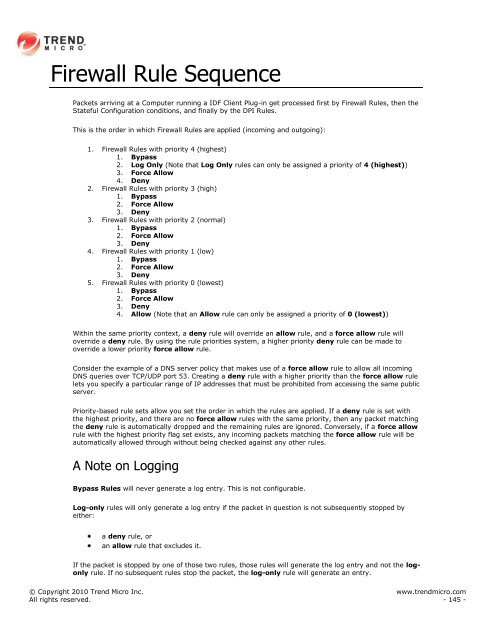
<strong>Firewall</strong> Rule Sequence<br />
Packets arriving at a Computer running a IDF Client Plug-in get processed first by <strong>Firewall</strong> Rules, then the<br />
Stateful Configuration conditions, and finally by the DPI Rules.<br />
This is the order in which <strong>Firewall</strong> Rules are applied (incoming and outgoing):<br />
1. <strong>Firewall</strong> Rules with priority 4 (highest)<br />
1. Bypass<br />
2. Log Only (Note that Log Only rules can only be assigned a priority of 4 (highest))<br />
3. Force Allow<br />
4. Deny<br />
2. <strong>Firewall</strong> Rules with priority 3 (high)<br />
1. Bypass<br />
2. Force Allow<br />
3. Deny<br />
3. <strong>Firewall</strong> Rules with priority 2 (normal)<br />
1. Bypass<br />
2. Force Allow<br />
3. Deny<br />
4. <strong>Firewall</strong> Rules with priority 1 (low)<br />
1. Bypass<br />
2. Force Allow<br />
3. Deny<br />
5. <strong>Firewall</strong> Rules with priority 0 (lowest)<br />
1. Bypass<br />
2. Force Allow<br />
3. Deny<br />
4. Allow (Note that an Allow rule can only be assigned a priority of 0 (lowest))<br />
Within the same priority context, a deny rule will override an allow rule, and a force allow rule will<br />
override a deny rule. By using the rule priorities system, a higher priority deny rule can be made to<br />
override a lower priority force allow rule.<br />
Consider the example of a DNS server policy that makes use of a force allow rule to allow all incoming<br />
DNS queries over TCP/UDP port 53. Creating a deny rule with a higher priority than the force allow rule<br />
lets you specify a particular range of IP addresses that must be prohibited from accessing the same public<br />
server.<br />
Priority-based rule sets allow you set the order in which the rules are applied. If a deny rule is set with<br />
the highest priority, and there are no force allow rules with the same priority, then any packet matching<br />
the deny rule is automatically dropped and the remaining rules are ignored. Conversely, if a force allow<br />
rule with the highest priority flag set exists, any incoming packets matching the force allow rule will be<br />
automatically allowed through without being checked against any other rules.<br />
A Note on Logging<br />
Bypass Rules will never generate a log entry. This is not configurable.<br />
Log-only rules will only generate a log entry if the packet in question is not subsequently stopped by<br />
either:<br />
a deny rule, or<br />
an allow rule that excludes it.<br />
If the packet is stopped by one of those two rules, those rules will generate the log entry and not the logonly<br />
rule. If no subsequent rules stop the packet, the log-only rule will generate an entry.<br />
© Copyright 2010 <strong>Trend</strong> <strong>Micro</strong> Inc. www.trendmicro.com<br />
All rights reserved. - 145 -