Intrusion Defense Firewall 1.2 User's Guide - Trend Micro? Online ...
Intrusion Defense Firewall 1.2 User's Guide - Trend Micro? Online ...
Intrusion Defense Firewall 1.2 User's Guide - Trend Micro? Online ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
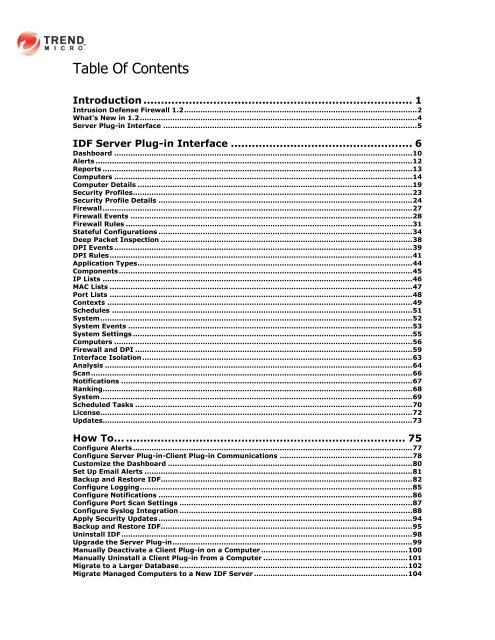
Table Of Contents<br />
Introduction ............................................................................. 1<br />
<strong>Intrusion</strong> <strong>Defense</strong> <strong>Firewall</strong> <strong>1.2</strong> .................................................................................................... 2<br />
What's New in <strong>1.2</strong> ....................................................................................................................... 4<br />
Server Plug-in Interface ............................................................................................................. 5<br />
IDF Server Plug-in Interface .................................................... 6<br />
Dashboard ................................................................................................................................ 10<br />
Alerts ........................................................................................................................................ 12<br />
Reports ..................................................................................................................................... 13<br />
Computers ................................................................................................................................ 14<br />
Computer Details ...................................................................................................................... 19<br />
Security Profiles ........................................................................................................................ 23<br />
Security Profile Details ............................................................................................................. 24<br />
<strong>Firewall</strong> ..................................................................................................................................... 27<br />
<strong>Firewall</strong> Events ......................................................................................................................... 28<br />
<strong>Firewall</strong> Rules ........................................................................................................................... 31<br />
Stateful Configurations ............................................................................................................. 34<br />
Deep Packet Inspection ............................................................................................................ 38<br />
DPI Events ................................................................................................................................ 39<br />
DPI Rules .................................................................................................................................. 41<br />
Application Types ...................................................................................................................... 44<br />
Components .............................................................................................................................. 45<br />
IP Lists ..................................................................................................................................... 46<br />
MAC Lists .................................................................................................................................. 47<br />
Port Lists .................................................................................................................................. 48<br />
Contexts ................................................................................................................................... 49<br />
Schedules ................................................................................................................................. 51<br />
System ...................................................................................................................................... 52<br />
System Events .......................................................................................................................... 53<br />
System Settings ........................................................................................................................ 55<br />
Computers ................................................................................................................................ 56<br />
<strong>Firewall</strong> and DPI ....................................................................................................................... 59<br />
Interface Isolation .................................................................................................................... 63<br />
Analysis .................................................................................................................................... 64<br />
Scan .......................................................................................................................................... 66<br />
Notifications ............................................................................................................................. 67<br />
Ranking..................................................................................................................................... 68<br />
System ...................................................................................................................................... 69<br />
Scheduled Tasks ....................................................................................................................... 70<br />
License ...................................................................................................................................... 72<br />
Updates..................................................................................................................................... 73<br />
How To... ................................................................................ 75<br />
Configure Alerts ........................................................................................................................ 77<br />
Configure Server Plug-in-Client Plug-in Communications ......................................................... 78<br />
Customize the Dashboard ......................................................................................................... 80<br />
Set Up Email Alerts ................................................................................................................... 81<br />
Backup and Restore IDF ............................................................................................................ 82<br />
Configure Logging ..................................................................................................................... 85<br />
Configure Notifications ............................................................................................................. 86<br />
Configure Port Scan Settings .................................................................................................... 87<br />
Configure Syslog Integration .................................................................................................... 88<br />
Apply Security Updates ............................................................................................................. 94<br />
Backup and Restore IDF ............................................................................................................ 95<br />
Uninstall IDF ............................................................................................................................. 98<br />
Upgrade the Server Plug-in ....................................................................................................... 99<br />
Manually Deactivate a Client Plug-in on a Computer ............................................................... 100<br />
Manually Uninstall a Client Plug-in from a Computer .............................................................. 101<br />
Migrate to a Larger Database .................................................................................................. 102<br />
Migrate Managed Computers to a New IDF Server .................................................................. 104