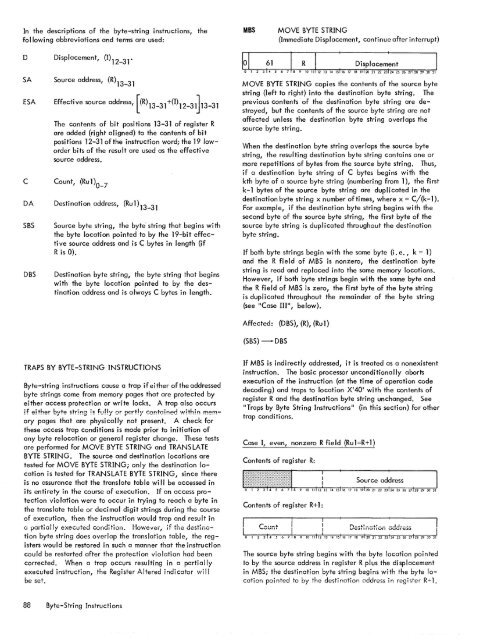
In the descriptions of the byte-string instructions, thefollowing abbreviations and terms are used:MBSMOVE BYTE STRING(Immediate Displacement, continue after interrupt)o Displacement, (1)12-3<strong>1.</strong>SAESACDASBSDBSSource address, (R)13-31Effecti ve source address, [(R) 13 -31 +(1) 12 -31} 3 -31<strong>The</strong> contents of bit positions 13-31 of register Rare added (right aligned) to the contents of bitposi tions 12-31 of the instruction word; the 19 loworderbits of the result are used as the effectivesource address.Count, (Ru1)0_7Destination address, (Ru1)13_31Source byte string, the byte' string that begins withthe byte location pointed to by the 19-bit effectivesource address and is C bytes in length (ifR is 0).Destination byte string, the byte string that beginswith the byte location pointed to by the destinati on address and is always C bytes in length.MOVE BYTE STRING copies the contents of the source bytestring (left to right) into the destination byte string. <strong>The</strong>previous contents of the destination byte string are destroyed,but the contents of the source byte string are notaffected unless the destination byte string overlaps thesource byte string.When the destination byte string overlaps the source bytestring, the resulting destination byte string contains one ormore repetitions of bytes from the source byte string. Thus,if a destination byte string of C bytes begins with thekth byte of a source byte string (numbering from 1), the firstk-1 bytes of the source byte string are duplicated in thedestination byte string x number of times, where x = C/{k-1).For example, if the destination byte string begins with thesecond byte of the source byte string, the first byte of thesource byte string is duplicated throughout the destinationbyte string.If both byte strings begin with the same byte (i. e., k = 1)and the R field of MBS is nonzero, the destination bytestring is read and replaced into the same memory locations.However, if both byte strings begin with the same byte andthe R field of MBS is zero, the first byte of the byte stringis duplicated throughout the remainder of the byte string(see "Case 111", below).Affected: (DBS), (R), (Ru1)(SBS) -DBSTRAPS BY BYTE-STRING INSTRUCTIONSByte-string instructions cause a trap if either of the addressedbyte strings come from memory pages that are protected byeither access protection or write locks. A trap also occursif elther byte stdng is fully or partly contoi!"'!ed with!!"'! memorypages that are physically not present. A check forthese access trap conditions is made prior to initiation ofany byte relocation or general register change. <strong>The</strong>se testsare performed for MOVE BYTE STRING and TRANS LATEBYTE STRING. <strong>The</strong> source and destination locations aretested for MOVE BYTE STRING; only the destination locationis tested for TRANSLATE BYTE STRING, since thereis no assurance that the translate table wi II be accessed inits entirety in the course of execution. If an access protectionviolation were to occur in trying to reach a byte inthe translate table or decimal digit strings during the courseof execution, then the instruction would trap and result inCi pCii-tiCilly executed condition. However, if the destinationbyte string does overlap the translation table, the registerswould be restored in such a manner that the instructioncould be restarted after the protection violation had beencorrected. When a trap occurs resulting in a partiallyexecuted instruction, the Register Altered indi cator wi"be set.If MBS is indirectly addressed, it is treated as a nonexistentinstruction. <strong>The</strong> basic processor unconditionally abortsexecution of the instruction (at the time of operation codedecoding) and traps to location X'40' with the contents ofregister R and the destination byte string unchanged. See"Traps by Byte String Instructions" (in this section) for othertrap conditions.Case I, even, nonzero R fi e Id (Ru 1 =R + 1)Contents of register R:Contents of register R+1:<strong>The</strong> source byte string begins with the byte location pointedto by the source address in register R plus the displacementin MBS; the destination byte string begins with the byte locationpointed to by the destiratior address in register R+l.88 Byte-String Instructions
Both byte strings are C bytes in length. When the instructionis completed, the destination and source addresses are eachincremented by C, and C is set to zero.Case II, odd R fi e Id (Ru 1 =R)Contents of register R:<strong>The</strong> source byte string begins with the byte location pointedto by the address in register R plus the displacement in MBS;the destination byte string begins with the byte locationpointed to by the destination address in register R. Bothbyte strings are C bytes in length. When the instruction iscompleted, the destination address is incremented by C,and C is set to zero.Condition code settings:2 3 4 Result of CBS- 0 0 Source byte string equals destination bytestring or initial byte count is equal to zero.- 0 Source byte string less than destination bytestring.o Source byte string greater than destinationbyte string.If CBS is indirectly addressed, it is treated as a nonexistentinstruction. <strong>The</strong> basic processor unconditionally abortsexecution of the instruction (at the time of operation codedecoding) and traps to location X'40' with the contentsof register R and the destination byte string unchanged.See "Traps By Byte String Instructions" (in this section) forother trap conditions.Case III, zero R field (Rul=l)Contents of register 1:Case I, even, nonzero R field {Rul=R+l}Contents of register R:<strong>The</strong> source byte string consists of a single byte, the contentsof the byte location pointed to by the displacement inMBS; the destination byte string begins with the byte locationpointed to by the destination address in register 1 andis C bytes in length. In this case, the source byte is duplicatedthroughout the destination byte string. When theinstruction is completed, the destination address is incrementedby C, and C is set to zero.Contents of register R+l:Ihe source byte string begins with the byte iocatlon pointedto by the source address in register R plus the displacementin CBS; the destination byte string begins with the byte locationpointed to by the destination address in register R+l.Both byte strings are C bytes in length.CBSCOMPARE BYTE STRING{Immediate displacement, continue after interrupt}Case II, odd R field (Ru l=R)Contents of register R:COMPARE BYTE STRING compares, as magnitudes, thecontents of the source byte string with the contents ofthe destination byte string, byte by corresponding byte,beginning with the first byte of each string. <strong>The</strong> comparisoncontinues unti I the specified number of bytes havebeen compared or unti I an inequality is found. When CBSis terminated, CC3 and CC4 are set to indicate the resultofthe last comparison. If the CBS instruction terminates due toinequality, the count in register Rul is one greater than thenumber of bytes remaining to be compared; the source addressin register R and the destination address in register Rulindicate the locations of the unequal bytes.Affected: {R}, (Rul), CC3, CC4(SBS) : (DBS)<strong>The</strong> source byte string begins with the byte location pointedto by the address in register R plus the displacement in CBS;the destination byte string begins with the byte locationpointed to by the destination address in register R. Bothbyte strings are C bytes in length.Case III, zero R field (Rul=l)Contents of register 1:<strong>The</strong> source byte string consists of a single byte, the contentsof the location pointed to by the displacement in CBS;Byte-String Instructions 89
- Page 1 and 2:
Xerox 560 ComputerReference Manual9
- Page 5 and 6:
4. INPUT/OUTPUT OPERA TIO NS 142 AG
- Page 7 and 8:
1. XEROX 560 COMPUTER SYSTEMINTRODU
- Page 10 and 11:
Many operations are performed in fl
- Page 12 and 13:
Rapid Context Switching. When respo
- Page 14 and 15:
2. SYSTEM ORGANIZATIONThe elements
- Page 16:
FAST MEMORYARITHMETIC AND CONTROL U
- Page 19 and 20:
INFORMATION BOUNDARIESBasic process
- Page 21 and 22:
(Maximumof eight)Core Core Core Cor
- Page 23 and 24:
3. Diagnostic logic. Each memory dr
- Page 25 and 26:
eference address field of the instr
- Page 27 and 28:
Instruction in memory:Instruction i
- Page 29 and 30:
Real-extended addressing is specifi
- Page 31:
Table 1. Basic Processor Operating
- Page 35 and 36:
DesignationFunctionDesignationFunct
- Page 37 and 38:
InterruptStateDisarmedArmed[$Waitin
- Page 39 and 40:
AddressTable 2. Interrupt Locations
- Page 41 and 42:
is assumed to contain an XPSD or a
- Page 43 and 44: Table 3. Summary of Trap LocationsL
- Page 45 and 46: TRAP MASKSThe programmer may mask t
- Page 47 and 48: PUSH-DOWN STACK LIMIT TRAPPush-down
- Page 49 and 50: Instruction Name Mnemonic FaultDeci
- Page 51 and 52: subroutine. However, with certain c
- Page 53 and 54: 3. INSTRUCTION REPERTOIREThis chapt
- Page 55 and 56: CC1 is unchanged by the instruction
- Page 57 and 58: Condition code settings:2 3 4 Resul
- Page 59 and 60: Example 2, odd R field value:Before
- Page 61 and 62: significance (FS), floating zero (F
- Page 63 and 64: next sequential register after regi
- Page 65 and 66: R 1 R2 R3 MeaningoThe effective vir
- Page 67 and 68: Condition code settings:2 3 4 Resul
- Page 69 and 70: MIMULTIPLY IMMEDIATE(Immediate oper
- Page 71 and 72: original contents of register R, re
- Page 73 and 74: Instruction NameCompare HalfwordMne
- Page 75 and 76: Condition code settings:2 3 4 Resul
- Page 77 and 78: 2 3 4 Result of ShiftCircular Shift
- Page 79 and 80: 4. At the completion of the left sh
- Page 81 and 82: Instruction NameFloating Subtract L
- Page 83 and 84: The following table shows the possi
- Page 85 and 86: Table 8.Condition Code Settings for
- Page 87 and 88: PACKED DECIMAL NUMBERSAll decimal a
- Page 89 and 90: DSTDECIMAL STORE(Byte index alignme
- Page 91 and 92: If no indirect addressing or indexi
- Page 93: Instruction NameMnemonicDesignation
- Page 97 and 98: of the destination byte that caused
- Page 99 and 100: again present, unti I a positive or
- Page 101 and 102: The new contents of register 7 are:
- Page 103 and 104: traps to location X'42 1 as a resul
- Page 105 and 106: If there is sufficient space in the
- Page 107 and 108: If CC1, or CC3, or both CC1 and CC3
- Page 109 and 110: appropriate memory stack locations
- Page 111 and 112: II, EI) are generated by II ORing"
- Page 113 and 114: In the real extended addressing mod
- Page 115 and 116: CAll INSTRUCTIONSEach ofthe four CA
- Page 117 and 118: The XPSD instruction' is used for t
- Page 119 and 120: If (I)1O = 0, trap or interrupt ins
- Page 121 and 122: For either memory map format and ei
- Page 123 and 124: initial value plus the initial valu
- Page 125 and 126: Table 9. Status Word 0Field Bits Co
- Page 127 and 128: READ INTERRUPT INHIBITSThe followin
- Page 129 and 130: Table 11.Read Direct Mode 9 Status
- Page 131 and 132: SET ALARM INDICATORThe following co
- Page 133 and 134: INPUT jOUTPUT INSTRUCTIONSThe I/o i
- Page 135 and 136: Table 13.Description of I/o Instruc
- Page 137 and 138: Table 15.Device Status Byte (Regist
- Page 139 and 140: Table 16. Operational Status Byte (
- Page 141 and 142: Table 19.Status Response Bits for A
- Page 143 and 144: If CC4 = 0, the MIOP is in a normal
- Page 145 and 146:
2 3 4 Meaningo 0 I/o address not re
- Page 147 and 148:
The functions of bits within the DC
- Page 149 and 150:
4. Each unit-record controller (int
- Page 151 and 152:
Interrupt at Channel End (Bit Posit
- Page 153 and 154:
Transfer in Channel. A control lOCO
- Page 155 and 156:
Otherwise, the first word of the ne
- Page 157 and 158:
Depending upon the characteristics
- Page 159 and 160:
change the rate on the primary cons
- Page 161 and 162:
Location(hex) (dec)20 3221 3322 342
- Page 163 and 164:
Table 22.Diagnostic Control (P-Mode
- Page 165 and 166:
at its normal rate (e. g., fixed du
- Page 167 and 168:
SET LOW CLOCK MARGINSThis command c
- Page 169 and 170:
BP STATUS AND NO.Th i s group of i
- Page 171 and 172:
Input5MPri ntout5MFunctionStore X 1
- Page 173 and 174:
6. SYSTEM CONFIGURATION CONTROLPool
- Page 175 and 176:
Table 25. Functions of Processor Cl
- Page 177:
Table 26. Functions of Memory Unit
- Page 180 and 181:
STANDARD 8-BIT COMPUTER CODES (EBCD
- Page 182 and 183:
STANDARD SYMBOL-CODE CORRESPONDENCE
- Page 184 and 185:
STANDARD SYMBOL-CODE CORRESPONDENCE
- Page 186 and 187:
TABLE OF POWERS OF SIXTEEN II162564
- Page 188 and 189:
HEXADECIMAL-DECIMAL INTEGER CONVERS
- Page 190 and 191:
HEXADECIMAL-DECIMAL INTEGER CONVERS
- Page 192 and 193:
HEXADECIMAL-DECIMAL INTEGER CONVERS
- Page 194 and 195:
HEXADECIMAL-DECIMAL FRACTION CONVER
- Page 196 and 197:
HEXADECIMAL-DECIMAL FRACTION CONVER
- Page 198 and 199:
APPENDIX B.GLOSSARY OF SYMBOLIC TER
- Page 200 and 201:
TermMeaningTermMeaningWKxWrite key
- Page 202 and 203:
Table C-2. Memory Unit Status Regis
- Page 204 and 205:
Y OYf'lV r'f'lrnf'lrtil"\n'''' ....
- Page 206:
701 South Aviation BoulevardEI Segu