Australian Government Architecture Reference Models Version 3.0
Australian Government Architecture Reference Models Version 3.0
Australian Government Architecture Reference Models Version 3.0
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
198<br />
7.6 Security and Privacy<br />
Security and privacy considerations apply to all three of the DRM’s standardisation areas. Security defines the<br />
methods of protecting information and information systems from unauthorised access, use, disclosure,<br />
disruption, modification or destruction in order to provide integrity, confidentiality and availability, whether in<br />
storage or in transit. Privacy addresses the acceptable collection, storage, use and disclosure of information, and<br />
its accuracy.<br />
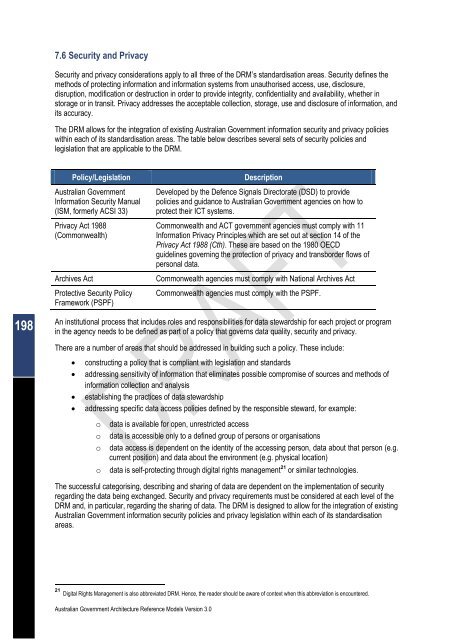
The DRM allows for the integration of existing <strong>Australian</strong> <strong>Government</strong> information security and privacy policies<br />
within each of its standardisation areas. The table below describes several sets of security policies and<br />
legislation that are applicable to the DRM.<br />
Policy/Legislation Description<br />
<strong>Australian</strong> <strong>Government</strong><br />
Information Security Manual<br />
(ISM, formerly ACSI 33)<br />
Privacy Act 1988<br />
(Commonwealth)<br />
<strong>Australian</strong> <strong>Government</strong> <strong>Architecture</strong> <strong>Reference</strong> <strong>Models</strong> <strong>Version</strong> <strong>3.0</strong><br />
Developed by the Defence Signals Directorate (DSD) to provide<br />
policies and guidance to <strong>Australian</strong> <strong>Government</strong> agencies on how to<br />
protect their ICT systems.<br />
Commonwealth and ACT government agencies must comply with 11<br />
Information Privacy Principles which are set out at section 14 of the<br />
Privacy Act 1988 (Cth). These are based on the 1980 OECD<br />
guidelines governing the protection of privacy and transborder flows of<br />
personal data.<br />
Archives Act Commonwealth agencies must comply with National Archives Act<br />
Protective Security Policy<br />
Framework (PSPF)<br />
Commonwealth agencies must comply with the PSPF.<br />
An institutional process that includes roles and responsibilities for data stewardship for each project or program<br />
in the agency needs to be defined as part of a policy that governs data quality, security and privacy.<br />
There are a number of areas that should be addressed in building such a policy. These include:<br />
� constructing a policy that is compliant with legislation and standards<br />
� addressing sensitivity of information that eliminates possible compromise of sources and methods of<br />
information collection and analysis<br />
� establishing the practices of data stewardship<br />
� addressing specific data access policies defined by the responsible steward, for example:<br />
o data is available for open, unrestricted access<br />
o data is accessible only to a defined group of persons or organisations<br />
o data access is dependent on the identity of the accessing person, data about that person (e.g.<br />
current position) and data about the environment (e.g. physical location)<br />
o data is self-protecting through digital rights management 21 or similar technologies.<br />
The successful categorising, describing and sharing of data are dependent on the implementation of security<br />
regarding the data being exchanged. Security and privacy requirements must be considered at each level of the<br />
DRM and, in particular, regarding the sharing of data. The DRM is designed to allow for the integration of existing<br />
<strong>Australian</strong> <strong>Government</strong> information security policies and privacy legislation within each of its standardisation<br />
areas.<br />
21 Digital Rights Management is also abbreviated DRM. Hence, the reader should be aware of context when this abbreviation is encountered.