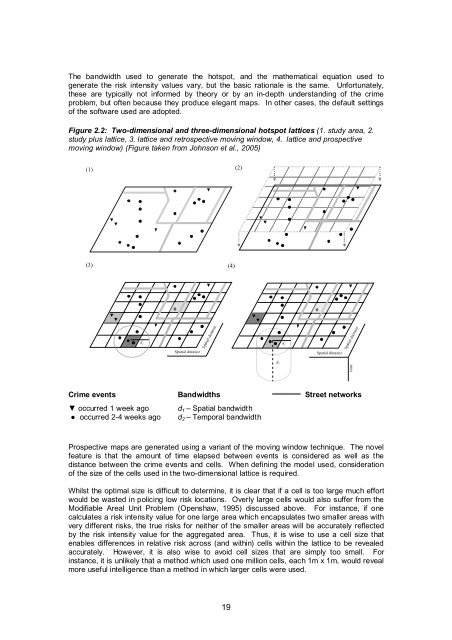
The bandwidth used to generate the hotspot, and the mathematical equation used togenerate the risk <strong>in</strong>tensity values vary, but the basic rationale is the same. Unfortunately,these are typically not <strong>in</strong>formed by theory or by an <strong>in</strong>-depth understand<strong>in</strong>g of the <strong>crime</strong>problem, but often because they produce elegant maps. In other cases, the default sett<strong>in</strong>gsof the software used are adopted.Figure 2.2: Two-dimensional and three-dimensional hotspot lattices (1. study area, 2.study plus lattice, 3. lattice and retrospective mov<strong>in</strong>g w<strong>in</strong>dow, 4. lattice and prospectivemov<strong>in</strong>g w<strong>in</strong>dow) (Figure taken from Johnson et al., 2005)(1) (2)(3)(4)d 1Spatial distanceSpatial distanced 2d 1Spatial distanceSpatial distancetimeCrime events Bandwidths Street networks▼ occurred 1 week ago d 1 – Spatial bandwidth● occurred 2-4 weeks ago d 2 – Temporal bandwidth<strong>Prospective</strong> maps are generated us<strong>in</strong>g a variant of the mov<strong>in</strong>g w<strong>in</strong>dow technique. The novelfeature is that the amount of time elapsed between events is considered as well as thedistance between the <strong>crime</strong> events and cells. When def<strong>in</strong><strong>in</strong>g the model used, considerationof the size of the cells used <strong>in</strong> the two-dimensional lattice is required.Whilst the optimal size is difficult to determ<strong>in</strong>e, it is clear that if a cell is too large much effortwould be wasted <strong>in</strong> polic<strong>in</strong>g low risk locations. Overly large cells would also suffer from theModifiable Areal Unit Problem (Openshaw, 1995) discussed above. For <strong>in</strong>stance, if onecalculates a risk <strong>in</strong>tensity value for one large area which encapsulates two smaller areas withvery different risks, the true risks for neither of the smaller areas will be accurately reflectedby the risk <strong>in</strong>tensity value for the aggregated area. Thus, it is wise to use a cell size thatenables differences <strong>in</strong> relative risk across (and with<strong>in</strong>) cells with<strong>in</strong> the lattice to be revealedaccurately. However, it is also wise to avoid cell sizes that are simply too small. For<strong>in</strong>stance, it is unlikely that a method which used one million cells, each 1m x 1m, would revealmore useful <strong>in</strong>telligence than a method <strong>in</strong> which larger cells were used.19
A further po<strong>in</strong>t of note concerns the trade-off between hav<strong>in</strong>g cells of small proportions, which<strong>in</strong>creases the precision of the maps generated, and the time taken to complete thecalculations. For <strong>in</strong>stance, the generation of a forecast for a grid which has 100m x 100mcells will take one-quarter of the time that it would take to complete the same task for a gridwhich conta<strong>in</strong>s cells that are 50m x 50m. Where analyses are required for an area the size of‘A’ Division, this can be of considerable importance. One issue then concerns the timelyproduction of the forecasts, a consideration whose importance will be amplified if the analysthas to produce forecasts with<strong>in</strong> a limited w<strong>in</strong>dow of time.The next issue concerns the bandwidth used. As is illustrated <strong>in</strong> Figure 2.2(4), Promap usestwo bandwidths. The first, the spatial bandwidth, may be calibrated <strong>in</strong> a variety of ways butshould relate to the distance over which the risk of victimisation is communicable.The second type of bandwidth concerns the time elapsed s<strong>in</strong>ce a <strong>crime</strong> occurred and theproduction of the forecast. This bandwidth is conditional upon the first, as a burglary eventshould contribute to the risk <strong>in</strong>tensity value of a cell only if it occurred with<strong>in</strong> a given distanceof that cell. As with the spatial parameter, for the temporal bandwidth a variety of sett<strong>in</strong>gscould be used but aga<strong>in</strong> this should reflect the period of time over which the communicabilityof risk can reasonably be expected to endure, or slightly longer.A further methodological difference between the authors’ approach and that used <strong>in</strong>retrospective hotspott<strong>in</strong>g lies <strong>in</strong> avoid<strong>in</strong>g use of the distance from the midpo<strong>in</strong>t of the cell andthe relevant burglary events <strong>in</strong> the derivation of the risk <strong>in</strong>tensity values. Consider that forretrospective hotspott<strong>in</strong>g a risk <strong>in</strong>tensity value is calculated for the midpo<strong>in</strong>t of the cell and thisvalue is then allocated to all other po<strong>in</strong>ts with<strong>in</strong> that cell. If risk <strong>in</strong>tensity values werecomputed for all po<strong>in</strong>ts with<strong>in</strong> a cell it is unlikely that they would be identical. Thus, us<strong>in</strong>g thevalue for the centroid of the cell gives the impression that the risk of victimisation is uniformacross the cell. This is unlikely to be true. This problem will be amplified as the cell size<strong>in</strong>creases. Instead of us<strong>in</strong>g the exact Euclidian distance between all events and the cellmidpo<strong>in</strong>t, for Promap the number of cells, the actual unit of analysis considered, between theevent and the cell is <strong>in</strong>stead used. Thus, if a <strong>crime</strong> occurred with<strong>in</strong> the cell underconsideration, the distance would be zero (actually, for computational reasons 1), if itoccurred with<strong>in</strong> an adjacent cell, two, and so on. By adopt<strong>in</strong>g this approach the risk <strong>in</strong>tensityvalues for each cell are likely to reflect more accurately the risks across the entire cell, ratherthan at one s<strong>in</strong>gle po<strong>in</strong>t. Formula (2) was used to derive the risk <strong>in</strong>tensity values for theprospective map, as follows:⎛ 1 ⎞ 1λτ( s)= ∑⎜1+ ∗ci ei c⎟(2)≤τ∩ ≤υ⎝ i ⎠ eiWhere,τ(s)bandwidthc i = number of cells between each po<strong>in</strong>t (i) with<strong>in</strong> the bandwidth and the celle i = time elapsed for each po<strong>in</strong>t (i) with<strong>in</strong> the temporal bandwidthλ = risk <strong>in</strong>tensity value for cell s τ = spatial bandwidth υ = temporalEvaluat<strong>in</strong>g the accuracy of the different methodsAs discussed <strong>in</strong> earlier work (e.g. Bowers et al., 2004), there has been little attention given tothe measurement of the accuracy of <strong>mapp<strong>in</strong>g</strong> techniques used to <strong>in</strong>form the deployment of<strong>operational</strong> resources. This is clearly essential. For this reason, <strong>in</strong> earlier papers the authorsproposed a number of different standard metrics. These <strong>in</strong>clude the hit rate, which is simplythe number of future <strong>crime</strong>s correctly identified. A second important factor is the area of the‘at risk’ locations to be policed. Where <strong>operational</strong> resources are limited, to compare twotechniques one may need to equate the latter to allow a like-for-like comparison. One way ofcontroll<strong>in</strong>g for this is to select the same geographic area for each method and then comparethe hit rate for each. Where possible this approach has been adopted <strong>in</strong> what follows. Arelated question concerns the area that should be selected with<strong>in</strong> which <strong>crime</strong> could occur. In20
- Page 2 and 3: 1. UCL JILL DANDO INSTITUTE OF CRIM
- Page 4 and 5: ContentsAcknowledgementsExecutive s
- Page 6 and 7: 2.5 Illustration of a simple neares
- Page 8 and 9: Project outcomesPatterns of burglar
- Page 10 and 11: those that involved collaboration w
- Page 12 and 13: 1. IntroductionThis report represen
- Page 14 and 15: optimally calibrated system, the go
- Page 16 and 17: e ij = n .j x n i.nWhere, e ij is t
- Page 18 and 19: Table 2.2: Knox ratios for Mansfiel
- Page 20 and 21: Table 2.6: Monte-Carlo results for
- Page 22 and 23: Table 2.10: Weekly Knox ratios for
- Page 24 and 25: Table 2.14: Monte-Carlo results for
- Page 26 and 27: Figure 2.1: The five policing areas
- Page 28 and 29: The results for area 5 again demons
- Page 32: a densely populated urban area this
- Page 35 and 36: Table 2.24: Average number of crime
- Page 37 and 38: Patrolling efficiencyAs discussed e
- Page 39 and 40: 3. Tactical options and selecting a
- Page 41 and 42: Selecting a pilot siteThe decision
- Page 43 and 44: Table 3.2: Tactical options matrixT
- Page 45 and 46: Type ofinterventionStudyUse ofintel
- Page 47 and 48: Other potential tactical optionsAt
- Page 49 and 50: 4. System development and evolution
- Page 51 and 52: the same time of day as each other
- Page 53 and 54: unfortunately, implementation or us
- Page 55 and 56: any tactical options were employed
- Page 57 and 58: the end of the pilot. In addition t
- Page 59 and 60: Figure 5.1: Promap dissemination pr
- Page 61 and 62: the busy schedule of the new Divisi
- Page 63 and 64: Tactical deliveryCommand Team daily
- Page 65 and 66: Table 5.3: Number of respondents wh
- Page 67 and 68: permitted, up to four plain clothed
- Page 69 and 70: observation made by those who used
- Page 71 and 72: A simple time-series analysis (see
- Page 73 and 74: Two approaches were used to compute
- Page 75 and 76: Figure 6.3: Changes in the proporti
- Page 77 and 78: Figure 6.5: Changes in the proporti
- Page 79 and 80: With respect to implementation real
- Page 81 and 82:
ReferencesAggresti, A. (1996) An In
- Page 83 and 84:
Johnson, S.D., Summers, L., and Pea
- Page 85 and 86:
Appendix 1. The information technol
- Page 87 and 88:
Figure A1.2: Stand-alone applicatio
- Page 89 and 90:
Recommendations that may be realise
- Page 91 and 92:
Section 1: knowledge and understand
- Page 93 and 94:
Extra Comments (please outline any
- Page 95 and 96:
In relation to the evaluation of in
- Page 97 and 98:
Time-series analysisFor the purpose
- Page 99 and 100:
Figure A3.1: Changes in the spatial
- Page 101 and 102:
Figure A3.2: Lorenz curves showing
- Page 103 and 104:
To recapitulate and elaborate, the
- Page 105 and 106:
Concluding comments on methodThe te
- Page 107 and 108:
Figure A5.2: An enlargement of the
- Page 109 and 110:
Figure A5.6: Prospective map magnif
- Page 111:
Produced by the Research Developmen