- Page 2 and 3:
Encyclopedia ofComputer scienceand
- Page 4 and 5:
C on t e n t sAcknowledgmentsivintr
- Page 6 and 7:
I n t r od u c t ion to t h eR e v
- Page 8 and 9:
Introduction to the Revised Edition
- Page 10 and 11:
Introduction to the Revised Edition
- Page 12:
Introduction to the Revised Edition
- Page 15 and 16:
AdaAdaStarting in the 1960s, the U.
- Page 17 and 18:
Advanced Micro Devices (AMD)Image P
- Page 19 and 20:
Algolgrammar of the data-descriptio
- Page 21 and 22:
ALUdown into component parts or bui
- Page 23 and 24:
10 Amdahl, Gene MyronShanahan, Fran
- Page 25 and 26:
12 analog and digitalhistory, bring
- Page 27 and 28:
14 Andreessen, MarcCompleted in 193
- Page 29 and 30:
16 animation, computerAndreessen tr
- Page 31 and 32:
18 APLAPL (a programming language)T
- Page 33 and 34:
20 application program interfacerat
- Page 35 and 36:
22 application softwareURL: http://
- Page 37 and 38:
24 arrayIn languages such as C that
- Page 39 and 40:
26 artificial intelligenceby tradit
- Page 41 and 42:
28 artificial lifewriters such as V
- Page 43 and 44:
30 Atanasoff, John VincentAtanasoff
- Page 45 and 46:
32 authoring systemsway”—the se
- Page 47 and 48:
34 awkthose found in C. There are a
- Page 49 and 50: 36 backup and archive systemsthe ec
- Page 51 and 52: 38 Backus-Naur formBackus-Naur form
- Page 53 and 54: 40 basic input/output systemdecisio
- Page 55 and 56: 42 Bell Laboratoriesand the early a
- Page 57 and 58: 44 Bezos, Jeffrey P.use if it is to
- Page 59 and 60: 46 bioinformaticsand a hierarchy of
- Page 61 and 62: 48 biometricsvariety of biometric s
- Page 63 and 64: 50 bitmapped imagesuch tasks as gra
- Page 65 and 66: 52 blogs and bloggingThe shift oper
- Page 67 and 68: 54 boot sequenceoperators (called B
- Page 70 and 71: oadbandTechnically, broadband refer
- Page 72 and 73: Brooks, Rodney 59such as Flickr and
- Page 74: ulletin board systems 61bugs and de
- Page 79 and 80: 66 CTotal = Total + 1;Total += 1;To
- Page 81 and 82: 68 C++While attracted to the advant
- Page 83 and 84: 70 calculatorthe location of the ca
- Page 85 and 86: 72 cascading style sheetsMojave Des
- Page 87 and 88: 74 CD-ROM and DVD-ROM“rapid proto
- Page 89 and 90: 76 censorship and the InternetIn 20
- Page 91 and 92: 78 central processing unitcentral p
- Page 93 and 94: 80 CGIIn a newly emerging sector th
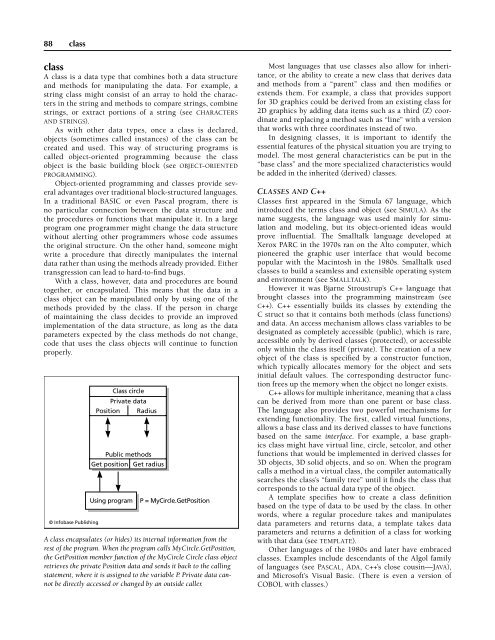
- Page 95 and 96: 82 characters and stringsAs compute
- Page 97 and 98: 84 chess and computersOne of the be
- Page 99: 86 chipsetattached to the silicon s
- Page 104 and 105: COBOL 91professional programmers. (
- Page 106 and 107: color in computing 93grams certainl
- Page 108 and 109: compiler 95as graphics file formats
- Page 110 and 111: computability and complexity 97As a
- Page 112 and 113: computer-aided instruction 99sumer
- Page 114 and 115: computer engineering 101Once a comp
- Page 116 and 117: computer games 103• stalking or h
- Page 118 and 119: computer graphics 105By the late 19
- Page 120 and 121: computer industry 107ket a variety
- Page 122 and 123: computer science 109PC World. Avail
- Page 124 and 125: computer virus 111programmed into a
- Page 126 and 127: concurrent programming 113Concurren
- Page 128 and 129: content management 115Web Conferenc
- Page 130 and 131: copy protection 117out to the volun
- Page 132 and 133: CPU 119In recent years the U.S. Dep
- Page 134 and 135: Cray, Seymour 121As with eBay, Crai
- Page 136 and 137: cyberlaw 123Available online [audio
- Page 138 and 139: cyberspace and cyber culture 125inv
- Page 140 and 141: cyberterrorism 127used for propagan
- Page 142 and 143: data acquisition 129For example, an
- Page 144 and 145: database management system 131menta
- Page 146 and 147: data communications 133Hellerstein,
- Page 148 and 149: data mining 135Further ReadingArimu
- Page 150 and 151:
data structures 137ture and termino
- Page 152 and 153:
decision support system 139data war
- Page 154 and 155:
Dertouzos, Michael L. 141While the
- Page 156 and 157:
developing nations and computing 14
- Page 158 and 159:
Diffie, Bailey Whitfield 145DHTML S
- Page 160 and 161:
digital convergence 147which allow
- Page 162 and 163:
digital rights management 149cent)
- Page 164 and 165:
disabled persons and computing 151p
- Page 166 and 167:
distance education 153disk array Se
- Page 168 and 169:
DNS 155Remote Method Invocation (Ja
- Page 170 and 171:
DNS 157NONPNRNTNUNZOMPAPEPFPGPHPKPL
- Page 172 and 173:
documentation, user 159In addition
- Page 174 and 175:
Dreyfus, Hubert 161gle computer) to
- Page 176 and 177:
DVR 163DSL uses special modems to c
- Page 178 and 179:
EeBayeBay Inc. (NASDAQ symbol: EBAY
- Page 180 and 181:
Eckert, J. Presper 167• There is
- Page 182 and 183:
education and computers 169Jupiter
- Page 184 and 185:
education in the computer field 171
- Page 186 and 187:
Eiffel 173As with private enterpris
- Page 188 and 189:
electronic voting systems 175Waugh,
- Page 190 and 191:
embedded system 177Instead, compani
- Page 192 and 193:
emulation 179Job Market Considerati
- Page 194 and 195:
encryption 181Public key encryption
- Page 196 and 197:
enterprise computing 183for alignin
- Page 198 and 199:
ergonomics of computing 185consisti
- Page 200 and 201:
expert systems 187On-line help and
- Page 202 and 203:
Ffault toleranceFault tolerance is
- Page 204 and 205:
file 191as dental and medical illum
- Page 206 and 207:
file transfer protocols 193a centra
- Page 208 and 209:
finite-state machine 195Masson, Ter
- Page 210 and 211:
flag 197• Hiding all the internal
- Page 212 and 213:
floppy disk 199flash drives contain
- Page 214 and 215:
Forth 201dows and Macintosh usually
- Page 216 and 217:
functional languages 203Page, Clive
- Page 218 and 219:
Ggame consolesGame consoles are com
- Page 220 and 221:
genetic algorithms 207by virtually
- Page 222 and 223:
globalization and the computer indu
- Page 224 and 225:
Google 211drives its proliferation.
- Page 226 and 227:
graphics card 213Industrial Competi
- Page 228 and 229:
green PC 215perceived by the human
- Page 230 and 231:
groupware 217In 1989 an open-source
- Page 232 and 233:
Hhackers and hackingStarting in the
- Page 234 and 235:
haptic interfaces 221Currently, han
- Page 236 and 237:
hashing 223third party) defragmenta
- Page 238 and 239:
hexadecimal system 225If not a prog
- Page 240 and 241:
history of computing 227electromech
- Page 242 and 243:
Hollerith, Herman 229embodying rela
- Page 244 and 245:
Hopper, Grace Murray 231Although th
- Page 246 and 247:
hypertext and hypermedia 233guage,
- Page 248 and 249:
IIBMInternational Business Machines
- Page 250 and 251:
identity in the online world 237dar
- Page 252 and 253:
information design 239Further Readi
- Page 254 and 255:
information theory 241the question
- Page 256 and 257:
Input/Output 243monitored the flow
- Page 258 and 259:
intellectual property and computing
- Page 260 and 261:
Internet 247I18n and L10n are somet
- Page 262 and 263:
Internet applications programming 2
- Page 264 and 265:
Internet service provider 251standa
- Page 266 and 267:
iRobot Corporation 253run the progr
- Page 268 and 269:
Java 255Next is a declaration for a
- Page 270 and 271:
Jobs, Steven Paul 257of Web service
- Page 272 and 273:
journalism and computers 259Markoff
- Page 274 and 275:
Joy, Bill 261Business_to_Business/C
- Page 276 and 277:
KKay, Alan(1940- )AmericanComputer
- Page 278 and 279:
Kleinrock, Leonard 265keyboardAltho
- Page 280 and 281:
Knuth, Donald 267istics or relation
- Page 282 and 283:
Kurzweil, Ray 269tial building of s
- Page 284 and 285:
Lanier, Jaron 271ings, and phrases
- Page 286 and 287:
legal software 273Development and T
- Page 288 and 289:
libraries and computing 275of techn
- Page 290 and 291:
Licklider, Joseph Carl Robnett 277L
- Page 292 and 293:
Linux 279of Sarah Y. He was arraign
- Page 294 and 295:
LISP 281At the 1956 Dartmouth Summe
- Page 296 and 297:
local area network 283edu/mc/LispNo
- Page 298 and 299:
loop 285to square :X :Y :Sizesetxy
- Page 300 and 301:
MMacintoshSince its inception in 19
- Page 302 and 303:
Maes, Pattie 289ing coding. However
- Page 304 and 305:
management information system 291sy
- Page 306 and 307:
marketing of software 293advocates
- Page 308 and 309:
mathematics software 295Mathematica
- Page 310 and 311:
McCarthy, John 297programming diffi
- Page 312 and 313:
medical applications of computers 2
- Page 314 and 315:
memory 301about prospective drugs a
- Page 316 and 317:
microprocessor 303ing system design
- Page 318 and 319:
Microsoft Corporation 305amount of
- Page 320 and 321:
Microsoft Windows 307• Windows Pr
- Page 322 and 323:
Microsoft Windows 309Here the vario
- Page 324 and 325:
military applications of computers
- Page 326 and 327:
MIT Media Lab 313Schein, Edgar H. D
- Page 328 and 329:
modem 315Author and Security Expert
- Page 330 and 331:
monitor 317cities. After the mixing
- Page 332 and 333:
motherboard 319that had a general-p
- Page 334 and 335:
MS-DOS 321duced the mouse to millio
- Page 336 and 337:
multiprocessing 323music and video
- Page 338 and 339:
music, computer 325program’s prio
- Page 340 and 341:
music and video players, digital 32
- Page 342 and 343:
NnanotechnologyOrdinary refining an
- Page 344 and 345:
netiquette 331Resources for Text, S
- Page 346 and 347:
netnews and newsgroups 333In the lo
- Page 348 and 349:
neural interfaces 335The growing ap
- Page 350 and 351:
nonprocedural languages 337tions),
- Page 352 and 353:
Oobject-oriented programming (OOP)D
- Page 354 and 355:
office automation 341so forth. Each
- Page 356 and 357:
Omidyar, Pierre 343Pierre Omidyar f
- Page 358 and 359:
online frauds and scams 345when ads
- Page 360 and 361:
online games 347sive gambling. Oppo
- Page 362 and 363:
online research 349sector jobs, and
- Page 364 and 365:
ontologies and data models 351onlin
- Page 366 and 367:
operating system 353tion programmer
- Page 368 and 369:
optical character recognition 355th
- Page 370 and 371:
OS X 357major competitor in busines
- Page 372 and 373:
Papert, Seymour 359Carr, David F.
- Page 374 and 375:
parsing 361sis.) A token is normall
- Page 376 and 377:
pattern recognition 363Turbo Pascal
- Page 378 and 379:
Perl 365Further ReadingAdobe Creati
- Page 380 and 381:
personal health information managem
- Page 382 and 383:
phishing and spoofing 369Jones, Wil
- Page 384 and 385:
photography, digital 371Jacobson, M
- Page 386 and 387:
PL/I 373ing for many users. PHP can
- Page 388 and 389:
pointers and indirection 375increas
- Page 390 and 391:
political activism and the Internet
- Page 392 and 393:
PostScript 379Polsson, Ken. “Pers
- Page 394 and 395:
printers 381Microsoft PowerPoint is
- Page 396 and 397:
privacy in the digital age 383cally
- Page 398 and 399:
programming as a profession 385Here
- Page 400 and 401:
programming environment 387that for
- Page 402 and 403:
project management software 389Nonp
- Page 404 and 405:
psychology of computing 391statemen
- Page 406 and 407:
Python 393Perl is still a popular s
- Page 408 and 409:
quantum computing 395dures and func
- Page 410 and 411:
queue 397To add an item, the tail p
- Page 412 and 413:
eal-time processing 399• RAID 1
- Page 414 and 415:
educed instruction set computer 401
- Page 416 and 417:
esearch laboratories in computing 4
- Page 418 and 419:
RFID 405TechniquesReverse engineeri
- Page 420 and 421:
Rheingold, Howard 407Glover, Bill,
- Page 422 and 423:
Ritchie, Dennis 409services to quic
- Page 424 and 425:
obotics 411human workers, such as i
- Page 426 and 427:
Ruby 413tor (the latter can combine
- Page 428 and 429:
SSAPSAP (NYSE symbol: SAP) is a Ger
- Page 430 and 431:
scheduling and prioritization 417Be
- Page 432 and 433:
scientific computing applications 4
- Page 434 and 435:
scripting languages 421of interest
- Page 436 and 437:
search engine 423AND, OR, or NOT. T
- Page 438 and 439:
service-oriented architecture 425Se
- Page 440 and 441:
shareware and freeware 427Along wit
- Page 442 and 443:
shell 429have achieved their greate
- Page 444 and 445:
simulation 431Further ReadingCharle
- Page 446 and 447:
Smalltalk 433progress is indeed exp
- Page 448 and 449:
smart card 435A smart house or buil
- Page 450 and 451:
smartphone 437birds, and bats. Some
- Page 452 and 453:
social impact of computing 439Strat
- Page 454 and 455:
social sciences and computing 441ta
- Page 456 and 457:
software engineering 443Padgham, Li
- Page 458 and 459:
Sony 445that has been stripped of c
- Page 460 and 461:
sorting and searching 447the one wi
- Page 462 and 463:
space exploration and computers 449
- Page 464 and 465:
speech recognition and synthesis 45
- Page 466 and 467:
spyware and adware 453spreadsheet h
- Page 468 and 469:
SQL 455Structured Query Language (S
- Page 470 and 471:
statistics and computing 457named L
- Page 472 and 473:
Stroustrup, Bjarne 459is that the u
- Page 474 and 475:
supercomputer 461by the 1990s the g
- Page 476 and 477:
Sutherland, Ivan Edward 463Simchi,
- Page 478 and 479:
systems programming 465network faci
- Page 480 and 481:
tape drives 467tape drivesAnyone wh
- Page 482 and 483:
TCP/IP 469The header fields and dat
- Page 484 and 485:
technical writing 471Further Readin
- Page 486 and 487:
telecommuting 473nents that were be
- Page 488 and 489:
terminal 475and they are not yet wi
- Page 490 and 491:
Torvalds, Linus 477texting and inst
- Page 492 and 493:
tree 479Some applications process t
- Page 494 and 495:
Turing, Alan Mathison 481Online att
- Page 496 and 497:
typography, computerized 483future,
- Page 498 and 499:
UNIX 485Vasilakos, Athanasios, and
- Page 500 and 501:
user-created content 487electromagn
- Page 502 and 503:
user interface 489Because a system
- Page 504 and 505:
VBScript 491The value of the memory
- Page 506 and 507:
virtual community 493Prencipe, Lore
- Page 508 and 509:
virtual reality 495organized in the
- Page 510 and 511:
von Neumann, John 497A regular tele
- Page 512 and 513:
von Neumann, John 499Eckert and Mau
- Page 514 and 515:
Web 2.0 and beyond 501powers Wales
- Page 516 and 517:
Web browser 503• platforms for us
- Page 518 and 519:
webmaster 505Amazon rain forest. In
- Page 520 and 521:
Web server 507What is the purpose o
- Page 522 and 523:
Weizenbaum, Joseph 509Access Protoc
- Page 524 and 525:
wikis and Wikipedia 511Walter Pitts
- Page 526 and 527:
wireless computing 513the encyclope
- Page 528 and 529:
women and minorities in computing 5
- Page 530 and 531:
World Wide Web 517• an extensive
- Page 532 and 533:
Wozniak, Steven 519Gillies, James,
- Page 534 and 535:
XML 521Eisenberg, J. David. “Intr
- Page 536 and 537:
young people and computing 523Finke
- Page 538 and 539:
ZZuse, Konrad(1910-1995)GermanEngin
- Page 540 and 541:
Appendix IBibliographies and Web Re
- Page 542 and 543:
Appendix IIA Chronology of Computin
- Page 544 and 545:
Appendix II 531•Eckert and Mauchl
- Page 546 and 547:
Appendix II 533••together with
- Page 548 and 549:
Appendix II 535base of knowledge. T
- Page 550 and 551:
Appendix II 537• An industry pund
- Page 552 and 553:
Appendix II 539favorite Web sites.
- Page 554 and 555:
Appendix II 541• Google and other
- Page 556 and 557:
Appendix III 5431977 John Backus:
- Page 558 and 559:
Appendix III 545Instruments scienti
- Page 560 and 561:
Appendix III 5471996 Shafrira Goldw
- Page 562 and 563:
Appendix III 5491991 Robert W. Floy
- Page 564 and 565:
Appendix III 551wider use of more p
- Page 566 and 567:
Appendix IVComputer-Related Organiz
- Page 568 and 569:
I n d e xBoldface page numbers deno
- Page 570 and 571:
Index 557Asymetrix Toolbook 32asymm
- Page 572 and 573:
Index 559chads 175, 392chairs, ergo
- Page 574 and 575:
Index 561Cybernetics of Control and
- Page 576 and 577:
Index 563Edelman, Leonard 316Edison
- Page 578 and 579:
Index 565PageRank algorithm of 57,2
- Page 580 and 581:
Index 567ISAM (Indexed Sequential A
- Page 582 and 583:
Index 569in chipset 86chips for 86,
- Page 584 and 585:
Index 571nerds 378nested loops 286.
- Page 586 and 587:
Index 573in client-server computing
- Page 588 and 589:
Index 575Representational State Tra
- Page 590 and 591:
Index 577Spitzer, Eliot 453spoofing
- Page 592 and 593:
Index 579Vvacuum, robotic 253vacuum