Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Kaspersky Internet Security 2012
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
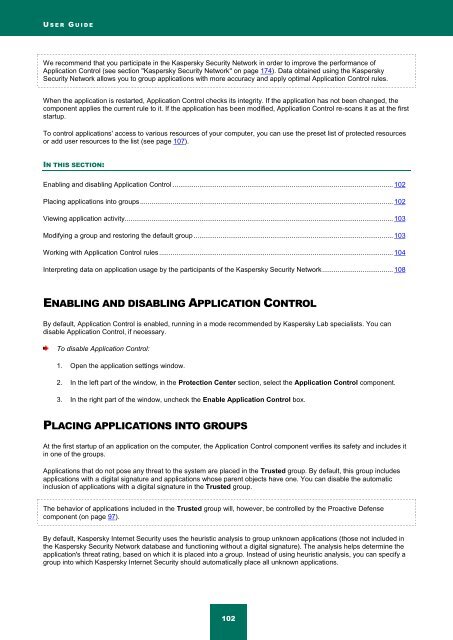
U S E R G U I D E<br />
We recommend that you participate in the <strong>Kaspersky</strong> <strong>Security</strong> Network in order to improve the performance of<br />
Application Control (see section "<strong>Kaspersky</strong> <strong>Security</strong> Network" on page 174). Data obtained using the <strong>Kaspersky</strong><br />
<strong>Security</strong> Network allows you to group applications with more accuracy and apply optimal Application Control rules.<br />
When the application is restarted, Application Control checks its integrity. If the application has not been changed, the<br />
component applies the current rule to it. If the application has been modified, Application Control re-scans it as at the first<br />
startup.<br />
To control applications' access to various resources of your computer, you can use the preset list of protected resources<br />
or add user resources to the list (see page 107).<br />
IN THIS SECTION:<br />
Enabling and disabling Application Control ................................................................................................................... 102<br />
Placing applications into groups .................................................................................................................................... 102<br />
Viewing application activity ............................................................................................................................................ 103<br />
Modifying a group and restoring the default group ........................................................................................................ 103<br />
Working with Application Control rules .......................................................................................................................... 104<br />
Interpreting data on application usage by the participants of the <strong>Kaspersky</strong> <strong>Security</strong> Network ..................................... 108<br />
ENABLING AND DISABLING APPLICATION CONTROL<br />
By default, Application Control is enabled, running in a mode recommended by <strong>Kaspersky</strong> Lab specialists. You can<br />
disable Application Control, if necessary.<br />
To disable Application Control:<br />
1. Open the application settings window.<br />
2. In the left part of the window, in the Protection Center section, select the Application Control component.<br />
3. In the right part of the window, uncheck the Enable Application Control box.<br />
PLACING APPLICATIONS INTO GROUPS<br />
At the first startup of an application on the computer, the Application Control component verifies its safety and includes it<br />
in one of the groups.<br />
Applications that do not pose any threat to the system are placed in the Trusted group. By default, this group includes<br />
applications with a digital signature and applications whose parent objects have one. You can disable the automatic<br />
inclusion of applications with a digital signature in the Trusted group.<br />
The behavior of applications included in the Trusted group will, however, be controlled by the Proactive Defense<br />
component (on page 97).<br />
By default, <strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> uses the heuristic analysis to group unknown applications (those not included in<br />
the <strong>Kaspersky</strong> <strong>Security</strong> Network database and functioning without a digital signature). The analysis helps determine the<br />
application's threat rating, based on which it is placed into a group. Instead of using heuristic analysis, you can specify a<br />
group into which <strong>Kaspersky</strong> <strong>Internet</strong> <strong>Security</strong> should automatically place all unknown applications.<br />
102